
Sophisticated, high-profile cyberattacks regularly get a lot of media attention, and rightfully so, given the impact that they tend to have on business, politics and society.
That said, if we look closely at many of these attacks, most of the time the root cause is less sophisticated and malicious but rather a simple misconfiguration. A recent example of this was the exposure of Facebook user information from misconfigured public cloud storage.
Facebook User Info Exposed in Misconfigured Public Cloud Storage: Researchers from UpGuard have discovered two separate un-secured cloud storage buckets holding Facebook user information, once again putting the social network’s users at risk. https://t.co/AXZPbwFh4p
— eWEEK (@eWEEKNews) April 10, 2019
Security misconfigurations are one of the easiest targets for hackers because they’re so commonplace. This type of vulnerability includes weak or default passwords, out-of-date software, unnecessary features that are enabled, and unprotected files or databases.
Misconfigurations can happen anywhere from up and down the stack; from the software platform to the web, including application servers, databases, frameworks, and custom code layered on top. If just one of these is misconfigured, it creates an opportunity for intruders to find a way in, which can lead to a slow takeover or a wider breach.
Figure 1 shows a proof of concept pentest my organization did for a client showing 66% of vulnerabilities exposed were misconfigurations.
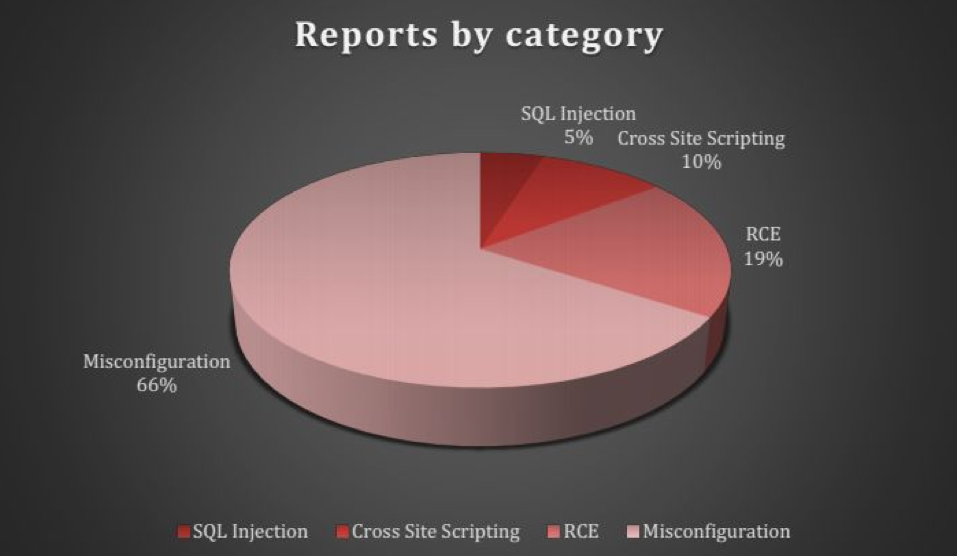
Figure 1 — Results from penetration test on a client’s network.
When we show similar graphs to sysadmin teams, their focus tends to gravitate towards the red segments — more often than not, they try to diagnose and fix these issues first.
This mentality to focus on the critical issues and ignore misconfigurations as ‘commonplace as long as the system is running smoothly’, is partly behind why misconfigurations have increased as a problem.
What do sysadmins need to do?
First, they need to pay more attention to misconfigurations. There are lots of open-source and free tools to find, monitor and fix these misconfigurations. Some common misconfigurations that can lead to security breaches include:
- Sensitive information disclosure
- Directory listing enabled
- Stack traces or debug mode enabled
- Outdated or unpatched software/hardware
- Default credentials
- Unnecessary features
- Unprotected resources
- Overly permissive policies
- CNAME record and unclaimed cloud resources
In Bangladesh, we have found 400+ vulnerable routers unpatched and vulnerable to CVE-2018-0171 and nearly 800+ vulnerable MIKROTIK devices to CVE-2018-14847 already infected by the COINHIVE miner.
Default credentials are also an issue in Bangladesh, with many ISPs and corporate networks keeping default credentials intact.
Unfortunately, there is no viable incident response team operating in Bangladesh which can respond or take the necessary steps to mitigate these identified issues, which is why sysadmins need to be more proactive in dealing with misconfigurations before they lead to an attack. The best form of defence is mitigation.
Shahee Mirza is the Head of Security Operations at Beetles Cyber Security Limited.
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.
