The Financials Information Sharing and Analysis Center Japan (金融ISAC), is the Japanese financial industry cybersecurity collaboration body. Currently, we have around 270 members.
One of the many activities carried out by F-ISAC JP is something we call “skill-up” working groups. “Skill-up” may not be the right English term, but it is used widely in Japan to explain training or education activities.
In November 2016, the skill-up working group organized a new style of training we call “CyberQuest”. This two-day training course simulates a real cybersecurity incident and gets participating F-ISAC JP members to respond to it.
How the training works
The training scenario was coordinated by a voluntary Red Team. They developed all the technical aspects, which were based on open source software or code written from scratch.
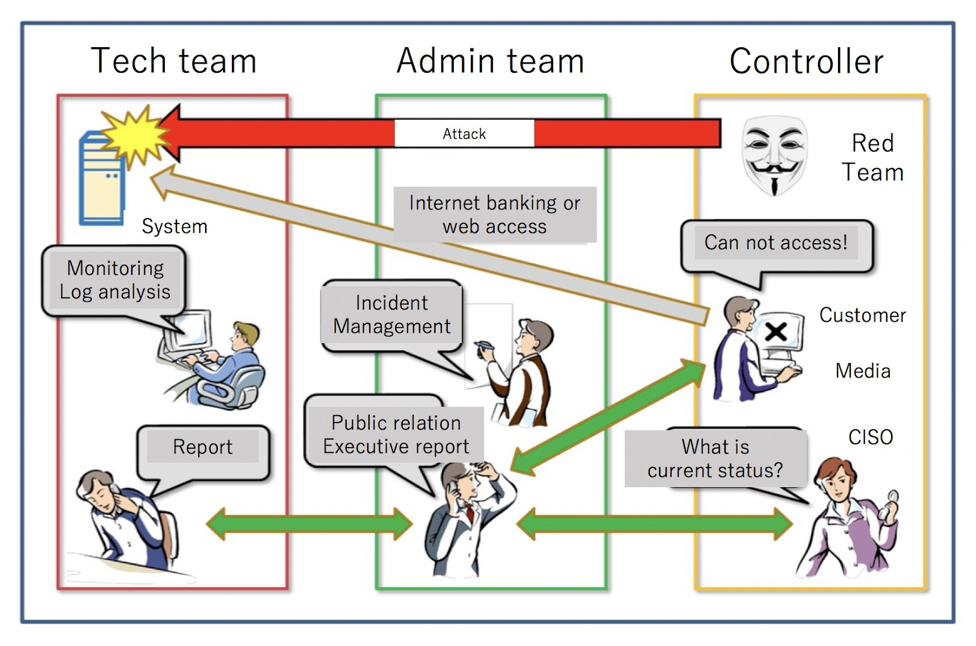
Participants are separated into two groups. The first group is the technical team responsible for hands-on, command line operations. The second group is the administration team that handles incident tasks, talks to the technical team and reports to a virtual Chief Information Security Officer (CISO).
Tech team tasks
- Install and build corporate Intranet, Internet banking, and corporate website.
- Receive attack from Red Team, then identify and analyze incident.
- Conduct malware analysis, forensic analysis, log analysis, packet analysis, and cooperate with the administration team to create reports for the CISO.
Administration team tasks
- Prepare for expected incident categories including malware infection, web-attacks, and DDoS attacks.
- Receive incident report from the customer and ask the tech team to do an incident investigation.
- Report to the CISO in a timely manner and conduct a press conference.
The diagram below gives a high-level overview of the interaction between the groups during the training.
Highlights of training content development
In this training, the technical team was expected to execute the tasks manually.
They had to install and set up a Linux or Windows operating system as well as several servers including an active directory, mail server, DNS server, web server, database server and application server.
Then they received a cyber attack mimicking real life, for which they were required to perform a real log or traffic analysis. The system design, attack code, infrastructure and incident response activities are the same as participants may experience in a true incident response. Participants are required to do a real technical analysis and report to the administration team.
The Red Team’s contribution and the commitment of the participating teams were critical to the success of CyberQuest 2016.
The feedback from participants was excellent, all of whom reported it as being “very useful” in relation to gaining experience in dealing with a real incident and realizing the need to prepare for such incidents, even if they had never had a serious cyber attack before.
You can find a movie of the training below and an article on the training featured in Nikkei. You can also read more about how Japan’s first Financial Services Information Sharing and Analysis Center was established and its other activities.
Keisuke Kamata is the Regional Director for F-ISAC, Japan and also a Board Member of Financials ISAC Japan.
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.