
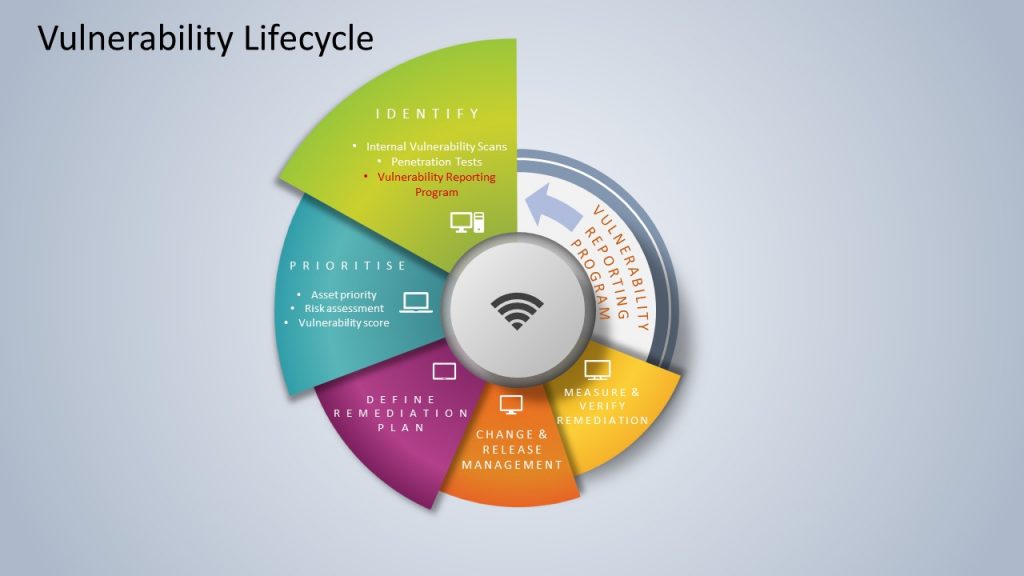
Today APNIC is announcing a formal Vulnerability Reporting Program that aims to provide guidance to security researchers who find bugs or weaknesses in any of APNIC’s services.
While APNIC has always welcomed reports of potential security issues, the introduction of this new program lays out a direct email address for the APNIC Computer Security Incident Response Team (CSIRT), what information we would like to see in a detailed report, and guidance on what is ‘In Scope’ and ‘Out of Scope’ for testing.
APNIC has also taken a further step by including a ‘Safe Harbour’ statement, which gives security researchers additional assurance that any security testing performed within the program’s guidance will be seen as authorized and lawful. This is a concern for many researchers, as there have been cases where companies have filed lawsuits against security researchers who discovered vulnerabilities and were attempting to report them in good faith.
This program is one aspect of APNIC’s ongoing proactive security program and will help improve the security of APNIC products and services.
Additionally, APNIC has implemented a proposed Request for Comment (RFC) for describing our Vulnerability Reporting Program through the use of a security.txt file. Read more about the security.txt format and the proposed RFC. You can also access APNIC’s security.txt.
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.
