
Snort rules are considered the gold standard of network intrusion detection signatures, and because of that, new analysts need to learn how to read and understand their logic. There are many great blog posts already on understanding Snort rules so I won’t try to rehash them here.
Instead, I wanted to show how you can use Wireshark to find which specific packet triggered a Snort rule in seconds from within the Wireshark GUI, giving you all the surrounding context that a PCAP can give you.
First, what are Snort and Wireshark?
For those that may not be familiar with Wireshark and Snort, I thought it may be helpful to give a brief overview. If you’re already familiar with these tools, skip ahead to the Getting started section.
Snort is one of the most commonly deployed Network Intrusion Detection Systems (NIDS). At an extremely high level, it runs a set of rules against each packet, and if there is a match, it will alert the security team.
Note: Snort is commonly deployed as a part of Security Onion.
Wireshark is the most popular GUI tool for analyzing network packet data. It is incredibly common to use on the job and has a huge feature set that most people do not know about, including dissectors.
Dissectors are meant to analyze parts of a packet’s data. They are typically used to analyze and view custom or new network protocols.
Fortunately for all of us, someone was an absolute legend and came up with the idea of using Wireshark’s built-in post-dissector feature to run Snort against the PCAP you may be investigating.
Getting started
So, how we can use Wireshark to quickly search for Snort alerts within a PCAP file.
Requirements
All you need is a Linux Virtual Machine (VM) with an up-to-date version of both Snort and Wireshark. If you use Ubuntu 20.04 Desktop or newer, the versions within the apt repository should work just fine.
As for hardware, you’ll need:
- 2 CPU cores
- 4 Gb/ RAM
- 50+ Gb storage
Note: Wireshark loads the PCAP into memory. If you have a giant PCAP, you may need to increase the amount of RAM within the VM that you create.
# Setup an Ubuntu 20.04 Desktop Linux VM # Update the VM: sudo apt update && sudo apt upgrade -y # Install wireshark - the defaults here should work sudo apt install wireshark # Install snort - you can accept all of the defaults again however # you will want to update the $HOME_NET variables to match the PCAP # being examined. You'll also be prompted to select an interface # to listen on twice by default, it will be set to eth0 however # you can delete this and leave it blank sudo apt install snort shutdown -r 0
If you’d like to add custom rules or use the ET Pro / ET Open rule sets, you can modify the rules at /etc/snort/rules. Don’t forget to update the snort.conf file at /etc/snort/snort.conf — this is also where you’d modify the $HOME_NET and EXTERNAL_NET variables if necessary.
Configuring Wireshark
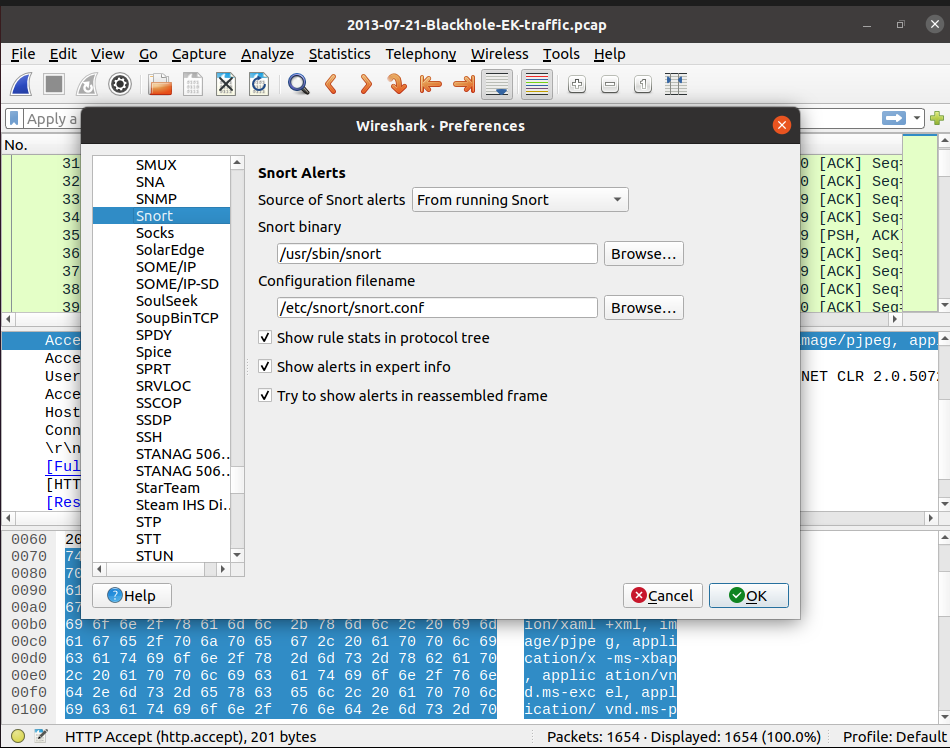
We’ll need to configure Wireshark to see our Snort binary, as well as a few other settings. Go to Edit > Preferences > Protocols > Snort and configure it to match the below image and restart Wireshark:
Searching Wireshark for Snort alerts
Launch Wireshark as root (via the terminal — sudo wireshark) and open the PCAP you want to analyze.
Once done, type snort into the Wireshark filter bar and you’ll see a list of all of the packets that have triggered a Snort alert.
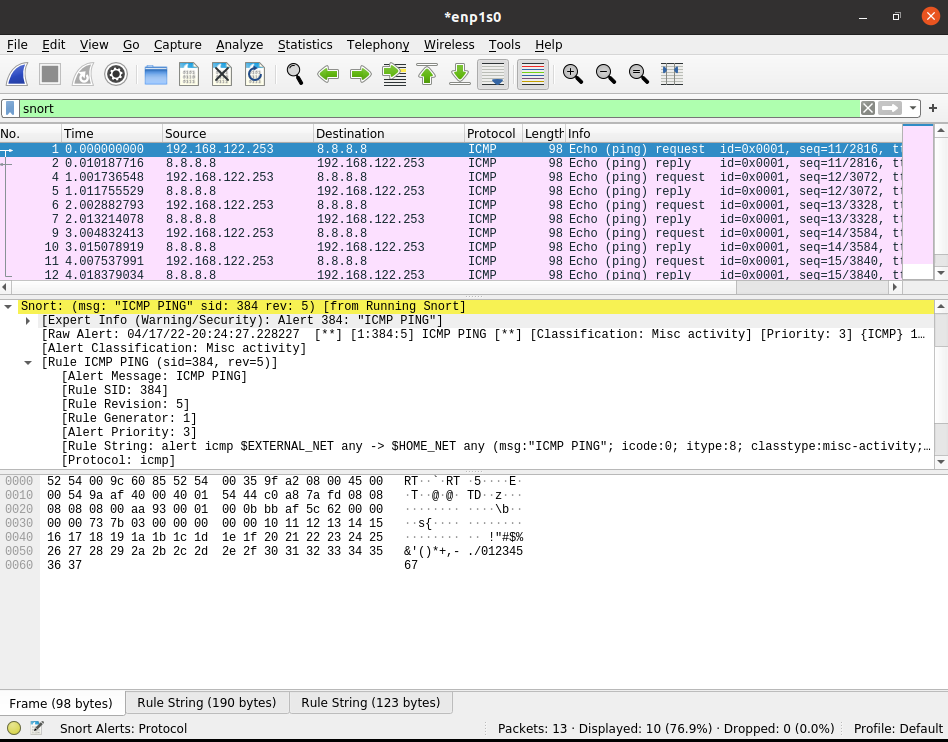
You’ll also notice in the middle Wireshark pane a Snort section with various information on the Snort rule(s) in question that triggered (how cool is that?!).
If this is something you’d use frequently, consider identifying which snort fields are useful, and right-click > set as column which can make it easy to see which packets have triggered an alert and which alert it was (Figure 3).
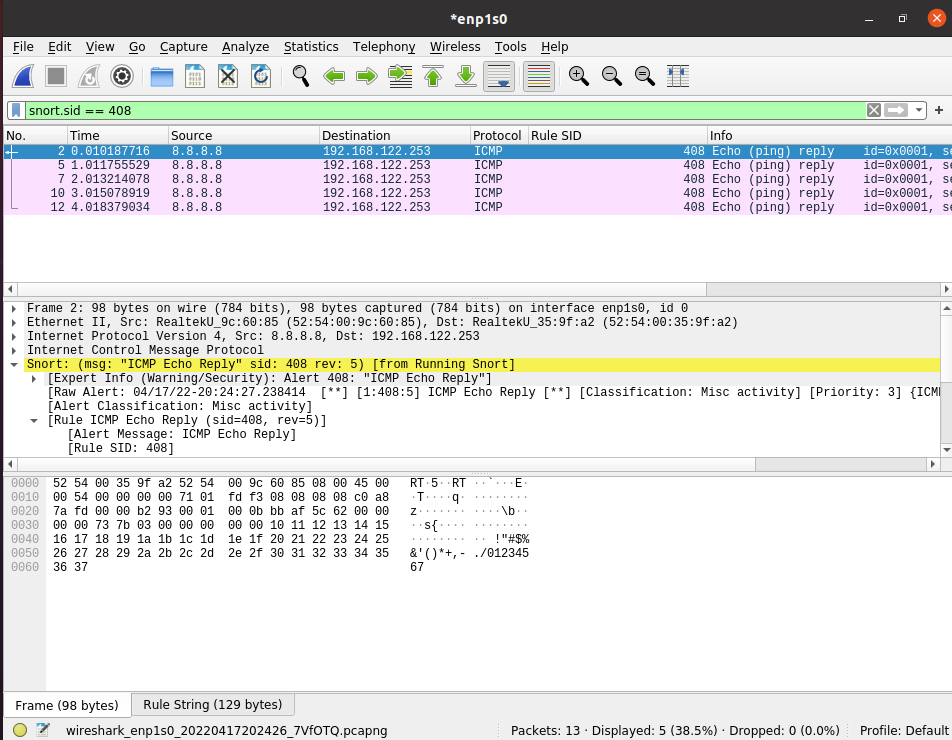
Finally, there are many other fields you can search the PCAP on related to Snort, such as the Signature ID (SID), shown in Figure 3. For reference, check the Wireshark display filter documentation.
But we use Suricata…
Unfortunately, there isn’t a Suricata post-dissector at this time. But all is not lost! Most of the ET Pro / ET Open Suricata rules have a corresponding Snort rule. If you’re using the ET Pro / ET Open rulesets with Suricata, you can still follow this guide and search for its corresponding Snort SID.
Final thoughts
Boom! You’ve now used Wireshark to analyze a PCAP for any Snort NIDS alert that may have triggered, in seconds. Consider replacing the default ruleset with one such as the ET Pro / ET Open rulesets to extend this capability further.
If this blew your mind (like it did mine when I learned it existed) then be sure to share this post to help others!
Adapted from the original post which appeared on SIGNALBLUR.
David Burkett is a cloud threat detection specialist with more than 14 years of enterprise IT experience.
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.
