In February 2019, the Cyber Policy Institute (CPI) and APNIC agreed to work together on complementary activities, particularly in the field of cyber capacity building in the Asia Pacific region.
To start a conversation with the APNIC community, we are sharing some of the conclusions about a recent analysis conducted by the CPI of 193 UN Member States around their ‘national cybersecurity strategies’. In our report (CPI NCSS A Commitment to Development Feb 2019, and annex) we found much need for sustainable and development-oriented capacity building in this field.
Cybersecurity strategies can help economies achieve various goals related to the development of information and communication technologies (ICTs). As of February 2019, 106 economies had issued a cybersecurity strategy or an equivalent government-level policy instrument. This number also shows that half of the states are still to formulate one.
The purpose of formulating and issuing a strategy is to form and provide political guidance, choose between policy options, prioritize objectives, allocate resources, legitimize the direction and content of adopted policies, as well as to inform domestic constituencies and foreign audiences. Strategies are also needed to create deterring effects against malicious and hostile acts.
Cybersecurity strategies have become a means of political and technical continuity as well as crisis management. Having a cyber strategy can be considered a requirement of responsible state behaviour [1]. Major regional organizations such as the Association of Southeast Asian Nations (ASEAN), the Organization for Security and Cooperation in Europe (OSCE), the Organization for American States (OAS), the African Union (AU), the Shanghai Cooperation Organization (SCO), the North Atlantic Treaty Organization (NATO) and the European Union (EU) all have taken determined approaches to cybersecurity.
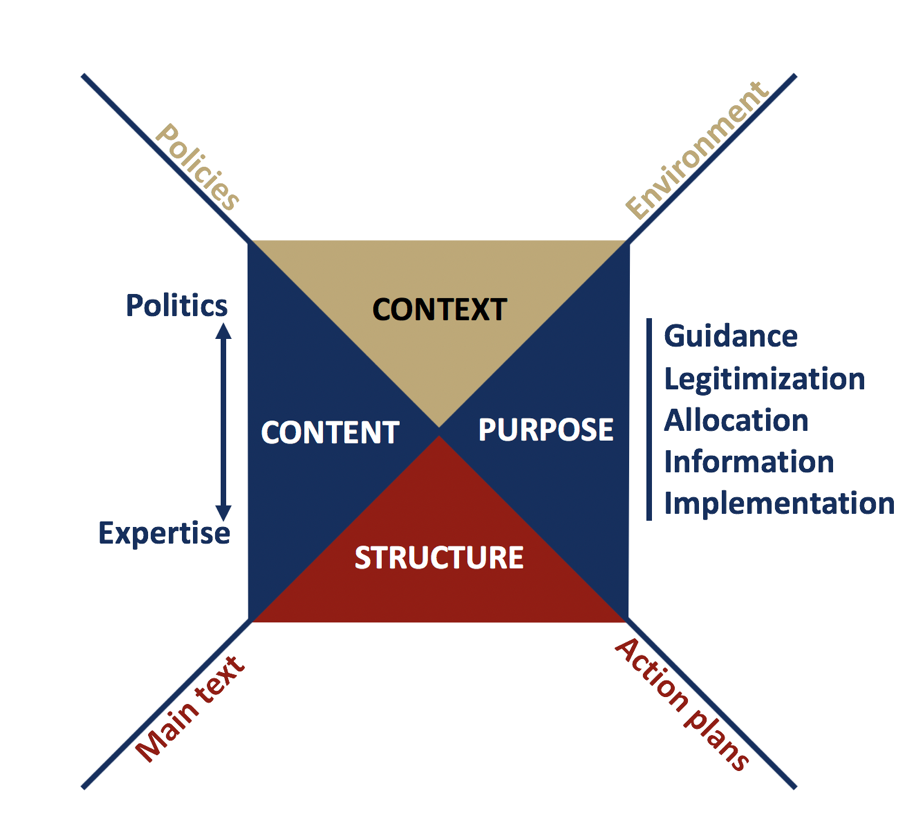
Figure 1 — National cybersecurity strategy conceptualized. Authors’ illustration.
Instruments such as issued legislation, government decisions, and development plans can fulfil the purpose of a strategy document. More important than the actual document is the implementation of the chosen policy: issuing a strategy is the start of improving a nation’s cybersecurity situation.
Strategies need to be tailored to the political, operational, financial and technological realities and stages of development of the actor and its environment. The art of strategy is not of adopting proven and universally acceptable measures but to design feasible approaches that will match with national ambitions, concerns and resources.
Thus, there cannot be any uniform direction or content to be followed or evaluated.
The need for national cybersecurity policy is usually argued as set of consolidated measures against threats. Many governments still lack a developed culture, confidence and competence of coordinated cyber policy planning and implementation. Strategy formulation is a process that can transform society.
Being able to formulate an implementable strategy requires thorough negotiations among domestic stakeholders. These strategy talks have to follow the purpose and direction of the chosen national and societal development policies and plans. They have to be cognizant of the domestic resources available. These discussions then lead to a national agreement between competing views and entities. To formulate a national cybersecurity strategy requires commitment: strategy without implementation remains an empty promise.
An obsession with security turns ICTs from the tools of peace and development into tools of suspicion and surveillance, and open societies into fearful societies. To avoid the negative consequences of securitization and to maintain the promise of ICTs, cybersecurity needs to be ‘societalized’. Societal and developmental objectives and human rights need to be the starting point and endgame of cybersecurity and the ultimate criteria of validity and relevance of the action to be taken. Cybersecurity is a means to an end, an engaging rather than an isolating process.
Without abandoning technical and political security requirements national cybersecurity strategies can become positive tools of societal development and instruments of international peace and regional stability. That is why a national commitment to international law and confidence-building measures are of particular importance.
Commitment to Development (C2D) is an approach that promotes cybersecurity as a societal and economic enabler. C2D methodology weaves values, development goals and societal realities into the fabric of cybersecurity policy. It enables nations to identify needs and capabilities, threats and risks as well as areas of potential domestic and cross-border cooperation. By doing this, the approach promotes interagency and cross-disciplinary dialogue and attention to the interrelationship of priorities, ambitions and resources. This approach also enables more fruitful discussion with the private sector and civil society as governments are empowered to communicate their visions on cybersecurity.
A proper assessment of cybersecurity strategies around the world entails analysis of not only the content and direction or implementation of governmental policies and programs, but in particular the impact-effect of these policies, that is, the achieved level and status of actual ICT developmental prowess and cybersecurity. Cyber affairs conceived as an ICT tool for peace and development deserve more serious and professional attention.
When measuring and ranking national cybersecurity strategies, ‘more’ is not always better. Just looking at this ‘maximalist’ criteria runs the risk of dismissing economies with lesser ambitions and capacities. As a result, the existing indices and rankings fail to point to the strategic objectives and the key priority areas of engagement. Over-prioritizing security tends to conclude that no economy is cyber ready but this undermines the international capacity-building agenda, including those who seek to support others.
There is no predetermined way, model or strategy to embracing ICTs in national development: economies and governments need to prioritize among competing but legitimate objectives, allocate scarce resources and take calculated risks based on their own assessments and realities. Strategy, by default, is contingent and calculative. Therefore, the approach of states to cyber affairs must be shaped by their distinct national and political culture, particularly in the development, use and oversight of ICT capabilities. Strategies cannot be not preordered, exported or imported.
Societal and developmental objectives are the starting points of crafting national information or cybersecurity strategy. Security-first approaches will be outsmarted, and security-alone approaches will become obsolete. Starting from and supporting wider national ambitions, the Commitment for Development is all about developing sustainable (and by default) cybersecurity.
[1] See in particular, the African Union Convention on Cyberspace Security and the European Union directive on network and information systems security (‘NIS Directive’) (2016/1148) stressing the need of their Member States adopting a strategy.
Contributor: Dr.Iur. Eneken Tikk
D.Soc.Sc. Mika Kerttunen and Dr.Iur. Eneken Tikk are founders of the Cyber Policy Institute, and Senior Research Scientists at the Tallinn University of Technology, Department of Software Science.
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.