
The exponential growth of client devices like smartphones, tablets, and wireless Internet of Things (IoT) is increasing the demand for Wi-Fi network infrastructure and with it the risk of security vulnerabilities.
In this series, I examine the risks associated with the three most popular Wi-Fi network categories (listed below), and what users can do to manage these.
- Residential, Home, SOHO (Small Office/Home Office) Wi-Fi networks
- Public Wi-Fi networks (coffee shops, libraries, shopping malls, hospitality market, outdoor hot spots provided by telcos or ISPs)
- Enterprise level Wi-Fi Networks (internal staff and guest network access)
Residential, Home, SOHO Wi-Fi networks
Typically, these are Wi-Fi access points (AP) installed by the owner (for example, behind a cable/ ADSL modem), or an ISP.
In 95% of cases, these APs have a maximum-security level of WPA2-PSK + CCMP/AES (Wireless Protected Access version 2 with Pre-Shared Keys and using the Advanced Encryption Standard). This means that the password is stored on the AP itself and, hopefully, this encryption standard is used in residential environments.
Unfortunately, we still see APs with open authentication or with shared key authentication, either with no security at all or Wired Equivalent Privacy (WEP) – a security encryption methodology that has been compromised for a long time. WPAv1-PSK + TKIP/RC4 has the same weaknesses as WPAv2-PSK CCMP/AES, as I’ll explain below.
Another disadvantage of using WEP and WPAv1 TKIP/RC4 is that the speed (data rate) cannot go higher than 54 Mbps – at least WPA2 is needed to achieve higher speeds used by IEEE 802.11n and IEEE 802.11ac standards.
Also, it might be that Wi-Fi Protected Setup (WPS) is still active on the AP – this latter method connects devices via Push Button Connection (PBC), PIN-code, token card or Near Field Communication (NFC). WPS has been compromised as well and should be turned off, as it can be another backdoor via the AP to the network.
Security risks to be aware of
There are several security risks that can jeopardize your network. These include:
- If the password or passphrase is weak, then a password dictionary attack can be done (basically capturing the authentication of the end-user and verifying it with words of the dictionary or a file created with commonly used passwords).
- Sometimes the ISP provides the password/passphrase which is based on the MAC-address (Media Access Control, the hardware address of the device) and use that in the Service Set IDentifier (SSID) to propagate the network. Unfortunately, there is an algorithm that can be used to figure out what the password is.
- Social Engineering, which is a way of just asking for the password via phone or email – possibly the simplest way to get a password.
- Guests that visit your house who use your Wi-Fi may save your Wi-Fi password on their devices, which may be more easily hacked than your own device.
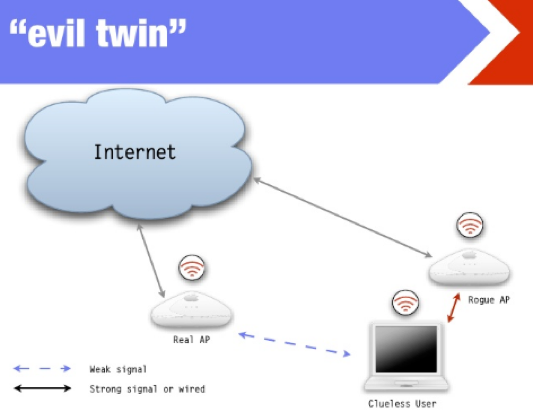
- Most households use WPAv2-PSK CCMP/AES, otherwise, there would be other risks like the evil twin attack. Client devices do not know the difference and might connect to the so-called rogue AP.
What is an Evil Twin Attack?
An Evil Twin Attack is when a hacker sets up an AP with the same name of a legitimate AP in the same vicinity to trick users to choose the compromised AP.
Imagine you’re at a coffee shop with W-iFi access. The SSID of the coffee shop’s AP is “CoffeeBean”, which you select and connect to via your laptop or smart device’s Wi-Fi network settings.
If a hacker sets up a different AP in the same vicinity and also calls it “CoffeeBean” you or your device may unintentionally choose this rogue AP instead of the real AP, especially if the rogue AP sends a stronger RF signal than the real AP (Note: in the list of Wi-Fi networks you’ll only see one “CoffeeBean” option, which will be the one with the strongest signal).
If this rogue AP also has a connection to the Internet, then the end-user has no clue if they are connecting via the hacker’s AP or the coffee shop’s AP.
- Other devices can also impact connections to the AP intentionally (radio frequency jammers) or unintentionally (microwave ovens and Bluetooth devices).
- There are tools that can extract the password/passphrases from the device itself (thus from the smartphone, tablet or laptop).
Note: In cases where the password or passphrase is known, then the content of these Wi-Fi packets can be captured by a protocol analyzer.
How can you protect yourself from such risks?
End-users can protect themselves by becoming better educated on extra security measurements they can take. Such measures include:
- Selecting a password or passphrase as long as possible with uppercase, lowercase and special characters. Most importantly do not write it down on a piece of paper or post-it note and stick it under your keyboard or hang it on the wall.
- Not giving access to your device, for example, watch out for USB-sticks automatically starting a script to extract passwords or passphrases.
- Check your software if there are more APs with the same SSIDs. If you have more than one in your home it is okay for roaming purposes, but if you have only one, then there should be one unique SSIDs. You can check this with reconnaissance tools like Acrylic WiFi, inSSIDer, Wi-Fi inspector on Windows, Wifi analyzer on Android or WiFi Explorer for Apple.
- Turning-off WPS if it is still enabled on the AP. You can use one of the reconnaissance tools mentioned above, to check if WPS is still active.
- Changing the SSID to a unique SSID, if required.
- Configuring your AP to a proper channel (for example, in 2.4 GHz, channel 1, 6 or 11 and in 5 GHz, 36, or 40) to make sure there is not too much overlap with other APs. You will need a spectrum analyzer (typically used by Wi-Fi professionals) to check for interference from other devices, like microwave ovens or Bluetooth devices.
- Using secure protocols at higher layers in the OSI-model, for example, IPSEC at layer 3 to create Virtual Private Network tunnels, or HTTPS at layer 7 to create secure web connections.
- Checking with your ISP if they provide a second logical Wi-Fi network for their customers that allows you to log in at other so-called “home-spots” propagating the same network (SSID) so when you travel you can make use of these SSIDs. In this case, the username and password are stored at the data centre or in the cloud by the ISP.
In my next post, I will look at the risks for Public Wi-Fi networks (coffee shops, libraries, shopping malls, hospitality market, outdoor hot spots provided by telcos or ISPs).
Ronald van Kleunen is CEO of Globeron Pte Ltd. He is a certified wireless network expert and certified security professional.
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.

Due to the growing incidents of hacking and other cyber breaches, it is now more important than ever that businesses should strengthen their IT infrastructure, especially the routers and Wi-Fi access points. For businesses, I would recommend virtual private networks.