
AS-PATH prepending (ASPP) is a technique largely employed on the Internet to try to influence the decisions of other Autonomous Systems (ASes). The ASPP principle consists of inflating the path length by adding the local Autonomous System Number (ASN) multiple times in the AS-PATH, making it longer and thus less likely to be chosen by other ASes.
While initially intended to indicate backup routes, paths with ASPP have been selected as best routes and propagated by ASes frequently. To illustrate, on 1 April 2019, 29.4% (876K) of the routes seen on the Amsterdam RouteViews collector had ASPP. Such operations were performed by 12,782 ASes (out of 63,693 that appeared in the paths).
Although ASPP is beneficial for traffic engineering, it can compromise the security of Internet routing. More precisely, ASPP use can increase the risk of prefix interception attacks, as illustrated below.
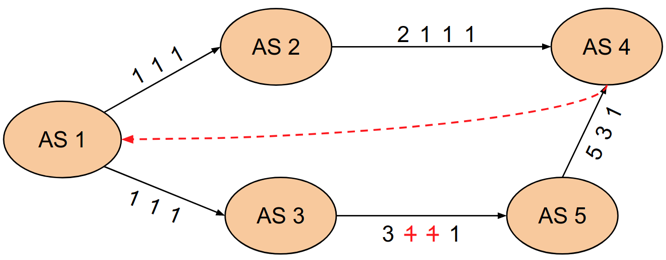
Figure 1 — Example of how ASPP can increase the risk of prefix inception attacks.
In the above example, AS 1 is announcing a prefix with ASPP to its neighbours, AS 2 and AS 3. Then, AS 3 partially or entirely removes the ASPP to create a shorter and potentially more appealing path to the other ASes, thus, attracting traffic destined to AS 1.
In this scenario, AS 3 could remove the ASPP as a strategy to maliciously inspect the flows, perform a Denial-of-Service (DoS) attack, or exploit economic aspects of its interconnection relationships (for example, increase revenue since more traffic will be sent using the tampered path). A configuration error made by the network operators of AS 3 could also lead to this scenario.
Is the Internet at risk?
While this scenario may sound hypothetical, during a recent presentation at RIPE 77, Cloudflare reported that they were victims of attacks exploiting the use of ASPP.
Different approaches have been proposed to improve routing security, including BGPSec and RPKI. BGPSec would be able to prevent such a situation, but it has not been widely deployed for a variety of reasons, including the need for modifying pieces of equipment and its overhead costs. RPKI has recently become more popular but is not capable of preventing the attack because the tampered route will continue to have a valid originator.
Learn more about RPKI via Security@APNIC
Is there anything we can do?
We at the Universidade Federal do Rio Grande do Sul are performing a longitudinal and global characterization of the ASPP to understand better the potential security issues of announcing routes with path prepending.
In our ongoing analyses, we have identified that ASes have different prepending policies that vary from the occasional use of prepending, to cases where the AS announces routes with ASPP almost all the time.
While we recognize that ASPP is a handy tool for network operators to perform traffic engineering, we advocate that the network operations community should strive to find a compromise between its traffic delivery requirements and routing security properties.
Leave a comment if your network was a victim of prefix inception attacks associated with ASPP or if you would like to learn more about our research.
Pedro Marcos is a PhD candidate at Universidade Federal do Rio Grande do Sul and lecturer at Federal University of Rio Grande, both in Brazil.
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.
