
I first learned about the Modern Honeypot Network (MHN) at the ThreatStream booth while I was attending the FIRST.org Annual Conference and AGM in Boston last June.
As a seasoned ‘honeypotter’ (don’t bother to look this up folks!) and someone who has been deploying honeypots and honeynets, I really liked the idea behind MHN. It simplifies the efforts that are required for deploying and monitoring multiple honeypot sensors. And it is free and open source too!
Behind the scenes, MHN consists of many open source projects and scripts that glue everything together. You can right away get the popular honeypot tools for observing different types of attacks such Kippo, Dionaea and Glastopf. Worth mentioning also is the integration data sharing and presentation tools such as hpfeeds and honeymap.
The project is also available on Github and there is a mailing list where Jason (ThreatStream) patiently answers questions from everyone. Making the project available on Github also means that you are more than welcome to fix or add a feature or two yourself (instead of just complaining 🙂 )
So, finally this month I managed to get MHN up and running in our research network. Now I have about 10 honeypot sensors running inside a couple of Linux instances (mostly Ubuntu 14.04.1 inside Linux containers – LXC). Check out some of the screenshots below:
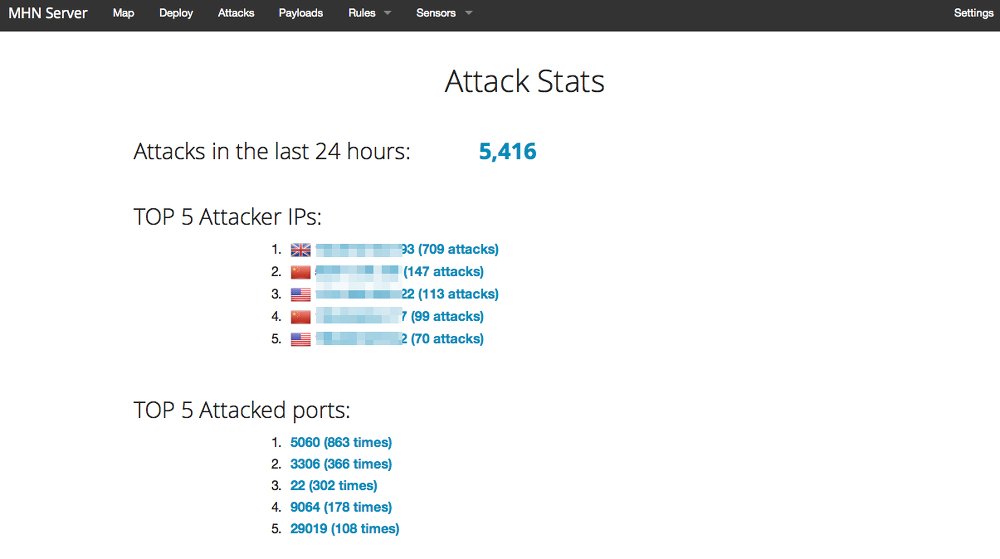 Simple stats for attacks observed in the last 24 hours.
Simple stats for attacks observed in the last 24 hours.
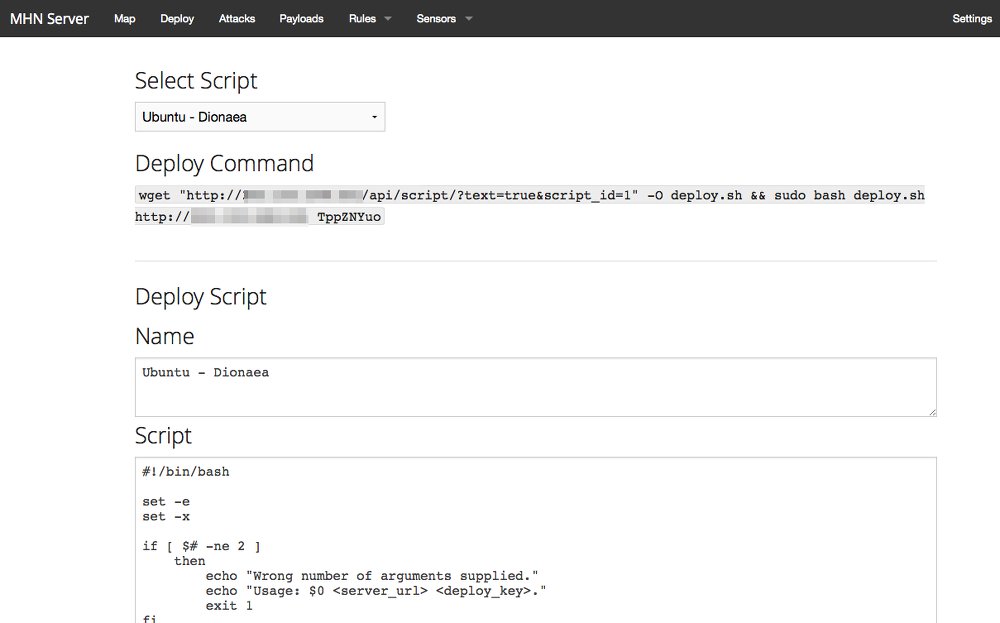 Deploying a new sensor is basically running a script on the honeypot host.
Deploying a new sensor is basically running a script on the honeypot host.
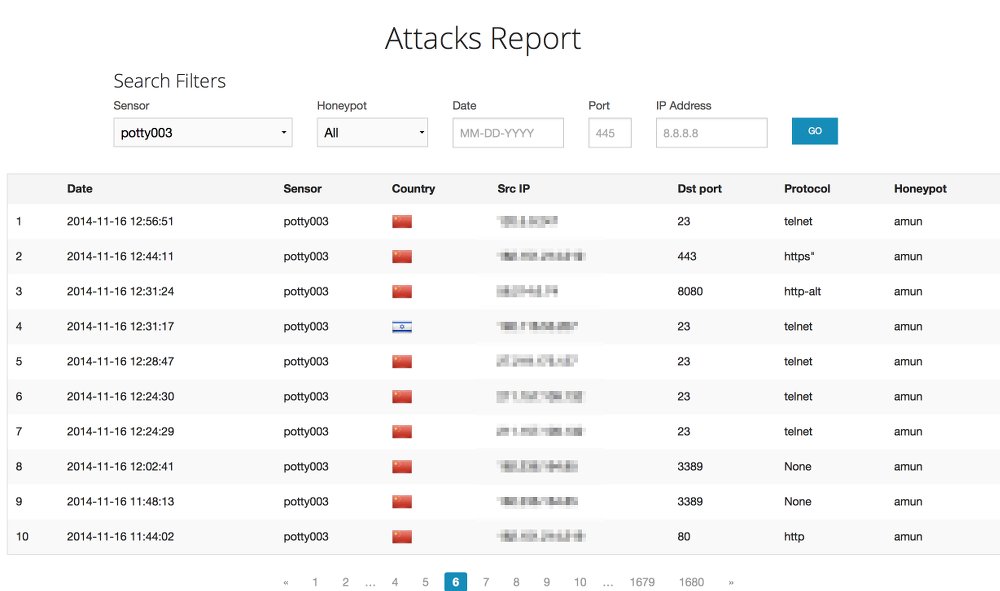 List of attacks captured by specific honeypot sensor (Amun) running on a host called Potty003.
List of attacks captured by specific honeypot sensor (Amun) running on a host called Potty003.
If you are interested to try out MHN then I highly recommend that you watch this introduction video.You can also find a lot of information on the tools I mentioned above at the Honeynet Project website. And while you’re there, do take note of the upcoming 2015 conference in Norway!
Honeypots and honeynets are pretty useful for learning about security and gaining situational awareness of the network or general types of attacks out there. I’ll be blogging about the observations from honeypot sensors our honeypot sensors in the near future so watch this space!
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.

Nice article. I’m gonna try it. Following are some useful links also:
https://zeltser.com/modern-honey-network-experiments/
https://fischer-its.com/?p=2076
https://n0where.net/modern-honeypot-network/
https://itandsecuritystuffs.wordpress.com/2015/02/03/honeypot-networks/
Thanks.