More than 5,000 Low Earth Orbit (LEO) satellites will be orbiting the Earth by the end of 2021. Their applications range from Earth-imaging and monitoring to, most notably, broadband Internet access.
SpaceX Starlink, Amazon Kuiper, and others are deploying hundreds to thousands of satellites, each carrying high-bandwidth networking equipment. SpaceX alone is on track to launch 11,000 satellites to complete its own LEO satellite network (LSN).
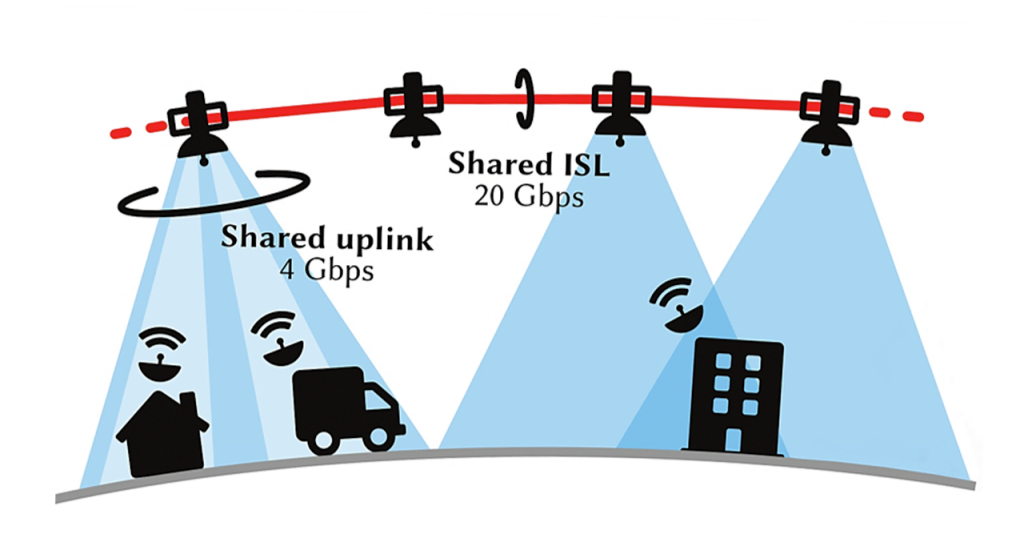
The race to design and deploy space communication networks is driven by their extremely appealing cost-performance trade-off. Even in their current configuration — where the constellations are only partially deployed and no intersatellite links (ISLs) are available — the sending rates of user ground terminal units (TUs) are already competitive with broadband, averaging tens of megabits with peak rates over 560 Mbps. And all of this is available globally, without the monstrous costs of laying fibre around the world. Given this unprecedented ease of access and high transmission rates, the demand for LSN services is skyrocketing, resulting in an enormous, but expected, number of TUs. In fact, SpaceX has requested permits for 5 million terminals in the US alone.
The excitement around this ‘New Space’ industry is also mirrored in academia, with a flurry of new publications following the developments of the networking space race. Most of this work has revolved around the expectation that LSNs will deploy ISLs, where satellites will be connected to others with high-bandwidth laser links forming an orbiting mesh.
Thanks to ISLs, the communication latency in LSNs will be significantly lower than in terrestrial networks. Researchers from many institutions — including ours at ETH Zurich — have been fantasizing about the game-changing opportunities that will be opened by these low-latency, high-bandwidth, and globally reachable networks.
Flying too close to the sun
However, the aspect of the secure operation of this new type of network has so far been largely ignored. To bridge this worrying gap, we at ETH Zurich decided to explore the resilience of LSNs to a large-scale volumetric distributed denial-of-service (DDoS) attack in a recent publication.
This study was a departure from the traditional literature on satellite security, which is mostly focused on jamming and the weak (or non-existent) encryption of uplinks. Instead, our work is more closely related to the extensive studies of DDoS in terrestrial networks.
Yet, LSNs are extremely different from their terrestrial counterparts, and we soon realized that the quest for high-speed satellite networking can be exploited by an adversary, turning the great opportunities of low-latency and global accessibility into threats to the viability of the LSN itself.
This observation is the starting point for our paper, ICARUS, a cautionary tale that — like the original Greek myth — warns against the hubris of seeking great technical achievements without caution.
DDoS on satellite networks
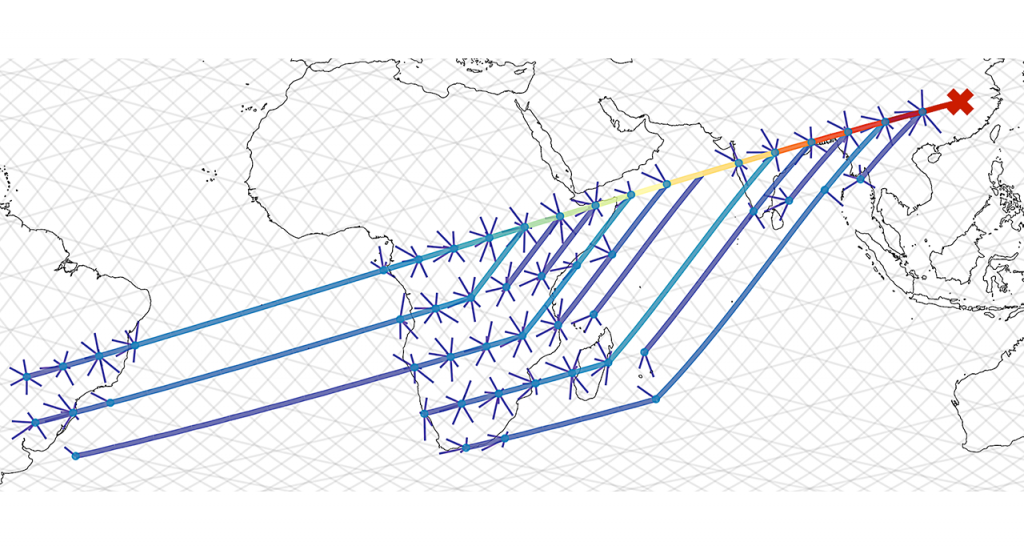
In an ICARUS attack, the adversary carefully plans attack flows and exploits an LSN’s structure to congest a link or a set of target links, rather than hosts. The adversary hopes to do so at low cost in terms of attack traffic volume, and with low detectability in terms of change in ingress traffic volume on the ground-to-satellite links.
Similarly to other terrestrial DDoS attacks (such as Coremelt), ICARUS achieves two devastating properties: The victim is unaware it is under attack, and the attack traffic is indistinguishable from legitimate communications — after all, the bots are ‘legitimately communicating’ with each other.
An LSN, however, has peculiar characteristics that make the straightforward application of Coremelt challenging. Unlike a terrestrial transit network, the LSN connects directly to the clients injecting traffic, and can more easily detect and stop malicious behaviour. The client population will initially be much smaller than the Internet, limiting the adversary’s resources, and finally, the sparse structure of the satellite network creates a risk of attack traffic flows congesting each other instead of the target(s).
However, our analysis uncovered features of LSNs that can be exploited to improve an adversary’s chances of congesting their desired links. Due to the predictable motion of orbiting satellites, an adversary can use public knowledge (filed to the FCC) of satellite position and orbits to compute the network topology days ahead of an attack.
The adversary can, in principle, compromise many vulnerable devices connected to satellite terminals. The globally encompassing nature of LSNs then plays in the adversary’s favour, enabling better control of attack paths as they can select the geographic location of the bots (the adversary knows the location of compromised terminals, as they are equipped with global navigation satellite systems (GNSSs) receivers to aid with signal acquisition).
Crucially, the goal of achieving low-latency communication drastically restricts the routing choices on the satellite network, forcing LSN operators to choose among the routes that provide close-to-optimal performance.
Space laser attack simulations
To assess the danger posed by ICARUS, we simulated its impact on existing and upcoming constellations, starting with the largest deployment to date, Starlink.
We found that an adversary can successfully target the majority of Starlink’s links, congesting both ground-to-satellite links and ISLs. Frighteningly, multi-target attacks that hamper connectivity between large regions are also feasible, without increasing the relative cost or detectability of the attack.
We also varied the assumptions on the internal routing algorithms used by the LSN, hoping that randomized load balancing would introduce enough uncertainty in forwarding decisions to prevent adversaries from finding the correct paths to reach the target links. Unfortunately, our experiments showed that ICARUS is still able to attack targets at some additional cost compared to the single shortest-path scenario.
What’s more, using randomized load balancing reduces the performance of paths even in the absence of an attack, by selecting non-latency-optimal paths. Therefore, the satellite network operator pays a price in forwarding latency, while obtaining only a minor increase in attack resilience.
A framework to study satellite DDoS resilience
Our work on DDoSing LSNs provides insights into the expected vulnerabilities in upcoming satellite constellation networks. Thanks to these insights, we were able to outline solutions and mitigations for the ICARUS attack.
In broad strokes, these mitigations come from either more resilient routing strategies, or a bandwidth reservation system (such as Colibri) supplemented by a more sophisticated billing system.
Much further work is needed to explore and evaluate these mitigations, but we hope our open-source LSN attack simulation framework will help in the development of secure and resilient LEO satellite networks.
Contributors: Tommaso Ciussani, Adrian Perrig, and Ankit Singla.
Giacomo Giuliari is a PhD student at the Network Security Group at ETH Zurich.
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.
