
Domain Name System (DNS) abuse is one of the most important ongoing discussions in the community. Many of the existing industry white papers and general discussions around abuse incidents are based on data from reputation feeds, also called Reputation Blocklists (RBLs). The results of such reports often indicate that domain name abuse is growing. However, these papers typically have used studies focused on a short time span such as half a year or less.
Using data from the ICANN organization’s Domain Abuse Activity Reporting (DAAR) system, the following looks at a longer time horizon. The DAAR system collects DNS security threat data for phishing, malware, botnet command and control domains and spam as a delivery mechanism from RBL providers.
Previous research shows that when the RBLs of different providers were studied, very little overlap was found, indicating that each list covers a different yet important part of this security threat landscape (see the papers Paint it Black: Evaluating the Effectiveness of Malware Blacklists and Quality Evaluation of Cyber Threat Intelligence Feeds). This is why ICANN’s DAAR system uses multiple well-reputed RBLs from a variety of providers, such as SURBL, Spamhaus, Anti-Phishing Working Group, PhishTank, Malware Patrol, and Abuse.ch. For more detailed information about data sources please refer to the latest DAAR report.
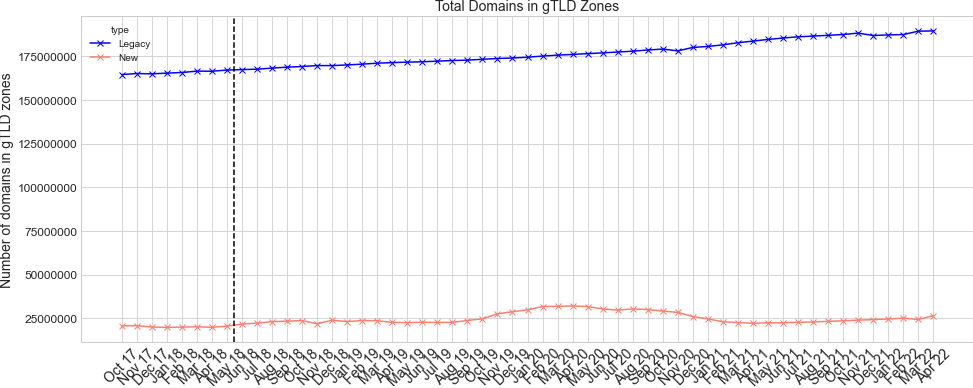
This report aims to demonstrate some of the general trends in security threat concentrations from October 2017 (when the DAAR system began) until April 2022. Figure 1 shows changes in the total sum of domains in generic Top-Level Domain (gTLD) zone files (new and legacy) that are included in DAAR over time. The black vertical line in this figure and all others indicates the time when the General Data Protection Regulation (GDPR) went into effect. As both the blue line for legacy gTLDs and the red line for new gTLDs indicate, the number of names has grown in the gTLD space in general.
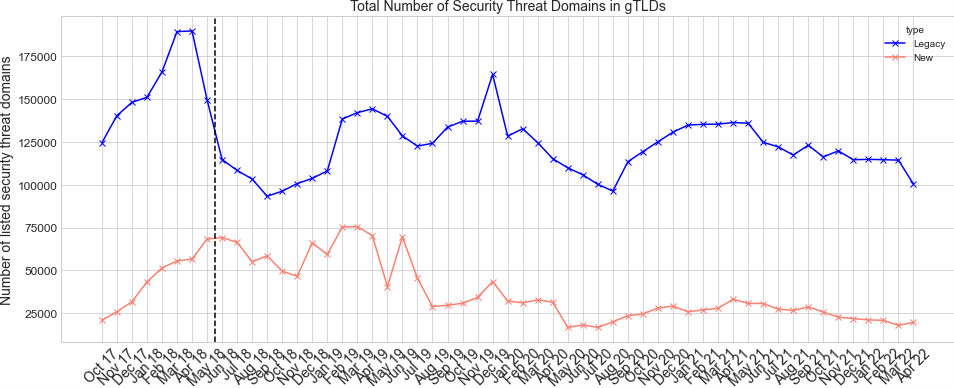
While Figure 1 demonstrates growth in the total number of registered domains in zone files, Figure 2 shows that the total number (absolute count) of security threat domains declined over the same period. A closer look at the source data shows that the spam data from Spamhaus is a significant contributor to the decline.
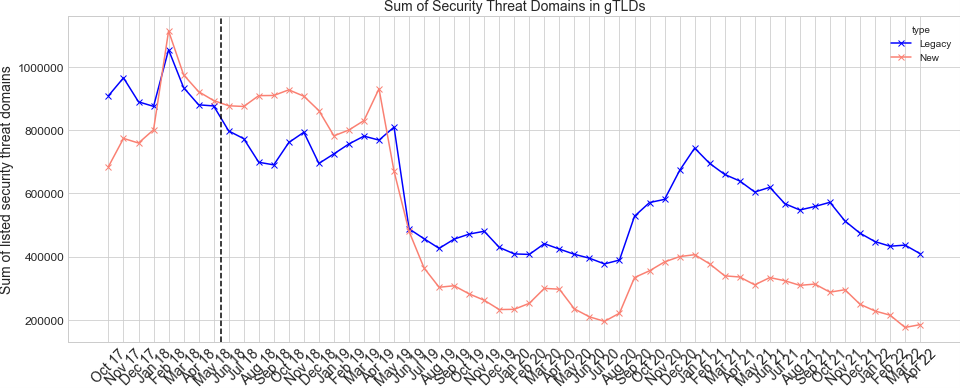
Figure 3 shows the same data as figure 2, but this time Spam as a delivery mechanism is excluded from the RBL data of the plot. What we see is that in both new gTLD and legacy gTLD line security threat counts are less or equal to where they were in 2017, even though the total number of registrations grew over time. Future research by ICANN’s Security, Stability, and Resiliency (SSR) group will take a deeper dive into the underlying reasons for the decline in both figures as well as the periodic spikes in the data.
While absolute counts are important to understand the scale of the security threat concentrations across gTLDs, relative normalized counts, which consider the size of gTLDs, are essential to put these counts and trends into perspective of how gTLDs are performing in comparison to their sizes and market shares. Figure 4 shows the changes in the normalized sum (percentage) of security threat domains in gTLDs over time for all threat types. This is calculated by taking the sum of security threat domains in each type of gTLD and dividing it over the sum of each gTLD size, then taking the percentage of this for any given month. As Figure 4 shows, in April 2022, security threat domains for all threat types are 0.7% of all domain names in new gTLDs and closer to 0.2% in legacy gTLDs. When we look at the numbers if Spam is excluded from the security threat types then the percentage drops to around 0.07% of all domain names in new gTLDs and closer to 0.05% in legacy gTLDs.
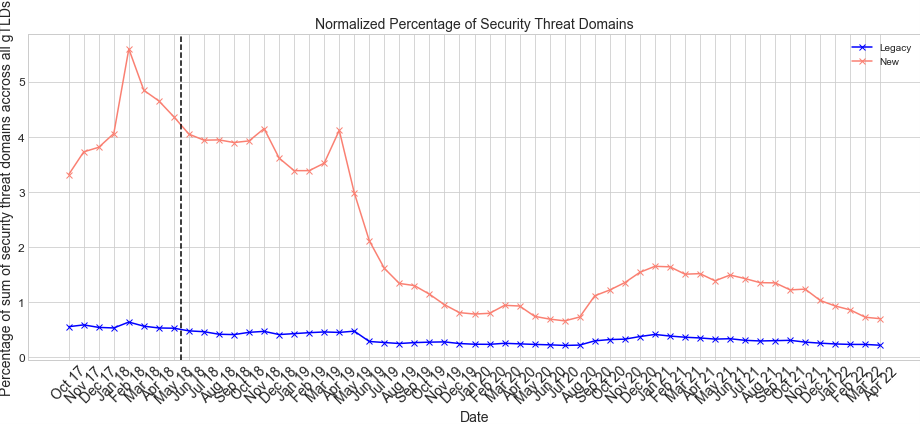
Please note that these normalized percentages of security threat domains in gTLDs over time is different from the calculations used in the DAAR monthly report. This focuses on the sum of security threat domains over a month where DAAR reports look at the average number of security threat domains over a month, a similar method to that used in other white papers including but not limited to the European Commission Study on DNS Abuse.
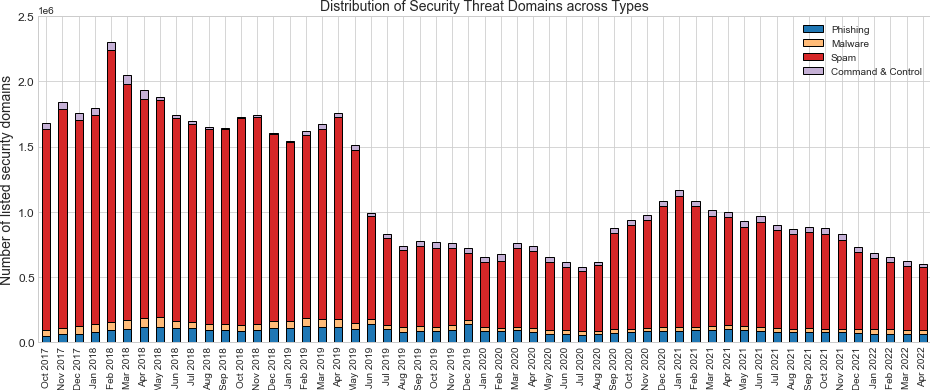
Finally, we examine how the proportion of different threat types changed over the years. As the bar plot in Figure 5 shows, the proportions remain constant over time, with spam being the most prominent type among the data collected, followed by phishing.
While looking at recent data is interesting, it is important to zoom out to assess the context of the trend. Over a longer timeframe, the data here shows DNS security threats trending down both in absolute terms and normalized rates. This does not mean the work is any less important and certainly not done when it comes to combating DNS security threats. Threats against Internet users are real and changing fast.
ICANN encourages the community to continue the important discussions about what additional measures can and should be done to further combat DNS abuse. In parallel, ICANN continues to focus efforts on supporting the mitigation of DNS security threats, with projects like the Domain Name Security Threat Information Collection and Reporting (DNSTICR), increasing data sets in DAAR, and enhanced reporting by Contractual Compliance to name a few. To learn more about DNS abuse and what ICANN is doing to help understand and mitigate it, visit the program webpage.
Dr. Samaneh Tajalizadehkhoob is Director of Security, Stability & Resiliency Research group as part of the Office of CTO (OCTO) group in ICANN’s Europe Region. Samaneh has authored publications on web security, cyber security, Internet measurements, underground economy, and development of security metrics design using advance statistical methods.
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.
