
The Domain Name System (DNS) is key to the modern Internet. The DNS translates between human readable domain names and IP addresses. Given the critical nature of the DNS it is designed to be scalable and resilient.
However, this resilience is jeopardized when configuration data is faulty; a common reason being lame delegations. In particular, a lame delegation occurs when a nameserver responsible for a domain is unable to provide authoritative information to translate human readable domain names to IP addresses.
Lame delegations can introduce both performance and security risks. As such, the prevalence of lame delegations is significant to better understand resilience in the DNS ecosystem.
Why do lame delegations matter?
Lame delegations can result in domains taking longer to resolve. Lame delegated nameservers will cause recursive resolvers to retry the query for the domain, retrying until it encounters a correctly configured nameserver.
Additionally, the queries to lame delegated nameservers represent additional load on the network, and at the incorrectly delegated nameserver. For example, incorrectly configured domains represent 12% of queries to GoDaddy nameservers: one out of eight queries received by a GoDaddy nameserver is a lame query, a query for which the GoDaddy nameserver is not authoritative.
Finally, lame delegations can also represent a potential security risk. In some cases, the lame delegations occur as a result of expired nameserver domains, allowing attackers to take control of the domain resolution by re-registering this expired nameserver domain.
Types of lame delegations
Lame delegated nameservers — nameservers unable to provide authoritative answers for a domain — can arise due to multiple reasons:
- It could be that the nameserver is unreachable or unavailable; the nameserver is not functional or the IP address for the nameserver is not routed
- The nameserver may be misconfigured or not authoritative for the domain. Consider a domain that lists the Google Public DNS Resolver (GPDNS) 8.8.8.8 as its authoritative nameserver. Given that GPDNS is a recursive resolver it cannot be an authoritative nameserver
- A nameserver could be lame delegated because it has no valid resolution path. The lack of a valid resolution path may be a result of missing glue or the nameserver domain expiring.
While the first two categories of lame delegated nameservers need active querying, this final category can be identified using passive analysis of zone files.
Read: Find bugs in your DNS zone files before deployment
We presented a paper at IMC 2020 called Unresolved Issues that investigates lame delegations using both passive analysis and active measurement. In this blog, we briefly describe our passive analysis before highlighting key findings and takeaways.
Identifying lame delegations using passive analysis
Using just zone files allows us to identify some lame delegations longitudinally, and at scale without the need to query actively. In our study we use zone files from nearly 1,250 TLDs across eight years that allowed us to uncover, in one case, a long-standing systemic issue causing lame delegations.
To identify lame delegations, we perform ‘static resolution’ of zone files. Using the NS, A, and AAAA records in zone files we find conservative estimates for when a nameserver was ‘resolvable’. Thus, if a domain lists an ‘unresolvable’ nameserver as its authoritative nameserver, then that delegation is lame.
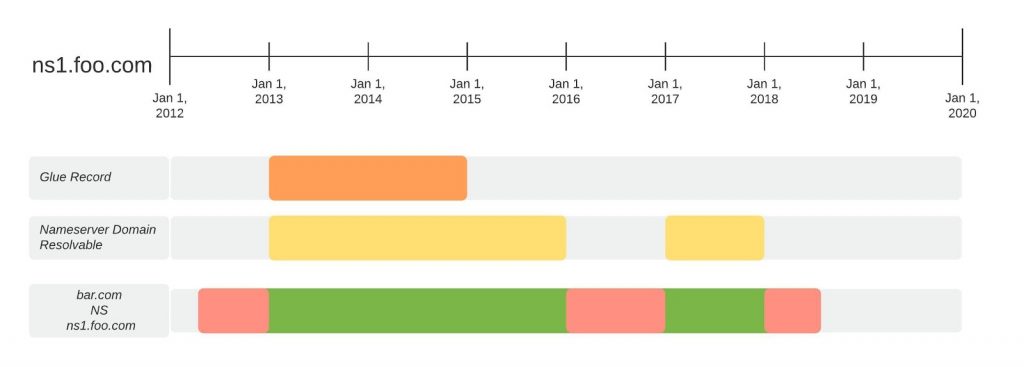
As an example, consider ns1.foo.com in Figure 1. The nameserver ns1.foo.com is used by the domain bar.com from mid-2012 to late 2018, so one expects the nameserver to be resolvable for this entire duration. The nameserver can either be resolvable if it has a glue record or if the nameserver domain foo.com has other resolvable nameservers. Using static resolution, we determine ns1.foo.com to be resolvable for two time periods. However, bar.com lists ns1.foo.com even when it is not resolvable, indicating bar.com was lame delegated for three distinct time periods. Note, we assume that the glue record listed is reachable and has a correctly configured nameserver.
For more details and specifics on static resolution, please refer to our IMC paper.
Findings and takeaways
We report our key findings and takeaways based on the longitudinal passive analysis of 499M domains and contemporaneous active measurements of 49M domains below.
.BIZ anomaly
In our passive analysis, we found nearly 50% of nameservers in .BIZ across eight years were lame delegated. In fact, nearly all of these nameservers never had a valid resolution path, indicating that domains start delegating to non-existent nameserver domains. On further investigation, we found that these lame delegations were a result of registrar practices to get around EPP constraints, and we identified eight registrars whose renaming practices put domains at risk of hijacking.
Zombie sinkholed domains: Conficker Working Group saga
Another interesting observation was the resurrection of sinkholed domains. Consider the example of the Conficker Working Group. The Conficker Working Group (CWG) sinkholed tens of thousands of domains associated with the Conficker Worm by pointing them to three nameservers controlled by the CWG. Unfortunately, these nameserver domains were allowed to expire, thereby enabling actors to register these nameserver domains and effectively control tens of thousands of domains. The CWG is one of many instances where sinkholed domains are allowed to expire. As such, it indicates that better long-term strategies need to be devised for sinkhole domains.
Contemporaneous lame delegations
Based on active measurements, we were able to identify a contemporaneous set of lame delegations. Based on that, we calculated the time taken to resolve the domains on average over a period of a month. We found that lame delegated domains take, on average, 3.7x longer than correctly configured domains to resolve. Additionally, we discovered that even popular domains had lame delegations.
In conclusion, our study found that lame delegations are prevalent, and in some cases created due to registrar operational practices. More importantly, we saw that lame delegations can persist for a long time if they have functional alternative nameservice. As such, the redundancy in DNS nameservice that helps domain availability can potentially hide broken delegations from domain owners. Finally, at times, lame delegations can become potential security risks, which can put the domain at peril.
This blog was possible due to the contributions of Mattijs Jonker, Raffaele Sommese, Geoffrey Voelker, Stefan Savage, and KC Claffy to the Unresolved Issues paper.
Gautam Akiwate is a PhD Candidate at UC San Diego. He primarily works on the intersection of security and large scale network measurements.
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.
