
Hypertext Transfer Protocol Secure (HTTPS) is a secure extension of the Hypertext Transfer Protocol (HTTP).
HTTPS secures communications over the Internet, adding a layer of security for your data, by enabling encrypted communications between your browser and a website.
HTTPS protects the privacy and integrity of your browser-to-website communications, encrypting every data packet in transition using Transport Layer Security (TLS), which replaces the old Secure Sockets Layer (SSL) protocol. This protects your online shopping, banking and other personally sensitive online activities from man-in-the-middle and other types of online hacks and attacks.
How does HTTPS work?
All modern web browsers support HTTPS by default.
HTTPS collaborates with certificate authorities, which evaluate the security certificates of any accessed websites. This helps ensure that the website you are connecting to is the website you intended to connect to, without worrying that your connection will be hijacked by an attacker.
The HTTPS certificate can be authorized for a website by linking the information from a domain name, server name or host name. Domain certificates are preferred by most and issued by most domain registrars.
HTTPS wraps HTTP in an encrypted layer, TLS, hiding the information that is being sent between your browser and the webserver.
Your web browser will check the website’s security certificate, and verify that a valid certificate authority issued the digital certificate and that it exactly matches the URL in the address bar. Authorized certificate authorities include GoDaddy, Let’s Encrypt, GlobalSign and Digicert.
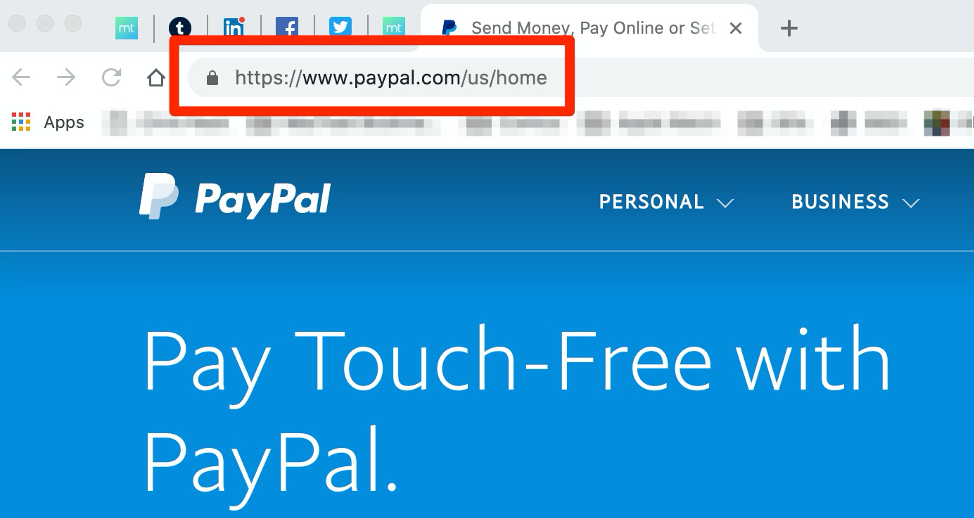
All of this ensures that when you see that little closed lock icon or see “https://” in your address bar, you are actually connected to the correct, secured website, and your personal information cannot be monitored in transit.
Why is HTTPS important?
As mentioned above, HTTPS adds an encrypted layer of protection, applying TLS to your browser’s communications with the website, which hides the information being sent back and forth, ensuring prying eyes cannot see the information.
HTTPS is important because HTTP comprises unencrypted ‘plain text’, which anyone that’s eavesdropping on a Wi-Fi network can intercept and view. This includes hackers, your Internet Service Provider (ISP) and government agencies, such as the NSA.
Read: HTTPS: why is it so popular?
This means that if you send sensitive information such as passwords or credit card numbers over HTTP, third parties could monitor, intercept and steal the information. HTTPS is what makes your browser interface a secure channel for shopping, banking, and other sensitive online activities possible.
This also comes in handy when you’re browsing other websites, such as Google. The search engine giant’s websites default to using an HTTPS connection, preventing other users (and your ISP) from monitoring your searches and other Google-related online activities.
In some economies, ISPs are allowed to monitor your online activities and then sell that information to interested third parties, such as advertisers. HTTPS prevents your ISP from monitoring your online activities. Sure, they can still see that you’re visiting Amazon, but they can’t see that you’re preordering the Baby Yoda figurine.
On sites that use only the insecure HTTP, your ISP could inject ads or other content, remove content or modify the page in other ways. Comcast has done this in the past by inserting bandwidth cap information into web pages users were viewing on its network.
While at first glance informational pop-ups such as this might appear to be a helpful feature, it, unfortunately, ’trains’ Comcast users to expect messages like this, enabling unsavoury websites to pop-up similar alerts, which could convince users to provide personal information that could include passwords, as well as credit card and account information.
Best ways to ensure you only access HTTPS web pages on websites
HTTPS Everywhere
HTTPS Everywhere is a security-centric browser extension that users can use with all the major browser platforms such as Chrome, Firefox, and Opera. The Tor Browser includes it by default.
HTTPS Everywhere is the result of a collaboration between The Tor Project and the Electronic Frontier Foundation. The extension ensures that your communication with web servers is encrypted by default when available.
Unfortunately, the extension is not available on Internet Explorer (IE) or Safari browser platforms directly from the EFF. However, there is an IE extension available that is based on the official HTTPS Everywhere extension. HTTPS Everywhere is also available as a Microsoft Edge browser add-on and is directly available from the EFF.
Safari users may want to take a look at the ’HTTPS Now for Safari’ extension, which provides similar functionality for Safari users.
Some websites offer limited support for HTTPS but make it difficult to use by defaulting to displaying unencrypted HTTP pages, or by including links to unencrypted content on encrypted pages.
The HTTPS Everywhere extension remedies these issues by rewriting page requests to these sites to use HTTPS.
Users of HTTPS Everywhere can choose to block any unencrypted requests — although this may cause issues with some sites. In this case, you can disable forced HTTPS for that site. You are strongly encouraged to contact the site’s developer and ask them to fix the HTTPS inconsistency. Fixing the issues is good for the site’s customers as well as its developers.
Tor Browser
The Tor Browser makes use of The Onion Router (that’s the ‘Tor’ in Tor Browser) network to anonymize your Internet browsing by bouncing it around a series of relays that volunteers around the globe set up and maintain.
Onion routing is named due to how it implements encryption in the application layer of a communication protocol stack, much like the layers of an onion. Tor encrypts the data sent and received by the browser multiple times, transmitting it via a series of randomly selected Tor relays.
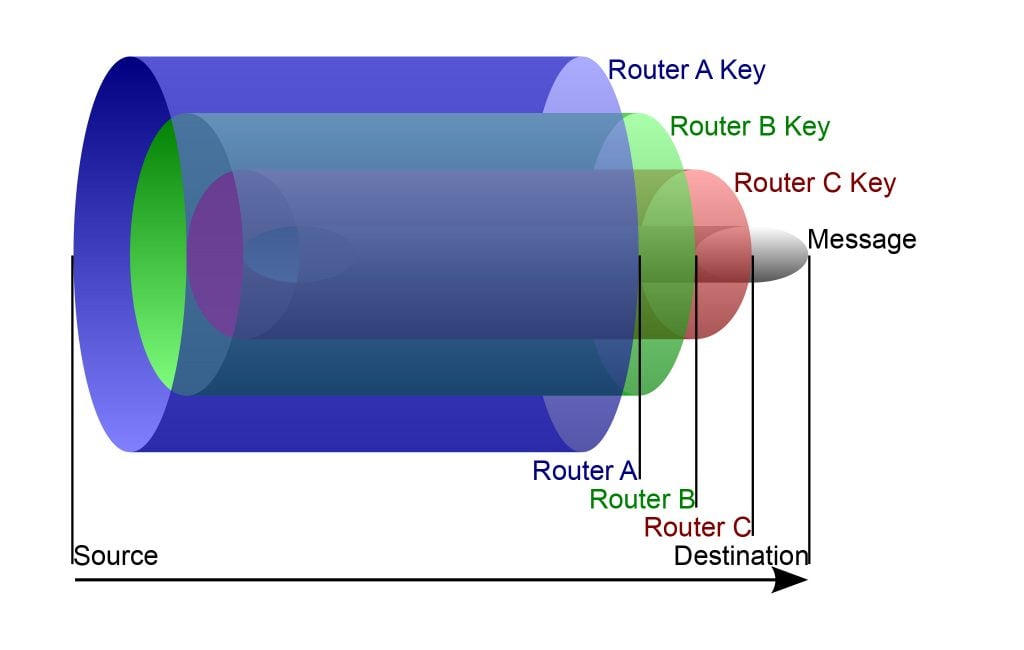
Each relay decrypts one layer of encryption and then passes the data on to the next relay. The final relay in the network decrypts the innermost layer of encryption, sending the original data without revealing the requestor’s IP address.
This onion layering prevents anyone from tracking a Tor Browser user’s Internet connection, preventing outsiders from learning the user’s physical location or from tracking which websites the user visits. This has come in handy, in particular, for activists and journalists located in economies where Internet traffic is closely monitored.
Note: Even if you are using the Tor Browser, it is still possible for your online activity to be monitored by the Tor network exit relay. Luckily, the Tor Browser has the HTTPS Everywhere extension installed by default, which will protect you, at least on websites that do offer HTTPS versions of their pages.
Other ways to encrypt your Internet traffic
Using HTTPS is only one of the ways to encrypt your Internet traffic. It should also be noted that HTTPS only encrypts your browser traffic — it does not protect all of your other Internet traffic, such as what other apps on your device generate. This leaves much of your Internet traffic open to being monitored.
Read: Understanding the limitations of HTTPS
Luckily, there are other ways to encrypt all of your Internet traffic.
Ensure encryption is enabled on home or office Wi-Fi Network
If your home or office Wi-Fi network is not protected by encryption enabled by a secure password, your online activities are left open to being monitored by anyone who is in the connection range of your Wi-Fi network.
By password-protecting your Wi-Fi network, you ensure that only authorized users can connect to the Wi-Fi hotspot. Password protection enables encryption of the Wi-Fi signal, hiding the online activities conducted while connected to the hotspot.
Encryption can be enabled on your Wi-Fi router’s administration interface. While each router make and model may vary when it comes to exactly how to password protect and encrypt your Wi-Fi network, it’s usually a matter of a few clicks of the mouse and a few strokes of your computer’s keyboard to enable the encrypted protection.
While the strongest encryption is provided by WPA3, the slightly weaker but more common WPA2 can also be used.
The lack of encryption is a well-known problem with public Wi-Fi hotspots. These hotspots usually do not require a password, as the idea is to make it as simple as possible for Internet users to quickly connect and use the Wi-Fi signal. That’s why it’s important to use a VPN when using a public Wi-Fi network. We’ll take a look at that in the next section.
Use a VPN
A Virtual Private Network (VPN) encrypts all of your Internet traffic, preventing your online activities from being monitored by your ISP, hackers, government agencies, and other nosy parties.
It uses government-grade encryption to protect your Internet connection and does so by encasing your connection in an encrypted link of sorts, hiding your Internet activities much like a highway or train tunnel hides the traffic on a road or railroad track.
This is especially useful when using unprotected Wi-Fi hotspots. These hotspots are popular targets for hackers that monitor the hotspot’s users’ connections in order to steal login information, as well as credit card numbers and banking information. A VPN’s encrypted protection prevents this from happening.
Read: Common setups to secure your networks from home
A VPN also offers the advantage of hiding your true geographical location. It does this by temporarily assigning a new IP address to your connected device, making it appear as if you are located somewhere else.
Some VPN providers can force a website to serve up HTTPS versions of their pages if they are available. This comes in especially handy for users of those browsers that do not have HTTPS Everywhere extensions available, such as Internet Explorer and Safari.
CyberGhost is one VPN provider that offers this feature. The forwarding to HTTPS pages is transparent to the user.
There are multiple ways to easily protect yourself online
HTTPS is an important part of online security, as it is encrypted protection for your in-browser communications, ensuring your online browser activities are kept safe from observation and data theft.
You should never conduct any kind of security-sensitive online activities, such as online shopping, banking or bill-paying unless the website you are connecting to uses HTTPS to encrypt your secure communications. I would strongly recommend that you never send a username and password to a website unless it uses HTTPS.
Users can force websites to provide HTTPS versions of their pages by using the HTTPS Everywhere browser extension, or by using a VPN that forces websites to provide HTTPS pages when they are available.
A VPN also comes in handy to encrypt all of your online communications, not just those conducted via your favourite browser. This is especially helpful when using unprotected Wi-Fi hotspots.
Users will also do well to protect their home and office Wi-Fi networks by requiring a strong password to connect and enabling strong encryption to protect all connections to the network.
By following these helpful tips, users can rest assured that their browser-based communications will remain secure and safe from observation by nosy outside parties.
Bill Hess is a Consumer Privacy Champion at PixelPrivacy.
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.
