Established in the 1980s, Border Gateway Protocol (BGP) is the routing protocol used to interconnect and exchange routes in order to maintain a connected Internet. Like many of the Internet’s early, and still core, protocols and systems, security was not something that was initially included in its design. Only in the last 10-15 years have security extensions been developed and become best common practice.
In the case of securing the BGP, the Resource Public Key Infrastructure (RPKI) has recently become the preferred framework to protect against accidental route leaks, as well as to protect against malicious attacks. Recently, Pakistan network operators made great strides in improving the economy’s RPKI status, after extensive discussions with APNIC.
Change can start with a WhatsApp group
Twelve months ago, the Pakistan network operator community gathered in Karachi for the 35th South Asia Network Operators Group (SANOG) meeting, during which they heard from several local and international experts on the growing need for networks to secure their routes.
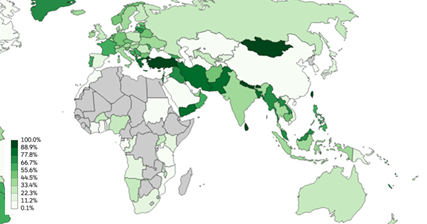
NOGs have played an important role in developing awareness of best current practices within the industry; their success stemming from them being community-led initiatives. This model has enabled certain community members, myself included, to take it upon ourselves to champion the use of RPKI within Bangladesh, Bhutan, Mongolia, Nepal, Sri Lanka and Taiwan, which are all exceeding 90% RPKI coverage.
Read: Local awareness and assistance is key to RPKI success
After joining APNIC and seeing how Internet communities in other economies work well together (through NOGs), I thought it would be great to bring together Pakistan operators for a common goal. Using my list of professional contacts from over 10 years in the ICT industry in Pakistan, I started a WhatsApp group for operators to join and ask questions about deploying RPKI on their network, and followed up with email and online remote sessions if they got stuck somewhere.
Contacts: Use personal and professional reference to contact the big operators and make them aware of how RPKI can secure their prefixes
Communication: Create a mailing list, WhatsApp group or use whatever tool that’s popular within the network operator community in your economy and invite everyone to join
Collaborate: Be on hand on offer assistance when it’s required. This requires a lot of effort, but you need to accommodate operators’ busy schedules
Carry on: Keep following up. The more you do this, the more operators will participate
Two key operators that benefited from and have helped expand this outreach are Pakistan’s largest broadband and mobile operators, PTCL and Jazz. PTCL’s decision to create Route Origin Authorization (ROAs) for its prefixes alone led to RPKI adoption in Pakistan to jump from 7 to 76% in March 2020.
Figure 2 — Pakistan’s RPKI growth.
For Yasir Ahmad, PTCL’s Manager of IP Core Network Operations, the personal support offered through the WhatsApp group and video calls helped to address their concerns.
“We recognized the need to secure and strengthen our IP domain in order to meet current ongoing challenges and to prevent route leaks and hijackings,” explained Yasir. “However, it’s always risky configuring route-objects; any mistake will stop traffic for many peers and customers.”
As the largest Internet Transit Provider for Pakistan and with millions of their own customers (most of whom have been stuck at home and reliant on the Internet for work and communication during the pandemic) even a small outage wouldn’t have been tolerable for PTCL.
“Having Yasir and the APNIC Training and Services teams walk us through the process in MyAPNIC, to make sure our whois details were up-to-date and that nothing would break when we created our ROAs, gave us the certainty we needed,” said Yasir.
Validation is the next step towards securing routes
Like PTCL, Jazz were also grateful for the assistance, especially when it came to cleaning up their whois details. This is an especially important step for organizations that are filtering for invalid routes based on prefix rather than using a validation tool like NLnetLabs’ Routinator 3000, RIPE NCC’s RPKI Validator 3, or Cloudflare’s OctoRPKI.
Read: How to install an RPKI Validator
Majid Iqbal, a specialist in Transport Planning in Jazz’s IP Team, said that while performing Route Origin Validation (ROV) and dropping invalid routes is a necessary step that Jazz is working towards implementing, they prefer prefix-based filtering for the moment as they educate their downstream customers.
“We are taking a personal approach, contacting each downstream customer individually and informing them of the importance of correctly creating ROAs for the routes they are announcing,” Majid said.
“We explain how this technology is helping minimize the impact of prefix hijacks or routing misconfiguration, and that they need to have valid ROAs so that once we and other upstream providers start performing ROV their traffic won’t be affected, nor will the Internet-based services that they’ve become reliant upon.”
Efforts like these by Jazz give us confidence that we’ll be able to continue to improve the current percentage of prefixes announced in the BGP covered by ROAs in Pakistan from 86% to 100% in the not too distant future, showing the world it is committed to no more accidental, nor malicious, Internet outages.
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.
