
The Domain Name System (DNS) has been in use on the Internet for more than 30 years — now it is time for its worldwide maintenance that shall, for the first time in the existence of DNS, require coordinated actions from all operators of DNS servers and DNSSEC validators.
This article summarizes the crucial steps that operators of DNSSEC authoritative servers need to take to ensure that their users will not experience any difficulties following upcoming scheduled DNS maintenance.
What’s happening
Authoritative server operators should ensure that their name server implementation correctly responds to queries with EDNS extensions by 31 January 2019 at the latest.
In accordance with the published plan, major DNS software vendors will discontinue support for servers that violate both the DNS standard RFC 6891 and its predecessor RFC 2671 after 1 February 2019 (also for the first time in history).
In practice, this means that servers that do not respond to queries with EDNS extensions will stop functioning after 1 February for clients, and domains hosted on these servers will become inaccessible!
Read: Measuring .nz preparation ahead of DNS Flag day
How to prepare for changes?
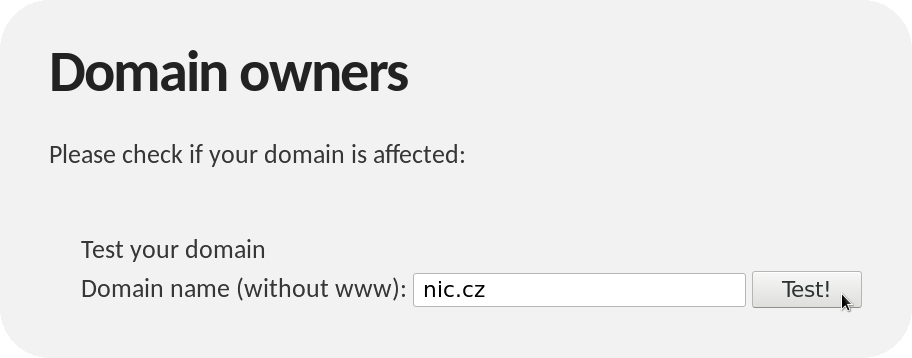
The first step is to make sure that your authoritative DNS server responds correctly. To do this, use the dedicated website dnsflagday.net with a testing tool. In the form, enter the name of any domain that is hosted on your DNS server:
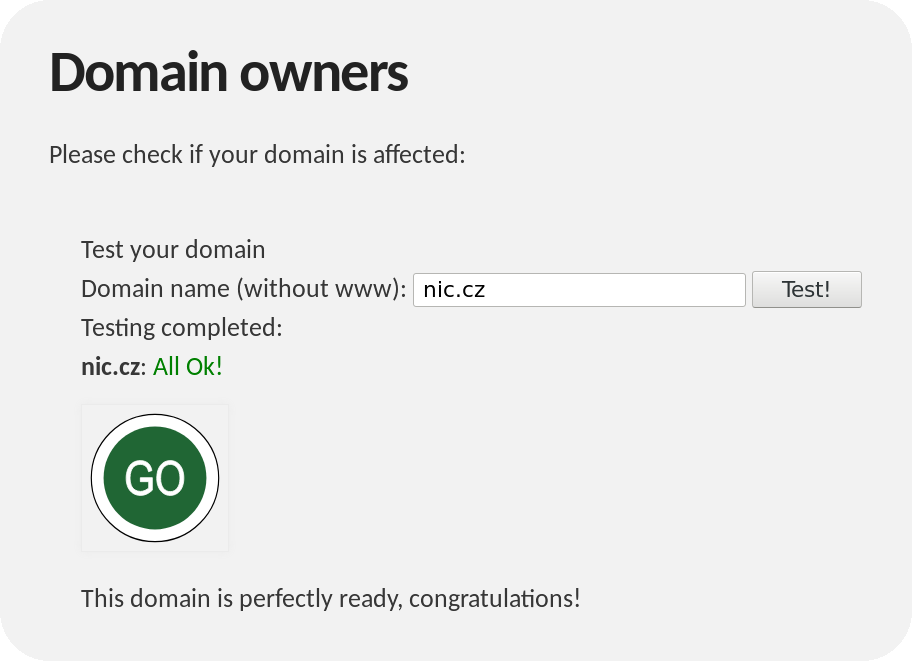
After clicking on the ‘Test!’ button, the vast majority of those reading this article will see the following message:
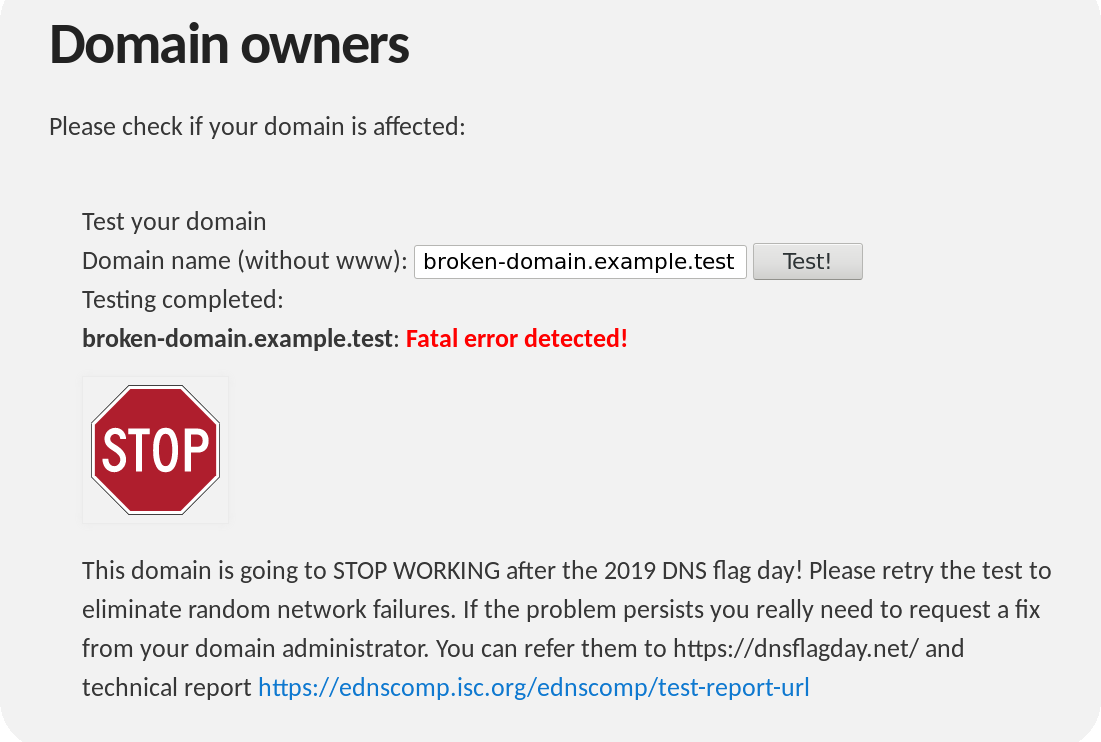
If you see this, no further action is required — your authoritative server is ready. If the testing tool finds a problem, it will let you know as follows:
Usually, problems like this can be solved by simply updating DNS software on the name servers hosting the tested domain. In rare cases, the problem may be caused by a too strict firewall that discards DNS queries with EDNS extensions.
See dnsflagday.net for more information along with the test tool and troubleshooting recommendations.
In conclusion, we would like to wish all operators of DNSSEC authoritative servers a smooth update of their software and seamless transition into the next 30-year DNS era.
Adapted from original post which appeared on CZ.NIC Blog.
Petr Špaček devotes his professional life to the DNS and leads the Knot Resolver project at CZ.NIC labs.
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.

Thanks for posting your valuable information with us & our readers.