The following article is an excerpt from the APNIC Academy’s Juniper SLAAC/DHCPv6 Router Lab exercise. The APNIC Academy also features virtual labs for SLAAC/DHCPv6 using Cisco and Mikrotik routers, as well as full mesh routing environments for you to learn about BGP, OSPF, IS-IS, NetFlow, SNMP, NETCONF and much more.
Part 1: Setting up
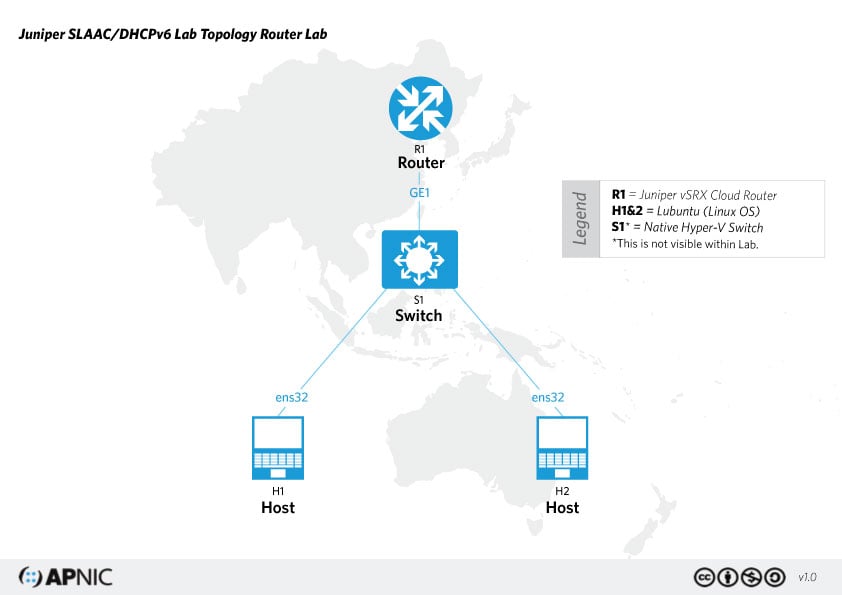
The network topology for setting up SLAAC/DHCPv6 is below. We will only be dealing with the configuration of Router R1 and Linux host H1.
Note: Your vSRX needs to be running in packet mode (that is, as a router, not a firewall) for this exercise. You can check this with the following command:
> show security flow status Flow forwarding mode: Inet forwarding mode: packet based Inet6 forwarding mode: packet based MPLS forwarding mode: packet based ISO forwarding mode: packet based ...
If your vSRX isn’t in packet mode, issue this command to enable IPv6 (and any other address families as desired) then commit and reboot.
set security forwarding-options family inet6 mode packet-based
Your router should have a minimal operational configuration. If you need help getting your router up and running from scratch, consult the Juniper SLAAC/DHCPv6 Router Lab.
Part 2: Configuring SLAAC
There are multiple ways to assign an IPv6 address to a host interface. In this section, let’s look at using Stateless Address Auto-Configuration (SLAAC). The router will be configured to advertise an IPv6 prefix. The host uses the 64-bit prefix from the router, and assigns the rest randomly or using EUI-64 to complete the 128-bit address.
With your router in configure mode, assign an IPv6 address to physical and loopback interfaces.
edit interfaces ge-0/0/0 unit 0 family inet6 set address 2406:6400:0:100::1/64 top edit interfaces lo0 unit 0 family inet6 set address 2406:6400::1/128
Configure the router to send router advertisements (RA) for the /64 prefix via ge-0/0/0.
set protocols router-advertisement interface ge-0/0/0 prefix 2406:6400:0:100::/64
Now verify the changes.
show interfaces show protocols router-advertisement
Optional – Set a trace for neighbour discovery (ND) events to help with troubleshooting.
edit protocols router-advertisement traceoptions set file ipv6-nd-trace set flag all
You may want to limit how much is logged by altering the ‘all’ flag to something more specific.
Show your changes before you commit.
show | compare
If you’re happy with the changes, then commit.
commit check commit and-quit
View the updated configuration.
run show configuration
Part 3: Verifying SLAAC
From your connected host, check that your interface has an IPv6 address. The address should look something like 2406:6400:0:100:x:x:x:x where the x:x:x:x ( the 64-bit interface ID) is generated randomly, as per RFC 4941.
If your interface doesn’t have an IPv6 address, toggle it.
sudo ifconfig ens32 down sudo ifconfig ens32 up
Once you have your IPv6 address, try pinging the router.
ping6 2406:6400:0:100::1
Now check the output of the following show commands on the router. It should show some statistics on messages sent and received.
root@R1> show ipv6 neighbors IPv6 Address Linklayer Address State Exp Rtr Secure Interface 2406:6400:0:100:d9:fd58:b528:39d3 00:0c:29:51:30:1d stale 811 no no ge-0/0/0.0 2406:6400:0:100:e01b:f078:3c2:2926 00:0c:29:ba:5b:af stale 1005 no no ge-0/0/0.0 fe80:6829:826e:fcfe:85dc 00:0c:29:51:30:1d stale 775 no no ge-0/0/0.0 root@R1> show ipv6 router-advertisement Interface: ge-0/0/0.0 Advertisements sent: 4, last sent 00:07:38 ago Solicits received: 1, last received 00:07:38 ago Advertisements received: 0 Solicited router advertisement unicast: Disabled
Since you have enabled an IPv6 ND trace on the router, you should see ICMPv6 ND messages being exchanged between the router and the client hosts. Issue the following command from the operational mode to check.
show log ipv6-nd-trace
or from JunOS shell, run:
tail -f /var/log/ipv6-nd-trace
You should see something similar to the log below.
root@R1> show log ipv6-nd-trace Nov 10 05:27:32 trace_on: Tracing to "/var/log/ipv6-nd-trace" started Nov 10 05:27:32 369657 ipv6_ra_ifIchange(Router-Advertisement): ifl 0x9e44d80 ifl ge-0/0/0.0 72 change 0. intf 0x9de2280
Part 4: Configuring stateless DHCPv6
In this part, we will configure the router as the DHCP server. The client gets an IPv6 address using SLAAC, then looks for a DHCPv6 server to get other information such as a DNS server address.
In configuration mode, update the RA to tell the client to look for a DHCP server for additional information.
edit protocols router-advertisementset interface ge-0/0/0.0 other-stateful-configuration
Configure the router as a DHCPv6 server, with a DHCPv6 pool named STATELESS-DHCPV6.
edit system services dhcp-local-server dhcpv6 group STATELESS-DHCPV6 set overrides interface-client-limit 10 set overrides process-inform pool STATELESS-DHCPV6
Bind the DHCPv6 server to an interface.
edit system services dhcp-local-server dhcpv6 set group STATELESS-DHCPV6 interface ge-0/0/0
Add DHCPv6 attributes, including DNS and lease time. These attributes will be passed on to the client.
edit access address-assignment pool STATELESS-DHCPV6 family inet6 set prefix 2406:6400:0:100::/64set dhcp-attributes dns-server 2406:6400::53 set dhcp-attributes maximum-lease-time 120 grace-period 3600
Verify the changes.
show system services show protocols router-advertisement show access address-assignment
And commit when you are happy with the candidate configuration.
show | compare commit check commit
Part 5: Verify DHCPv6
Toggle your host’s interface.
sudo ifconfig downsudo ifconfig up
Check that you are still being assigned an address by SLAAC — the address should look something like 2406:6400:0:100:x:x:x:x.
ifconfig
Verify that other information such as a DNS server address is being received from the DHCPv6 server.
cat /var/lib/dhcp/dhclient.leases | grep dhcp-server-identifier
Make sure you can still ping the router.
ping6 2406:6400::1
From the router’s operational mode, display the address bindings.
root@R1> show dhcpv6 server binding Prefix Session Id Expires State Interface Clinet DUID 2406:6400:0:100:a9a3:ba70:bc37:1887/128 5 109 BOUND ge-0/0/0.0 LL_TIME0X1-0x2379336c-00:0c:29:7b:f4:45
Display the DHCPv6 statistics. Confirm that DHCPV6_INFORMATION_REQUEST messages were received.
root@R1> show dhcpv6 server statistics Dhcpv6 Packets dropped: Total 0 Messages received: DHCPV6_DECLINE 0 DHCPV6_SOLICIT 0 DHCPV6_INFORMATION_REQUEST 10 DHCPV6_RELEASE 0 DHCPV6_REQUEST 0 DHCPV6_CONFIRM 0 DHCPV6_RENEW 0 DHCPV6_REBIND 2 DHCPV6_RELAY_FORW 0 DHCPV6_LEASEQUERY 0 Messages sent: DHCPV6_ADVERTISE 0 DHCPV6_REPLY 0 DHCPV6_RECONFIGURE 0 DHCPV6_RELAY_REPL 0 DHCPV6_LEASEQUERY_REPLY 0 DHCPV6_LEASEQUERY_DATA 0 DHCPV6_LEASEQUERY_DONE 0
Congratulations! You’ve now configured SLAAC and DHCPv6 on your Juniper vSRX. For more hands-on virtual labs, visit the APNIC Academy.
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.

Hi Sheryl
I’m working with a hardware appliance SRX300 and above and have searched a lot of sources for a suitable configuration for me and my IPv6 configuration on the SRX appliance. I thought thing should not be so much different when dealing with hardware or software appliances.
But the very first command you mentioned in the article let me struggle. Why do you set the vSRX to packet mode instead flow mode?
Is there a meaningful difference regarding IPv6 in leaving statefulness apart?
Regards
Illjuschin
Hi Sheryl,
Thank you for your guidance on IPV6. I tried SLAAC and there were no issues. However, with stateless DHCPv6, my laptop did not receive DNS information which i configured. It showed as 8.8.8.8(Juniper device not connected to internet).
Ethernet adapter Ethernet:
Physical Address. . . . . . . . . : 14-58-D0-17-D8-82
DHCP Enabled. . . . . . . . . . . : Yes
Autoconfiguration Enabled . . . . : Yes
IPv6 Address-2402:d000:1078:0:1658:d0ff:fe17:d882(Preferred)
Temporary IPv6 Address-2402:d000:1078:0:590d:8dfe:90e1:a6ec(Preferred)
Link-local IPv6 Address-fe80::1658:d0ff:fe17:d882%7(Preferred)
Autoconfiguration IPv4 Address-169.254.142.73(Preferred)
Subnet Mask-255.255.0.0
Default Gateway-fe80::f6bf:a8ff:fe4f:e680%7
DHCPv6 IAID . . . . . . . . . . . : 437541072
DHCPv6 Client DUID-00-01-00-01-26-8F-37-84-14-58-D0-17-D8-82
DNS Servers . . . . . . . . . . . : 8.8.8.8
NetBIOS over Tcpip. . . . . . . . : Enabled
Then i tried to troubleshoot with Wireshark and identified that, there is no reply for Information request from Juniper side. Client keeps send the Info-Req with contained “Requested Option code: DNS recursive name server (23)”
fe80::1658:d0ff:fe17:d882 ff02::1:2 DHCPv6 120 Information-request XID: 0xa52d31 CID: 00010001268f37841458d017d882
And dhcpv6 binding state also showing as “SELECTING” only.
run show dhcpv6 server statistics
Dhcpv6 Packets dropped:
Total 7
Bad Send 7
Advertise Delay:
DELAYED 0
INPROGRESS 0
TOTAL 0
Messages received:
DHCPV6_DECLINE 0
DHCPV6_SOLICIT 7
DHCPV6_INFORMATION_REQUEST 12
DHCPV6_RELEASE 0
DHCPV6_REQUEST 0
DHCPV6_CONFIRM 0
DHCPV6_RENEW 0
DHCPV6_REBIND 0
I tried to find solution for this, but i could not, appreciate if you can guide to fix this.
Thank you very much.
HasiiAth
Hello HasiiAth,
Can you provide the configuration on the SRX end ?
Thanks
Ruban