
This post is the first in a three-part series summarizing recent efforts towards protecting Internet geolocation services from manipulation.
Internet geolocation is the process of learning the geographic location of an Internet-connected device. Geolocating a client (such as a browser accessing a website) can be useful for location-aware authentication, access control, online voting, social networking and fraud reduction. Geolocating a remote server can provide higher assurance of the server’s identity – important when justifying critical transactions, such as those that require data sovereignty.
Geolocation is often targeted for manipulation in order to impersonate (if location is used to reinforce authentication) or other location-dependent benefits, such as access to copyright-protected media and localized news.
We will look at Client Presence Verification and Server Location Verification as techniques for verifying geographic locations of clients and servers in real time over the Internet. Each technique addresses a wide range of tactics for manipulating geolocation, including IP-hiding technologies such as VPNs and anonymizers.
Geolocation techniques
Most current geolocation relies on the client’s IP address or the GPS coordinates of a hand-held device. For web applications, the Geolocation API is a W3C standard that enables browsers to get location information about the client device and communicate it to a web server. The Javascript example below shows how a webpage would request the client device’s location.
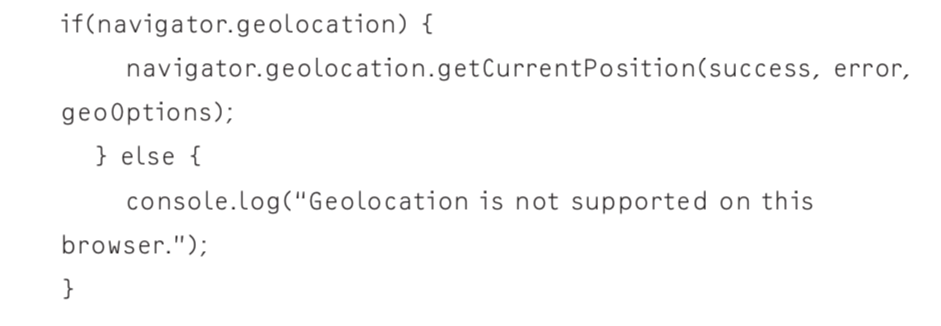
Figure 1 – Accessing the Geolocation API using Javascript.
The methods by which location is discovered varies by browser. Most major browsers rely on the following methods: GPS, WiFi Positioning System (WPS), IP-address-based location lookup, and cell-tower triangulation. The method used differs by browser too, and if the preferred method fails, the next will be tried.
The geographic location of an IP address can be learned from publicly available routing information, or public registries such as whois. Many location service providers maintain lookup tables to instantly map IP addresses to locations. Although it can often take a long time for changes to be updated, this kind of static tabulation is often reliable enough for benign server geolocation. Flagfox is an example of a browser extension that uses IP address-based geolocation to display a flag of the economy corresponding to the server’s location.
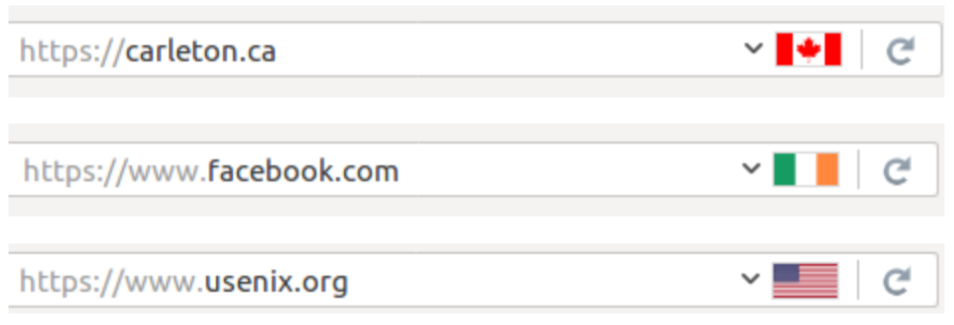
Figure 2 – Snapshot of the Flagfox browser extension, which displays the flag of the economy corresponding with the location of the server’s resolved IP address.
None of the above techniques are resilient to manipulation, however. Generally, the server trusts the coordinates communicated to it by the browser, which in most cases can easily be forged. Firefox extensions such as Fake Location and Location Guard both enable this kind of forgery, enabling a user to specify the location they wish to appear to be in. If the server relies on tabulation methods instead of asking the browser, the use of proxies and anonymizers comes into play.
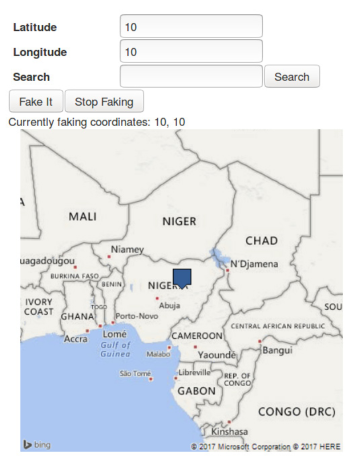
Figure 3 – Snapshot of the Fake Location extension.
Many other techniques can be used to help a server infer a client’s geographic location, such as using hints obtained from HTTP headers, like preferred language or time zone. A device’s location can also be interpolated from its proximity to nearby devices with known locations, such as WiFi access points.
Network measurement-based techniques aim to locate devices (clients or servers) by estimating their distance from landmarks in a network with known locations. The network delay to or from a network landmark is measured, then mapped to a geographic distance. This form of mapping is not nearly as accurate as GPS satellite-based measurement but is considered more accurate than the IP address-based tabulation approach.
Network measurement-based methods are also vulnerable to evasion. Delay-increasing attacks can distort the perceived location of a client or server, and delay-decreasing attacks can be performed by issuing fake ICMP echo replies. Combining both attacks, an adversary can forge the calculated location to an accuracy of a few tens of kilometres relative to the desired target location.
This post was adapted from an article that featured in ;login: titled “Secure client and server geolocation over the Internet”.
AbdelRahman Abdou is a Postdoctoral Researcher in the Department of Computer Science at ETH Zurich, Switzerland. His research interests include location-aware security, SDN security, and using Internet measurements to solve problems related to Internet security.
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.

A nice topic that most of us wanted to talk about, how a web service tracked our location.As the article says it has lot of advantages from the service providers end, but is it the same for the client. Some years back, when I was searching something on the google I noticed the location parameter for the first time and wondered how it exactly showed where I was. I was surfing using my desktop firefox client and internet connection was a traditional ADSL which ISP data even points to some where else in the country. But the location on the google page was precise. This haunted me for hours thinking how it worked so well. Then I realized that I was logged in to google from my android phone which was in home wifi and google connected the dots and my location was shared among every device I was logged in.
Thinking it will put my privacy at risk I tried to find how to stop being tracked. But there was no single point where I can switch off this feature.
Confirming server location is good to identify where we are accessing, also at the same time most browsers and multi-platform services defaults to send the user location to the server side as well. Browsers asks to share the location but still if we deny it, servers can figure out where it is been accessed.
So from my point of view this has both its pros and cons. For individuals like me, can consider this as a risk to our privacy while services like Google or Facebook can argue that they can provide better service by getting to know the location.
Also, as the article says, faking the location is a big problem when there are services targeting specifically the location, it will badly affect the location based marketing as well. But still I think sharing my location or at least my country location will put me at risk in doing modern day to day networking. As Google sends us customize ads, an attacker can also send us a custom phishing mail based on our location. A torrent seed or Tor bridge can be easily pointed out and owner may get sued … and the list will go on…
~Just a thought…