
In this post, we will look at basic Neighbor Discovery messages used in IPv6.
There are five different ICMPv6 message types defined in RFC 4861, which are:
- RS — Router Solicitation (ICMPv6 type 133)
When an interface becomes enabled, hosts may send out RSes that request that routers generate Router Advertisements (RAs) immediately rather than at their next scheduled time.
- RA — Router Advertisement (ICMPv6 type 134)
Routers advertise their presence together with various link and Internet parameters either periodically, or in response to an RS message. RAs contain prefixes that are used for determining whether another address shares the same link (on-link determination) and/or address configuration, a suggested hop limit value, and so forth.
- NS — Neighbor Solicitation (ICMPv6 type 135)
A Neighbor Solicitation (NS) message is sent by a node to determine the link-layer address of a neighbor, or to verify that a neighbor is still reachable via a cached link-layer address. NSes are also used for Duplicate Address Detection (DAD).
- NA — Neighbor Advertisement (ICMPv6 type 136)
A Neighbour Advertisement (NA) message is sent in response to an NS message. A node may also send unsolicited NAs to announce a link-layer address change.
- Redirect (ICMPv6 type 137)
Redirects are used by routers to inform hosts of a better first-hop for a destination.
Watch this great 10-min video by Rick Graziani (Cisco Press) to understand these message types.
All of these messages should use link-local addresses (FE80::/64) as their source and a hop limit of 255 (for security reasons).
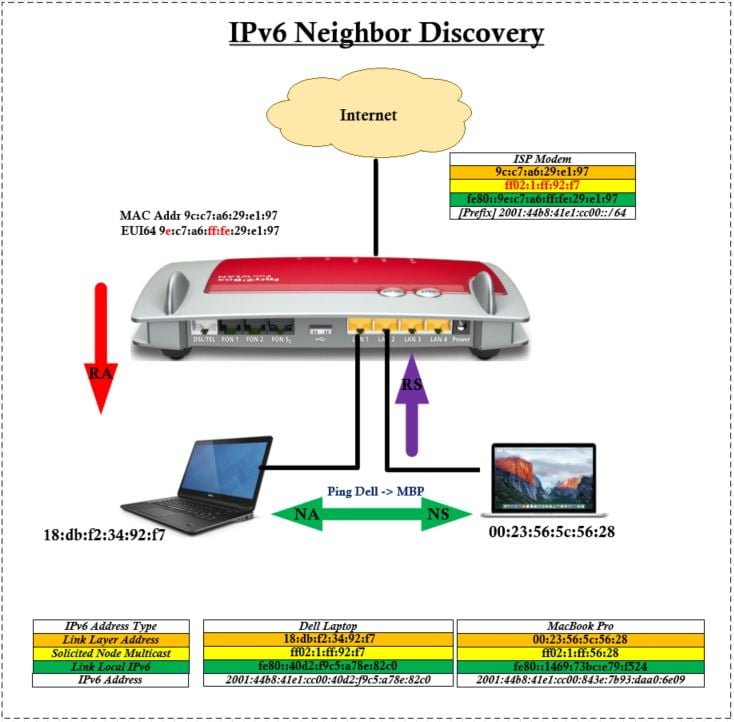
My test setup is as shown in Figure 1 below. I have taken Wireshark captures from these laptops (using capture filter – IPv6) to look at details of these ICMPv6 frame exchanges.
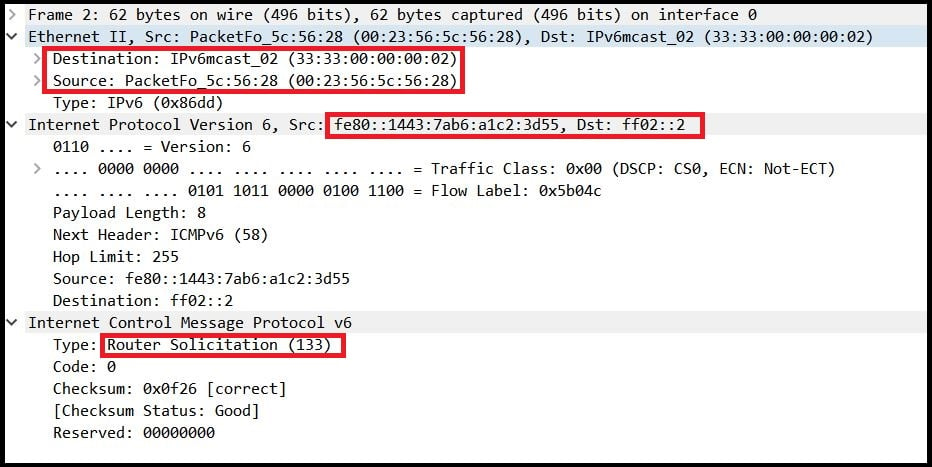
Router Solicitation (RS)
These messages are sent by nodes when they boot up to find any routers in a local segment. It will send to the ‘All Router IPv6 Multicast Address’ (FF02::2). All layer 3 multicast addresses have a corresponding layer 2 mac address (33:33:xx:xx:xx:xx) where xx:xx:xx:xx are the last 32 bits of the layer 3 multicast address). Here is the pcap file for RS/RA frames for your reference.
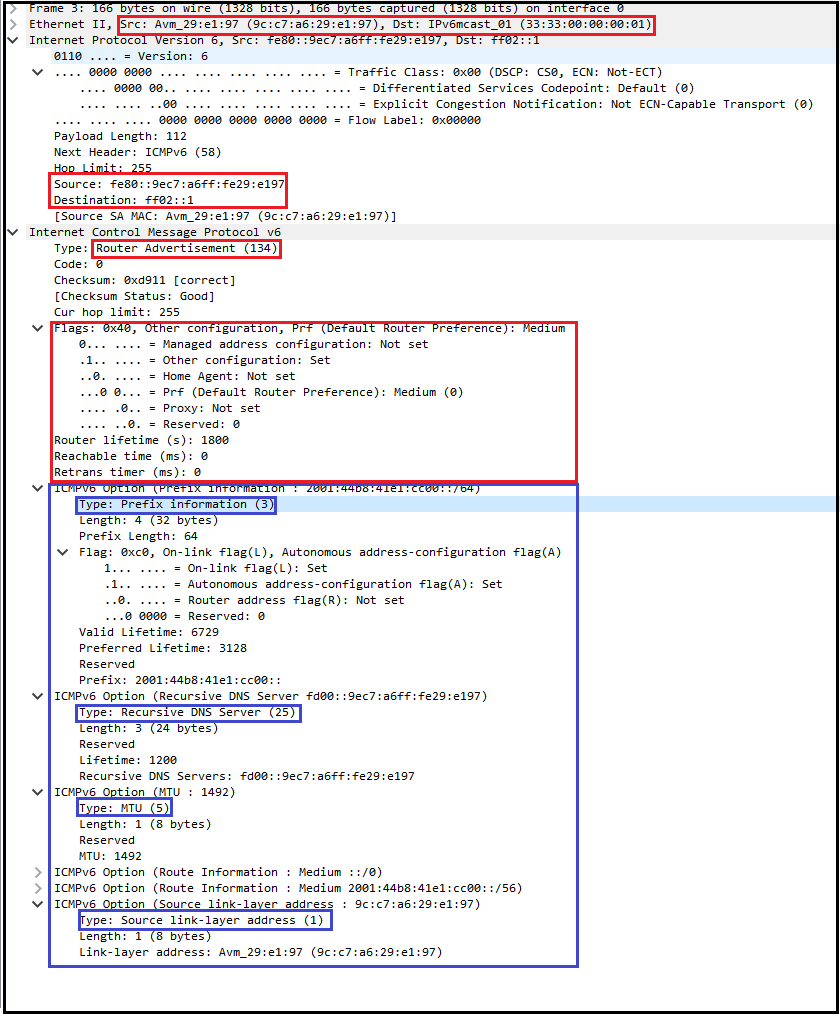
Router Advertisement (RA)
An RA will be sent periodically or as a response to an RS message. Routers in a local segment will respond to RS messages with a RA (ICMPv6 type 134) message — it is destined to the all-nodes multicast addresses (FF02::1). RAs consist of certain flags and options (prefix, MTU, DNS, SLLA – Src Link-Layer Address).
Here is the meaning of certain flags:
- Managed (M flag) = A ‘1’ means the address is provided by stateful DHCPv6.
- Other (O flag) = A ‘1’ means that the address is provided by Stateless DHCPv6, useful for providing options when the client is doing SLAAC–Stateless Address Autoconfiguration. (Note, there is no option for a default gateway).
- Address Autoconfiguration (A flag) = A ‘1’ means that it suggests the host creates its own IPv6 address using SLAAC.
- Router lifetime = anything other than a ‘0’ value means the source sending the RA will be the default gateway. (Note, it is a link-local address and not global unique address).
Here are different options seen in the given RA:
- Option 3 — Prefix Info (Every RA should have this field)
- Option 25 — DNS Server Info
- Option 5 — MTU
- Option 24 — Route Information
- Option 1 — Source Link-Layer Address
Note, it uses a link-local IPv6 address FE80::9ec7:a6ff:fe29:e197 as a source. This address will be used as the ‘default-gateway’ by the host. In this packet, an ‘A’ flag set to 1 means a laptop will derive its IPv6 address based on the prefix information 2001:44b8:41e1:cc00::/64 provided by a router. Depending on the Operating System (OS) running on the end device, some devices will choose the EUI-64 method to derive the Interface-ID part of an IPv6 address while other devices will use 64 random bits for better security (you will see both Windows 10 and Mac Book Pro laptops using random bits instead of EUI-64.
There are another two types of neighbor discovery message exchanges called NS — Neighbor Solicitation and NA — Neighbor Advertisement. These are similar to the ARP process in IPv4, where nodes need to learn link-layer addresses (MAC address) before communicating with each other. In IPv6, it is done via NS and NA messages.
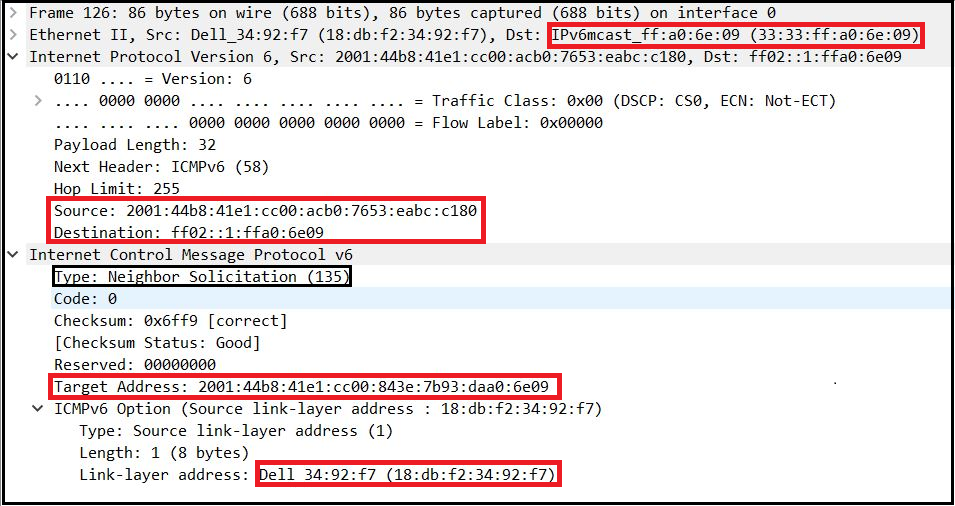
Neighbor Solicitation (NS)
Here are the packet details of an attempt to ping from a Dell Laptop to a MacBook Pro (ping 2001:44b8:41e1:cc00:843e:7b93:daa0:6e09 from a Dell Laptop). Here is the NS message sent by the Dell to the MacBook Pro.
First, the Dell laptop needs to find out the MAC address of the MacBook Pro, so it will send an NS message to the solicited-node multicast address of the target (MBP) that has the lower 24 bits from the IPv6 unicast address (ff02::1:ff:a0:6e:09). Every layer 3 multicast address is mapped to a layer 2 multicast MAC address (33:33:xx:xx:xx:xx) where xx:xx:xx:xx are the last 32 bits of the solicited-node multicast address. In this case, the destination MAC address is 33:33:ff:a0:6e:09 (Note, the lower 32 bits came from an IPv6 solicited-node multicast address.
Neighbor Advertisement (NA)
When a device gets an IPv6 address, it will join a solicited-node multicast group to see if any other devices are trying to communicate with it. In our case, the MacBook Pro actively joins its solicited multicast group ff02::1:ff:a0:6e:09. Therefore, it gets to know about NS messages and it will respond with NAs. It will send these directly to a Dell Laptop’s link-layer address (as it was in the NS message). Additionally, it will set flags, in my case:
- Router flag 0 as a response going from another node.
- Solicited flag 1 as its response to an NS message.
- Override set to 1, to let others know about it is link-layer address.
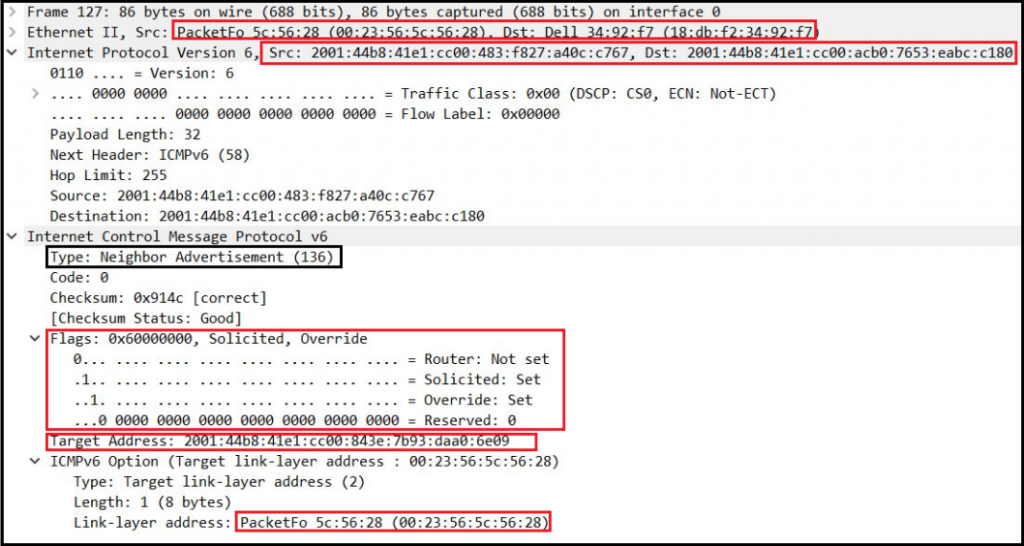
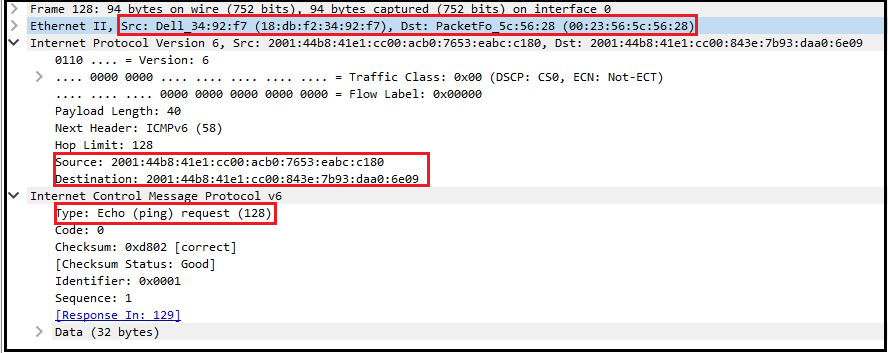
Once the layer 2 address is known by each node, they will communicate directly (frame 128 – 135 as shown below). Here is the capture of frame 126-135 for your reference.
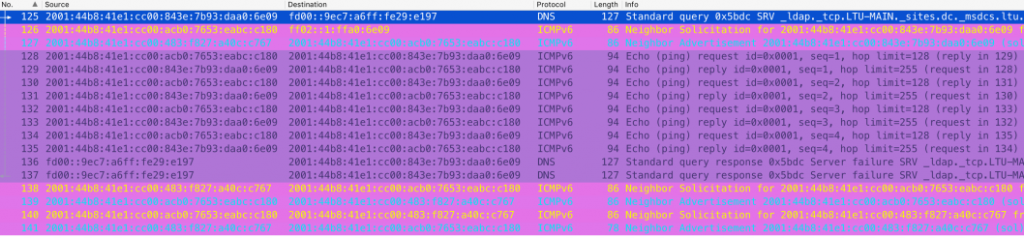
The screenshot below shows frame 128, which illustrates how Dell laptops use MacBook Pro MAC addresses as layer 2 destination addresses.
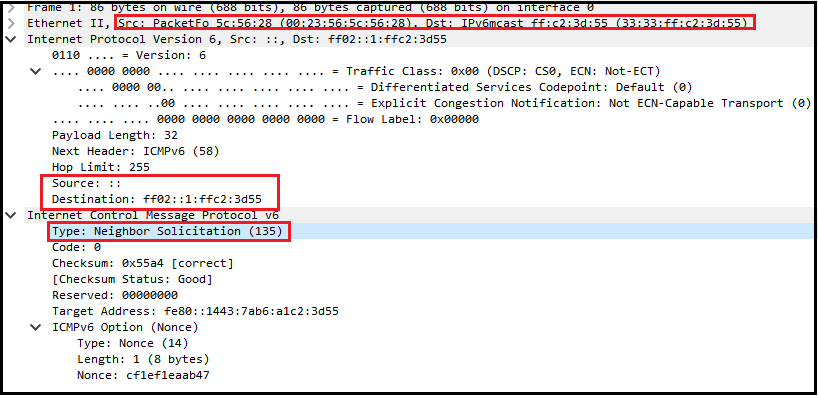
Duplicate Address Detection (DAD)
There is a special type of NS message used for DAD. In this case, NS messages source an unspecified IPv6 address ::/128 and a destined solicited-node multicast address of the IPv6 address it intends to use.
Redirect (ICMPv6)
Since my test setup does not have multiple routers, I could not see ICMPv6 redirect messages in the captures.
Adapted from original post which appeared on mrn-cciew.
Raskia Nayanajith is a networking professional with 15 years’ experience in ICT and Cisco technologies.
Discuss on Hacker NewsThe views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.

Hi,
I have one question about the RA packet, the SRC IPv6 who is?
in the schema is not rapresented
Source: 2001:44b8:41e1:cc00:483:f827:a40c:c767
Sorry the NA packet.
You have the following statement:
“All of these messages should use link-local addresses (FE80::/64) as their source”
But the wireshark output doesn’t have a single such source address.
Can you please clarify this for me?
Worrying that the Cisco CCNA Official cert guide has this wrong then if we trust Wireshark… here is the Cisco cert guide excerpt:
“PC1 initializes and does a DAD check, but PC2 happens to already be working and already be using the address. … The figure shows the following steps:
1. PC1, before using address 2001:DB8:1111:1::11, must use DAD.
2. PC1 sends an NS message, listing the address PC1 now wants to use (2001:DB8:1111:1::11) as the target.
3. PC2 receives the NS, sees what PC2 already uses as its own address, and sends back an NA.
4. PC1, on receiving the NA message for its own IPv6 address, realizes a duplicate address exists.”
!! NO mention of using the SNMA for the destination !!
The CCNA 200-301 Official Cert Guide states (on page 599):
” The NS message is sent to the solicited-node multicast address associated with the target address, so the message is processed only by hosts whose last six hex digits match the address that is being queried”
Hi i have a question. If a Host doesn´t know the MAC of the targeted Host. Which protocol does it use to get the MAC?
a) ICMPv6
b) Neighbor Discovery Protocol (NDP)
or/and
c) Stateless Address Auto Config (SLAAC)
I need this for my study and im not sure if its just a or b or both. Can u help me please?
a) ICMPv6
This is illustrated quite well in the packet captures.
Good luck in your studies.
where is source address on router solicitation: fe80::1443:7ab6:a1c2:3d55
come from ?
you would better learn how to communicate well with other people before represent this IPv6 topic