Attackers will take advantage of whatever tools or circumstances are at their disposal; this includes COVID-19.
Taiwanese cybersecurity body TWCERT/CC faced a changed threat landscape in 2020. Taiwan was among the economies that contained the COVID-19 outbreak very well, only to discover it also needed to face an outbreak of related malicious activity online.
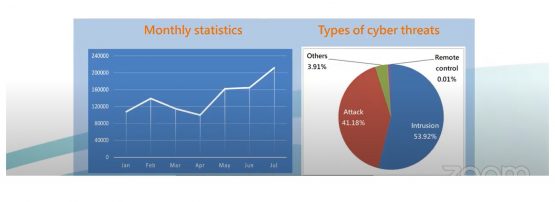
An APNIC 50 conference presentation highlighted the scope of the cybersecurity threat TWCERT/CC faced, which included over a million cyber threat records in the first six months of 2020.
Five key threats
TWCERT/CC Director Chih-Hung Lin elaborated on the key types of COVID-19 attacks being used.
“Attackers used COVID-19 social engineering to increase the success rate of their attacks,” he said. “Based on the cyber events we received, there are five types of attacks related to COVID-19.”
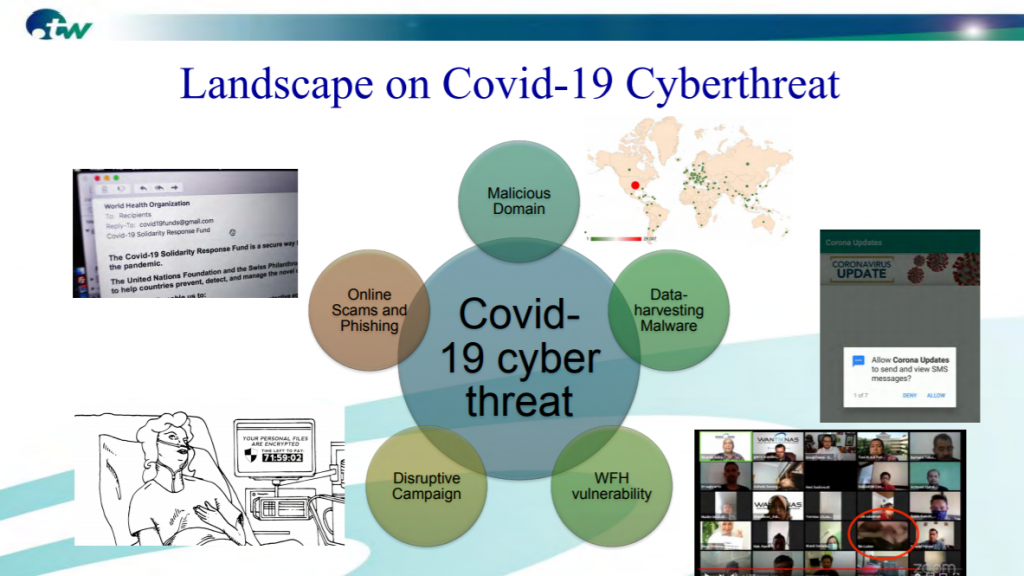
They ranged from attackers exploiting vulnerabilities in software people were using to work from home, through to new COVID-19-based online scams and phishing attempts.
Medical facilities targeted
One particularly concerning development included attempted attacks on medical facility infrastructure. “This was not to steal information, it was to prevent access to critical data or disrupt the epidemic prevention system,” Chih-Hung said.
TWCERT/CC Security Engineer Henry Chu also pointed out that attackers used COVID-19 to launch ransomware attacks on hospitals.
Working from home isn’t as safe as it seems
Chih-Hung pointed out that the widespread use of home networks created more vulnerabilities during the COVID-19 pandemic. “People were accessing enterprise resources remotely, but home networks are not as efficient as enterprise networks. If someone at home gets infected by malware it may spill into the enterprise core network,” he said.
Zoom phishing was also a key problem. These attacks began with an email that impersonates a notification from Zoom, to join a meeting that has been missed. It encourages the user to click the link for more details and access a recording of the meeting and prompts them to enter login details.
“It creates a sense of urgency and panic,” Henry said. “This is a key trait of many scams to get people to click the link and provide personal information.”
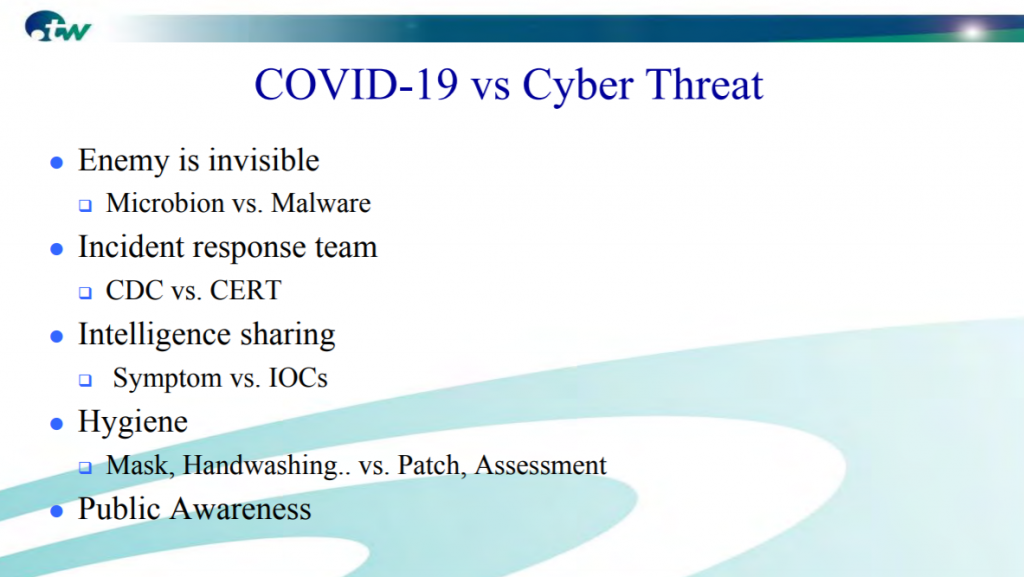
There are similarities between COVID-19 and cyber threats
Many of the practices that can be used to contain COVID-19 apply quite well in the context of preventing cyber threats. “Both of the enemies are invisible,” Henry said. “It’s challenging to deal with, whether it’s microbial or malware. Therefore, we need centres for disease control and prevention for COVID-19, and a CERT team to quickly deal with an emergency cyber-response situation,” Chih-Hung said.
Domain name abuse
There was also an increase in COVID-19 related domains — and in some cases they were the launching point for themed attacks. “There are increased malicious domains registered and the attackers may use these domains to launch malicious campaigns such as malware, C2 and spear-fishing,” Chih-Hung said.
Henry elaborated on the kinds of domains being used by attackers. “When there’s an emergency, a new cyber threat emerges,” he said. “Attackers make use of the public fear and they register COVID-19 related trending words such as virus, Corona, COVID, test, vaccine, and mask. It’s used as a means to send spam or phishing websites to spread malware.”
Impersonation is also a key problem. “We also observe that many attackers impersonate well-known organizations,” Henry said. “The WHO declared COVID-19 a pandemic on 11 March, and we can see a drastic increase in domain registrations of related domains on that day.”
A wide range of organizations were copied. A popular supermarket chain in Taiwan, PXMart, had its Facebook fan page copied to lure in victims on the offer of free face masks.
Not all the new related domains were created with malicious intent, of course. About 90% were likely to be speculators holding on to domains in the hope they could be sold at a higher value. “But there are still thousands of domains being identified as active threats,” Henry said.
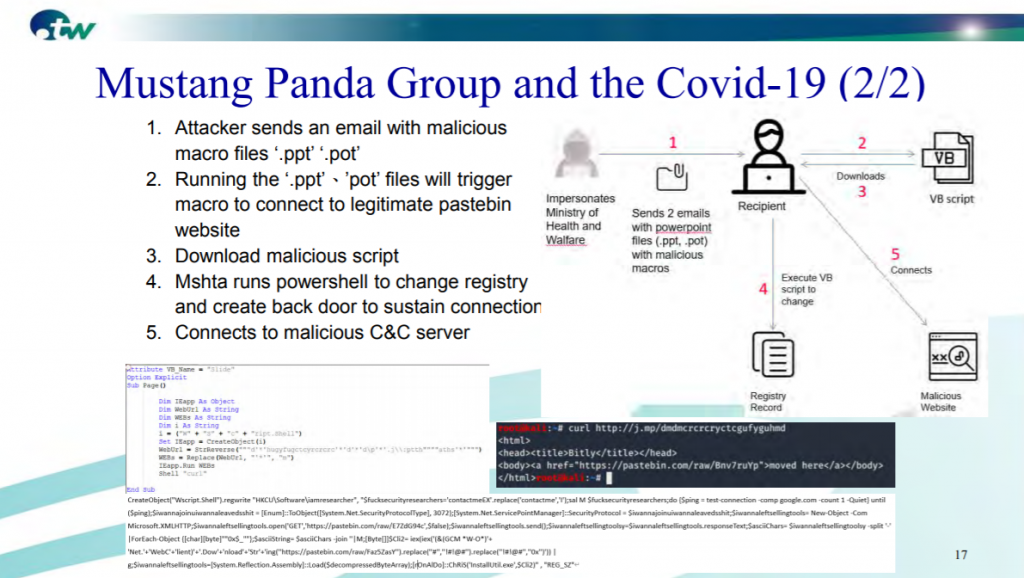
He examined the case of the hacker group ‘Mustang Panda’, which in June, impersonated Taiwan’s Ministry of Health and Welfare. They then used that as a springboard to target the economy’s technology sector. “As a CERT we responded quickly to analyse these files and share that information nationwide,” Henry said.
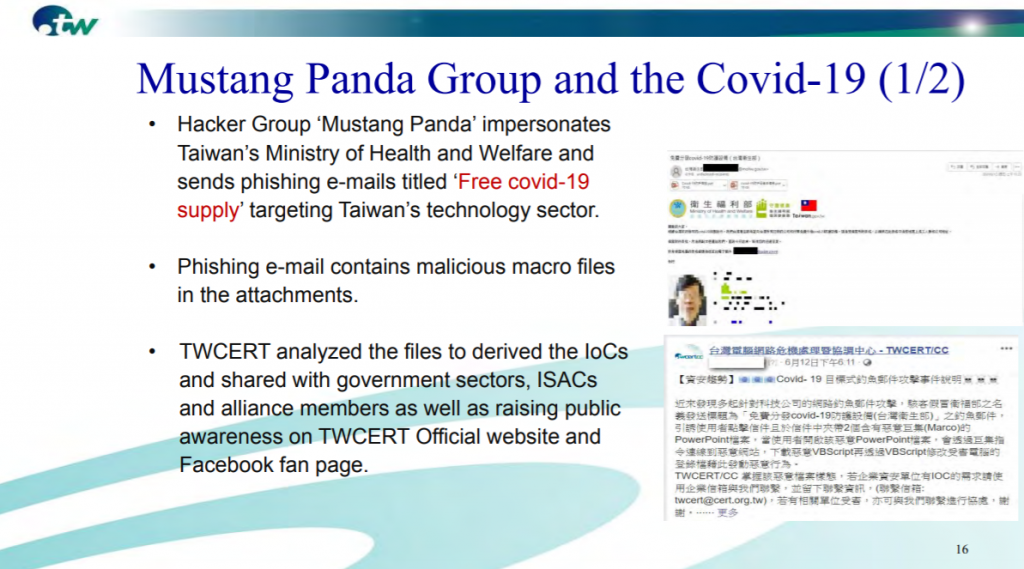
Henry also explained how Mustang Panda used malicious PowerPoint files to conceal macros. Henry pointed out the way the script was used to evade detection (Figure 4).
“What’s interesting about this case is that although the crafty email was in the traditional Chinese language that we use in Taiwan, and which aimed to impersonate the ministry of Health and Welfare, instead in the email, they claimed to be the National Health Commission,” Henry said. “This is a name that is widely used in mainland China, so this was the first giveaway clue of where the attack possibly originated from.”
The TWCERT/CC team had five key pieces of advice for dealing with COVID-19 related cyber threats:
- When receiving suspicious emails, do not click on unknown links or download attachments.
- When receiving links from well-known organizations, do not click on unknown links, instead use a search engine and access them via the official website.
- Confirm it is the right organization through other communication channels.
- Back up files regularly.
- Treat cyber threats like a pandemic.
You can view the full APNIC 50 presentation by Chih-Hung and Henry below.
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.
