Defenders have to be right 100% of the time and attackers have to be right once…
I am so tired of hearing this. Yes, attackers have a significant edge. However, I believe with some tweaks to how we approach network security, we can tip the balance back in our favour.
Change your mindset
We, as defenders, have traditionally built our solutions as castles hoping to prevent all the bad from getting in. Prevention fails for any number of reasons. Perhaps you just bought the tool to stop the attack and haven’t implemented it yet. Perhaps it’s untuned. Perhaps the alert is caught up in the middle of thousands of false positives and it’s missed by the team. Perhaps a user clicks on a malicious link.
Instead we need to change our mindsets. By assuming that attackers have already breached your system you will immediately start to think about all of the blind spots inside your systems and networks that would lead to them achieving their goals.
Take advantage of a home-field
We built the network and systems and (should) understand where the most valuable data is. Therefore, we already have a head start on attackers. Not only this but we get to determine the secure configs in use (that is, thinning out the attack surface). We get to decide to harden systems and not use local admins. We get to implement honeypots and mantraps and deception to make the attackers jobs harder.
That said, we cannot protect what we don’t know about. For far too long we have given up on asset management or just considered that it can never be done. This is irresponsible, as we cannot detect anomalies or assure against attacks if we don’t know the landscape, state and content on your system.
Learn from what we know
Thanks to research and years of reconnaissance we have the tools and understanding to see what attackers do and how they do it.
In 2011, Lockheed Martin launched the Lockheed Martin Killchain, which did an excellent job describing the phases an attacker goes through when attempting to breach a system. They did an amazing job showing that attacks occur over time and in various stages. This was a great starting point for the community to learn what anomalies to look for and when to look for them.
In 2018, MITRE launched the MITRE ATT&CKtm Framework, which gave the community the nomenclature of attacks. Through ATT&CKtm, the community is able to maintain a constantly updating set of the techniques, tactics and procedures (TTPs) that attackers use to break into systems. If you want to see all the techniques used by a particular APT group they are there. If you want to see how just lateral movement is achieved on a windows system that’s also there.
I am a big fan of MITRE ATT&CKtm and I can’t think of anything else over the last two years the community has rallied around like this. Whether it is better product testing or design, I think they have had a major impact.
Think like an attacker
While the MITRE chain brings us up to date on TTPs and helps with designing suitable monitoring and prevention tools, we need to understand where to deploy these for greatest effect.
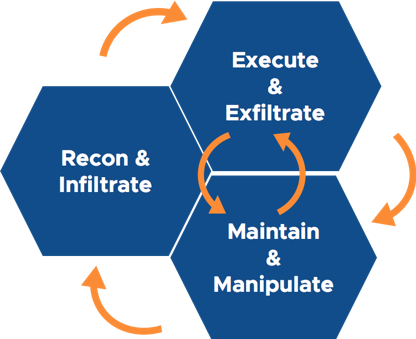
Let’s think like an attacker for a minute. They do some recon on your staff members on LinkedIn to find targets for a phishing attack, from which they succeed and land a piece of malware on an endpoint. Now that they’re in your system, they need to do more recon to learn what is running on the system, and what’s next to it to decide how they will manoeuvre towards their target — this is what we call an OODA loop (Observe Orient Decide and Act).
Figure 1 — An example of an attacker OODA loop. They will normally be performing multiple loops along their attack chain.
Lucky for us, not all attackers follow these steps. Many are seeking the quickest, not necessarily the most covert, way to the target — a weakness we can use to our advantage.
I often use the Spartans to illustrate this example, specifically how they choose their battle fields. In their most famous battle, the Spartans were able to battle a much larger army by reducing their enemy’s front; using their surroundings to bottleneck oncoming soldiers. Combined with their use of shields, long spears, and agile armour, the Spartans were able to defend and attack at the same time.
The ancient Greek historian, Plutarch wrote of the #Spartan phalanx, “It was a sight equally grand and terrifying”…imagine that, several centuries ago through today, as a result of its victories & Thermopylae it is acknowledged as one of antiquity’s greatest military formations pic.twitter.com/xflV4DyfYA
— John Trikeriotis (@spartanwarriors) January 12, 2018
Defenders can learn from the Spartans by designing systems to lure and/or direct attackers towards monitoring points and away from valuable targets. In effect, it’s another example of the importance of home-field advantage.
Flipping the cyber defence equation
For far too long defenders have given up inherent advantages and we need to take them back. Identifying and properly resourcing our assets and positions of power will ultimately give us the upper hand in our continual cat and mouse games with attackers. If we can do this, we will force attackers to be 100% right when they are inside of our environments.
Rick McElroy is Principal Security Strategist at Carbon Black.
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.