
Electronic government (e-gov) services enable citizens and residents to interact with their governments digitally, via the Internet. The Domain Name System (DNS), which maps domain names to Internet addresses, underpins e-gov.
Together with colleagues at the University of Twente and The National Cyber Security Center of the Netherlands, we have recently published a peer-reviewed study comparing the resiliency and redundancy of e-gov domains of four economies — The Netherlands, Sweden, Switzerland and the United States.
E-gov adoption has grown steadily and has been recently accelerated by the COVID-19 pandemic. E-gov reduces costs, provides faster services, and makes access easier for people with disabilities and mobility challenges. Figure 1 shows a subset of e-gov services provided by the Delft municipality in the Netherlands — you can make appointments, register your address, schedule marriage or partnership services, and more.
E-gov services are provided over the Internet, and the DNS is one of the Internet’s core services. Therefore, if the DNS fails, domains can become unreachable, jeopardizing the ability to deliver government services to citizens. For example, several state government websites in the United States were victims of a DDoS attack, becoming unreachable recently.
Given such risks, it is of paramount importance that the DNS services of e-gov domains are properly configured with maximum levels of redundancy to withstand disruption or stress. Getting that configuration right is not always easy; the DNS has many moving parts, and some are complex and/or difficult to configure.
So, we set out to assess the DNS configurations of e-gov domains, and whether they provide enough redundancy at different layers.
Datasets
It turns out it is hard to obtain a list of e-gov domains per economy as many use their own ccTLDs for e-gov domains, but there is no public list of e-gov domains that governments provide.
So instead, we selected four different economies from which we could obtain data. Our contacts in the Netherlands, Sweden, and Switzerland provided us with curated lists, while the United States .gov domain names are publicly available. The table below shows the number of Second-Level Domains (SLDs), such as example.nl we identified for each economy and their populations.
| Economy | Netherlands .nl | Sweden .se | Switzerland .ch | United States .gov |
| E-gov domains (SLD) | 602 | 614 | 3,971 | 7,972 |
| Population | 17.4M | 10.4M | 8.7M | 332.9M |
Results: DNS providers
The first metric we looked at was the number of distinct DNS providers e-gov domain names have. For example, in Figure 2, example.nl has two NS records, each with its own IP address, which is announced by two different Autonomous Systems (ASes), so we say it has two DNS providers.
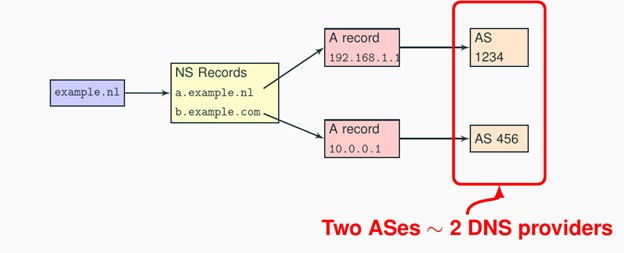
In Table 2, we see that roughly 40% of the NL, SE, and CH e-gov domain names have a single DNS provider (over IPv4). For the US, we see 82% of e-gov domains have a single provider.
| Economy | Netherlands | Sweden | Switzerland | United States |
| SLDs | 602 | 614 | 3,971 | 7,972 |
| Responsive | 601 | 609 | 3,546 | 7,911 |
| Single provider (IPv4 / IPv6) | 43% / 55% | 41% / 41% | 43% / 54% | 82% / 55% |
One could argue that this is a bogus metric — if you host everything on a cloud provider, it ought to be OK. Clouds also occasionally fail, as AWS and Dyn have shown, and even Amazon.com doesn’t use AWS for DNS; they rely on two external DNS providers. While we cannot speak for them, we suspect that it is for the same reason — redundancy. The DNS market is highly localized.
So, who are those DNS providers? Table 3 shows the results. It turns out that DNS services are heavily localized — local companies dominate the market. We believe this is because of the freedom of choice that local governments have in choosing DNS and hosting services; they may choose their traditional local companies.
| Netherlands | Sweden | Switzerland | United States | ||||
| ASN | e-gov | ASN | e-gov | ASN | e-gov | ASN | e-gov |
| Transip | 112 | Loopia | 47 | Infomaniak | 278 | GoDaddy | 1,215 |
| CLDIN | 39 | Tele2 | 23 | Swisscomm | 115 | Cloudflare | 900 |
| QSP | 28 | Microsoft | 21 | Novatrend | 100 | Amazon | 676 |
| Solvinity | 8 | Telia | 21 | Abraxas | 97 | Akamai | 334 |
| SSC-ICT | 8 | Telia | 19 | Metanet | 91 | Tiggee | 316 |
Results: Number of routing prefixes
If the DNS servers of an e-gov domain name share the same routing prefixes, it means they are announced from the same location(s) and are not, therefore, topologically diverse. It creates a false sense of redundancy, given they share large parts of their networking infrastructure. An attack against servers with the relevant prefixes could compromise the reachability of the e-gov domain names.
We, therefore, determined the number of prefixes per domain name. As shown in Figure 3, the number of BGP prefixes found in routing tables matches the IP addresses of the e-gov DNS servers. We used CAIDA’s IP to prefix datasets.
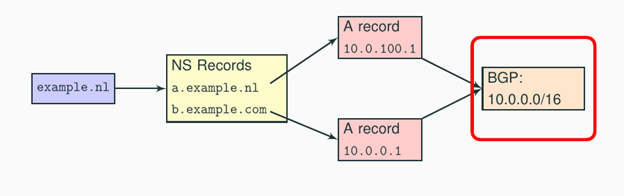
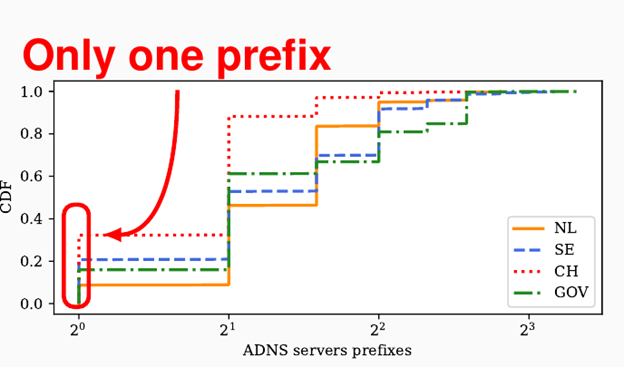
As shown in Figure 4, we see that roughly a third of the Swiss e-gov domain names are announced by a single prefix, while the figure for each of the other economies was less than 20%. Reliance on a single prefix creates unnecessary risk, and we recommend that the operators of the domains in question diversify their networks to increase their resilience and minimize the chances of collateral damage.
Results: Number of TLDs
The next metric we measured was the number of Top-Level Domains (TLDs) that each e-gov domain has for its DNS servers. For example, in Figure 5, we see that there are two TLDs (.nl and .com) for this domain. If one of those TLDs were to become unreachable for some reason, resolvers would still be able to reach the other TLD’s authoritative servers and ultimately retrieve the DNS records for their e-gov domain.
We obtained the following results:
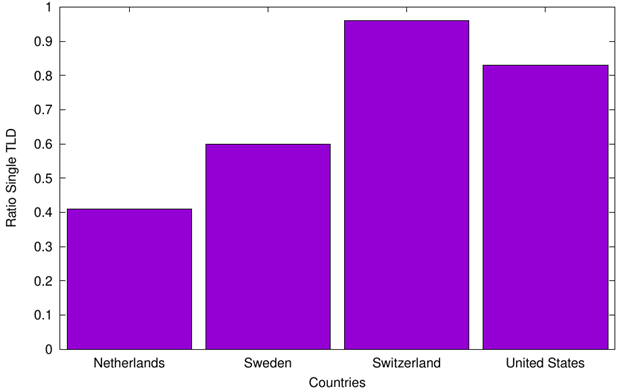
- In fourth place, we have Switzerland, with more than 90% of the Swiss e-gov domains having their authoritative servers under a single TLD – .ch, Switzerland’s ccTLD.
- In third place, we have the United States, with 83% of its domains depending on a single TLD (.com).
- Sweden ranks second with 60% of its e-gov domains depending on a single TLD (.se).
- The Netherlands fares better, although, still a considerable 40% of e-gov DNS servers depend on a single TLD (.nl).
Why so much dependency?
We believe that the reason for the results is that many of the services belong to local governments, and they may typically use whatever DNS services their registrars provide. As such, they are at the mercy of the policy decisions taken by their registrars — if a registrar has a diverse set of TLDs, the local governments in question automatically benefit from it. One option would be to adopt a second DNS provider that employs different TLDs.
Results: Anycast adoption
IP anycast is a technique that allows the same IP prefix to be announced from multiple locations. Traditionally, IP prefixes were announced from a single physical location. With anycast, you can announce the same prefix from multiple locations worldwide, as illustrated in Figure 7.
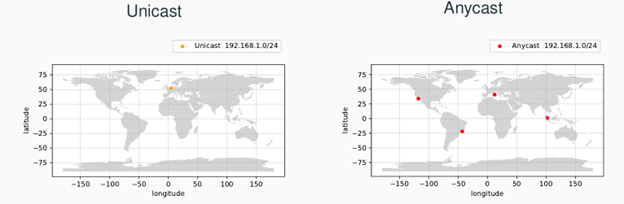
In this way, traffic is distributed across the anycast locations, making it harder to mount an effective Distributed Denial-of-Service (DDoS) attack against an anycast network — some anycast sites (such as those shown in Figure 6) may remain active, while others may be overwhelmed by BGP. The DNS servers under these sites may have different service capacities and suffer from the attack unevenly. We have investigated how anycast reacts to DDoS attacks, and we have presented considerations for anycast operators in an informational RFC.
If we look at the level of anycast adoption for e-gov domains (Figure 8), we see that it’s quite low in Europe — Switzerland has fewer than 3% of its e-gov domains having at least one anycast server. The United States performs better, with over 55% of its e-gov domains on anycast services. The Netherlands has around 20%, while Sweden has 12%.
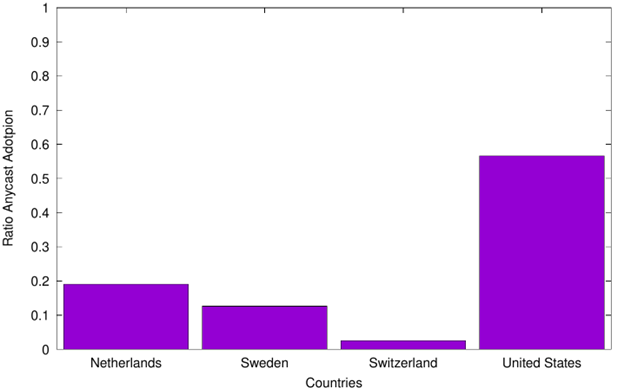
As with TLD usage, the explanation has to do with operational decisions taken by the registrars and DNS providers chosen by the e-gov domain name operators. The situation could be improved by deploying secondary anycast providers.
Wrapping up
E-gov domains play a crucial role in many economies. We have measured four economies and have shown that their e-gov DNS services can still be improved and be made more resilient by adding extra redundancy in terms of DNS providers, routing prefixes, TLDs, and by adopting IP anycast.
If you’d like to know more about this topic, see our peer-reviewed paper with all the experimental details and extra results, and our RIPE 86 meeting presentation.
Giovane Moura is a Data Scientist with SIDN Labs (research arm of SIDN, the .nl registry) and Guest Researcher at TU Delft, in the Netherlands.
Raffaele Sommese, Mattijs Jonker, and Jeroen van der Ham contributed to this work.
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.
