
In WiFi networks when a device sends a data packet, the receiving device sends an acknowledgement (ACK) back to the transmitter. This mechanism is deployed to deal with error prone wireless channels and to handle retransmissions in the physical and MAC layer. In particular, upon receiving a packet, the receiver calculates the cyclic redundancy check of the packet to detect possible errors. If the packet passes the check, then the receiver sends an acknowledgment to the transmitter to notify the correct reception of the data packet.
Since most networks use security protocols (such as WPA2) to prevent unauthorized devices from joining, one may assume that a WiFi device only acknowledges packets received from the associated access point or other devices in the same network.
Surprisingly, we have found that all today’s WiFi devices acknowledge any packet they receive as long as the destination address matches their MAC address.
The physical layer acknowledges all packets, even those without any valid payload, although higher layers eventually discard the fake packet.
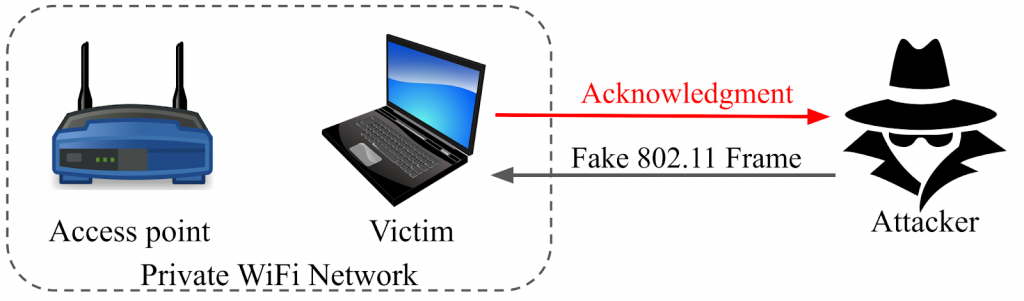
Consider a scenario where a client device is connected to an access point, as shown in Figure 1. This is a private network secured by protocols such as WPA2. We have found that if an attacker sends a fake and unencrypted 802.11 packet to the client device (labeled as victim), the client device sends back an acknowledgment!
We call this behavior Polite WiFi because WiFi devices respond to any stranger with an acknowledgement.
Testing the politeness of WiFi
We examined a few different WiFi devices in our lab and found that they were all vulnerable to Polite WiFi behavior.
To extend this experiment to thousands of devices, we mounted a WiFi dongle on the roof of a vehicle and drove around the city to test all nearby devices. For the WiFi dongle, we used a Realtek RTL8812AU USB WiFi dongle connected to a Microsoft Surface, running Ubuntu 18.04. We developed a multi-threaded program using the Scapy library to discover nearby devices and sent fake 802.11 packets to the discovered devices, then verified that target devices responded to our fake packets.
Read: How consumer IoT devices expose information
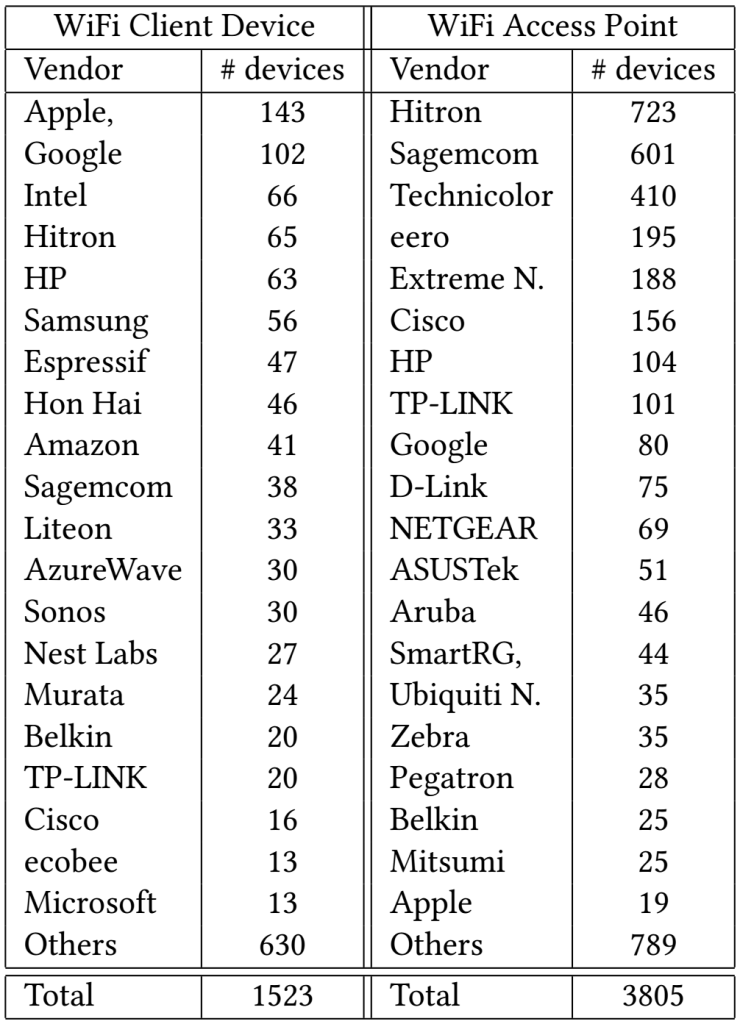
We performed this experiment for one hour while driving around the city of Waterloo, Ontario, Canada. In total, we discovered 5,328 WiFi nodes from 186 vendors, 1,523 different WiFi client devices from 147 vendors, and 3,805 access points from 94 vendors.
Table 1 shows the top 20 vendors for WiFi devices and WiFi access points in terms of number of devices discovered in our experiment. The list includes devices from major smartphone manufacturers (such as Apple, Google, and Samsung) and major IoT vendors (such as Nest, Google, Amazon, and Ecobee).
We found that all 5,328 WiFi Access Points and devices responded to our fake 802.11 packets with an acknowledgment. Therefore we can assume most modern WiFi devices and access points are vulnerable to Polite WiFi.
Potential threats from Polite WiFi
Polite WiFi behaviour creates many threats. For example, an attacker can send back-to-back fake packets to a victim device. Then, it can analyze the signal of the received ACKs to infer some personal information about the victim.
Recent studies have shown that by monitoring WiFi signals, one can infer some information about the environment such as localization, gesture recognition, breathing rate estimation, and keystroke inference. Hence, the attacker can exploit these systems and use the signal of ACKs to infer some personal information.
Read: How to detect IoT devices in a network
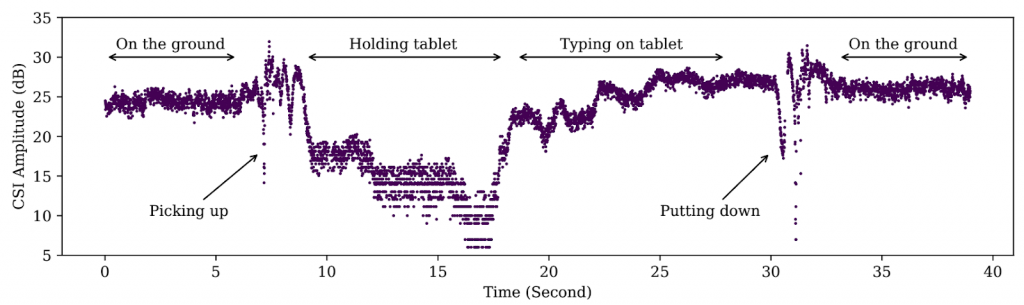
To evaluate the feasibility of this attack, we conducted an experiment in which we tried to infer information from a target device; in this case, a Microsoft Surface Pro tablet. We placed an attacker device in a different room and implemented the attacking mechanism on an ESP32 WiFi module. The attacker had no access to the victim’s network nor did it have the secret key of this network. The attacker sent fake 802.11 packets to the target device, and measured the signal of received ACKs.
Figure 2 shows the amplitude of the signal received from the target device. As can be seen, when the tablet is on the ground, the signal amplitude is very stable. However, as soon as a user approaches the device and picks it up the amplitude experiences large fluctuations.
Next, the user holds the tablet for about 10 seconds and then starts typing for about 10 seconds. It is very clear that the pattern of just holding the tablet and typing are very distinct.
This experiment shows that one can potentially reveal privacy-sensitive information by using Polite WiFi. An attacker can send fake packets to the devices inside a building to infer various information (about what is happening inside that building) by measuring changes in the signal of responses received.
We believe that there are still many open questions that require future study. Can an attacker detect occupancy? Can an attacker detect the activity of people inside a building? Or can an attacker estimate vital signs such as heart rate and breathing rate of people from the signal of their WiFi devices?
Dr Ali Abedi is a lecturer in the School of Computer Science at the University of Waterloo. His research interests lie primarily in the areas of wireless networking and low-power communication for IoT devices.
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.
