
The APRICOT 2026 keynotes during the Opening and Closing Plenaries traced a line from near‑term changes in operations, to long‑term data stewardship, to concrete migration steps enterprises can take towards IPv6 deployment.
The agentic shift: The Internet industry reimagined
Speaker: Mukhammad Andri Setiawan, Chief Information Officer, Universitas Islam Indonesia
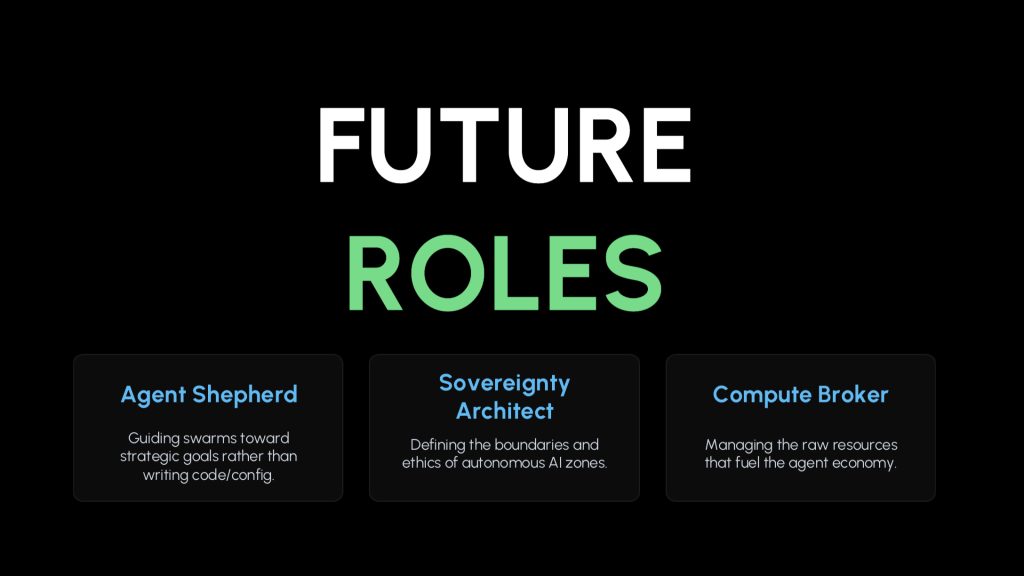
Andri Setiawan described how agentic AI is already changing daily operational practice: An agent is the first thing he installs on a virtual machine (VM), before handing off routine tasks (from firewalling to service configuration) in natural language. That reframes entry‑level ops work and raises questions about future roles. He floated new archetypes, like agent shepherd, sovereignty architect, and compute broker, which emphasize system‑level thinking over line‑by‑line configuration.
The talk examined cost, reliability, and autonomy. For many operators and institutions in our region, USD 20 a month is a significant outlay, and even then, subscription tokens run out. What happens if a vendor can no longer afford to subsidize access, or decides that local regulation is too difficult to comply with? Open source local models may seem like a good alternative, but come with tradeoffs in capability, management, and operational costs. On‑premises alternatives can be significantly more expensive once hardware, power, and cooling are considered.
Two takeaways stood out. First, engineers should keep moving up the stack toward architecture, policy, and assurance. Second, that network operators need shared patterns for safe use of autonomous agents — boundaries, ethics, and plans for service continuity if an AI dependency fails. As a reminder of the pace of change, Setiawan noted that a tool he had invested time in learning six months ago had become obsolete. What hasn’t changed, though, is the need for reliable network outcomes under resource constraints.
Slides: The agentic shift: The Internet industry reimagined
Internet History Initiative: Preserving our collective data legacy
Speaker: Jim Cowie, Founder, Internet History Initiative
Jim Cowie argued that the Internet’s “operational exhaust” — measurements, routing snapshots, DNS histories, logs, and the institutional memory behind them — is the evidence future researchers, policymakers, and practitioners will need to understand the Internet of today. Without intention and funding, this record evaporates: Servers are decommissioned, projects end, people retire, and data vanishes. He shared examples of historic datasets rescued on short notice, and asked the room to surface “endangered data” before it is too late.
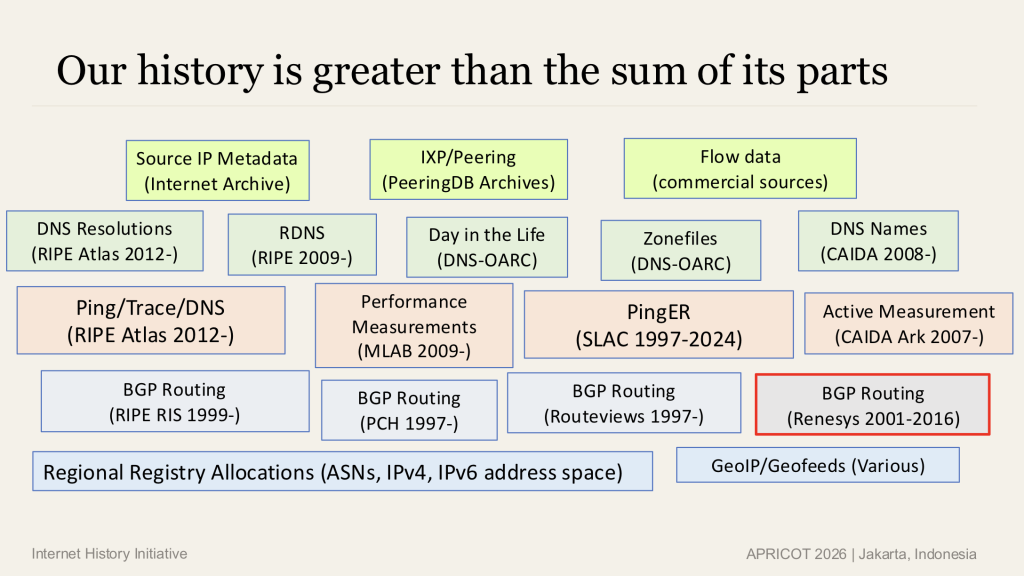
A rapid tour of early Internet history made the point that today’s architecture was not inevitable. In the early 1990s, there were live debates about packet vs circuit switching, and even a serious proposal to replace IP entirely, before the protocol won out. Email threads and discussions on mailing lists tell some of the story, and data and measurements from deployments make that story more accurate and complete. The record of decisions, measurements, and deployments — including in the Asia Pacific — must be preserved with proper metadata, provenance, and access.
Cowie’s work at the Internet History Initiative has two goals:
- Preservation: To collect as many Internet operational datasets as possible, with rich metadata, for long-term storage.
- Broadened access: A ‘working collection’ that researchers, educators, and LLM‑assisted tools can explore responsibly.
He suggested distributed stewardship (“lots of copies keep stuff safe”) and invited IXPs, NRENs, universities, and operators to host cold replicas, contribute legacy datasets, and include long-term retention of operational data in plans to sunset services.
Slides: Internet History Initiative: Preserving our collective data legacy
IPv6 in enterprise networks
Speaker: Jen Linkova, Network Engineer, Google
Consumer and access networks have pushed far ahead on IPv6. Many enterprises have not, and have gotten stuck on a transitional technology. Linkova pointed out that dual‑stack was never the finish line, as it increases operational surface, hides defects, and does nothing about IPv4 scarcity. The practical path she outlined is IPv6‑mostly and, where feasible, IPv6‑only for clients, using solutions like NAT64, DNS64 and CLAT to reach IPv4‑only services. In other words: Prefer IPv6, translate when necessary, and let clients signal capability so the network can disable DHCPv4 on demand.
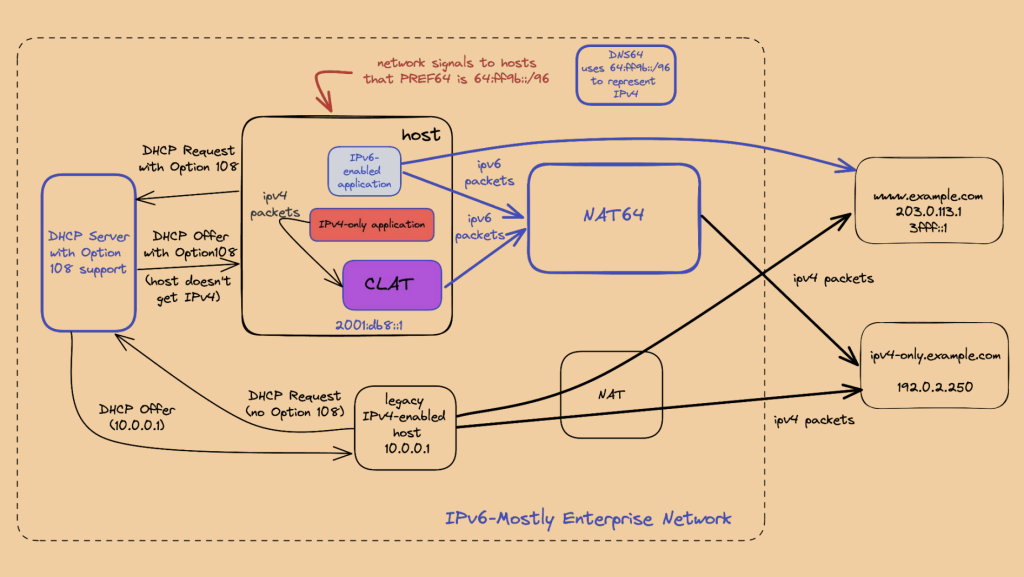
Key actions she highlighted:
- Use Happy Eyeballs behaviour to shield users, while finding and fixing latent IPv6 issues.
- Pilot IPv6‑mostly SSIDs and segments where engineers are present and ready with TCP dumps. Look for early wins on guest and public networks.
- Adopt the DHCPv4 signal for IPv6‑only preferred, allowing capable clients to switch off v4 gracefully — support is spreading across major platforms, with IPv6‑only Windows support in preview.
- Expect the main hurdles to be people and legacy applications. Choose pilots carefully, communicate early, and monitor for silent regressions when IPv4 is re‑enabled ‘just to test’.
Linkova suggested that operators can do the incremental work now, reclaim scarce IPv4 addressing where possible, and make IPv6 the default path so problems become visible and fixable.
Slides: IPv6 in enterprise networks
Agency and resilience
All three talks touched on agency and resilience. Setiawan’s agentic AI scenarios promise speed but raise new dependencies and governance needs. Cowie’s initiative asks the community to take custody of its own evidence. Linkova shows where operators can act immediately, with tools that already work at scale. Together, they argue that Asia Pacific operators can shape how automation is used, how history is saved, and how IPv6 becomes ordinary.
What you can do about it
- On automation: Publish patterns for safe agent use (approval gates, audit, rollback), share cost models for ‘subscribe vs self‑host’, and design for interruption.
- On preservation: Inventory datasets at risk, make plans to safeguard them. Coordinate with peers who hold complementary data. Host historical data.
- On IPv6: Pick one enterprise segment and run an IPv6‑mostly pilot with NAT64/DNS64 and CLAT; document exceptions. Shrink IPv4 use over time.
This year’s APRICOT keynotes asked us to automate with care, keep our shared memory alive, and ship IPv6 into holdout environments. To revisit the talks — or share them with colleagues — check out the APRICOT 2026 YouTube playlist.
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.
