
This post is the first in a three-part series surveying recent DDoS attack trends, and detection and mitigation techniques.
Global DDoS attack trends
The average size of Distributed Denial of Service (DDoS) attacks — where attackers seek to take down a website, application, or infrastructure by flooding it with requests — increased by 24% in 2018. In addition, the attack peak sizes have skyrocketed, as the memcached-based attacks that started in February 2018 ushered in the terabit era of attacks with a 1.7 Tbps attack in late February. The number of attacks greater than 300 Gbps increased as well, from 7 (in the first half of 2017) to 47 (in the first half of 2018), which is a 571% increase. However, the number of attacks worldwide declined by 13%, which shows that the attacks are more powerful and harder-hitting than earlier.
The reason for these trends is the rapid weaponization of new harder-hitting attacks, fuelled by the proliferation of booter/stresser services, which offer cheap DDaaS (DDoS-as-a-Service). For example, the memcached attack was weaponized and became available on GitHub only five days after the initial large attack.
Asia Pacific DDoS attack trends
The same trends are seen in the Asia Pacific region, where the average attack size increased by 23% in 2018 while the number of attacks declined by 4%. The number of attacks greater than 300 Gbps increased dramatically, from 5 (in the first half of 2017) to 35 (in the first half of 2018), which is a 600% increase. In addition, China experienced 17 attacks greater than 500 Gbps.
New DDoS attack trends
The majority of DDoS attacks are launched using attack vectors that have been around for a long time. As the majority of enterprises (and even some Internet Service Providers) lack even the most rudimentary DDoS protection, even a 15-year-old attack like a TCP SYN flood or a simple NTP reflection flood is sufficient to take these organizations offline.
However, as attackers often focus on high impact targets that take DDoS defence seriously, they constantly evolve new attack vectors that are designed to bypass or take advantage of limitations or vulnerabilities in traditional DDoS defence solutions.
This has resulted in a never-ending arms race between the defenders and the attackers, where the attackers come up with new attack vectors and the defenders scramble to create new defences to mitigate these new attacks. Then the attackers create new attack vectors and the cycle repeats itself.
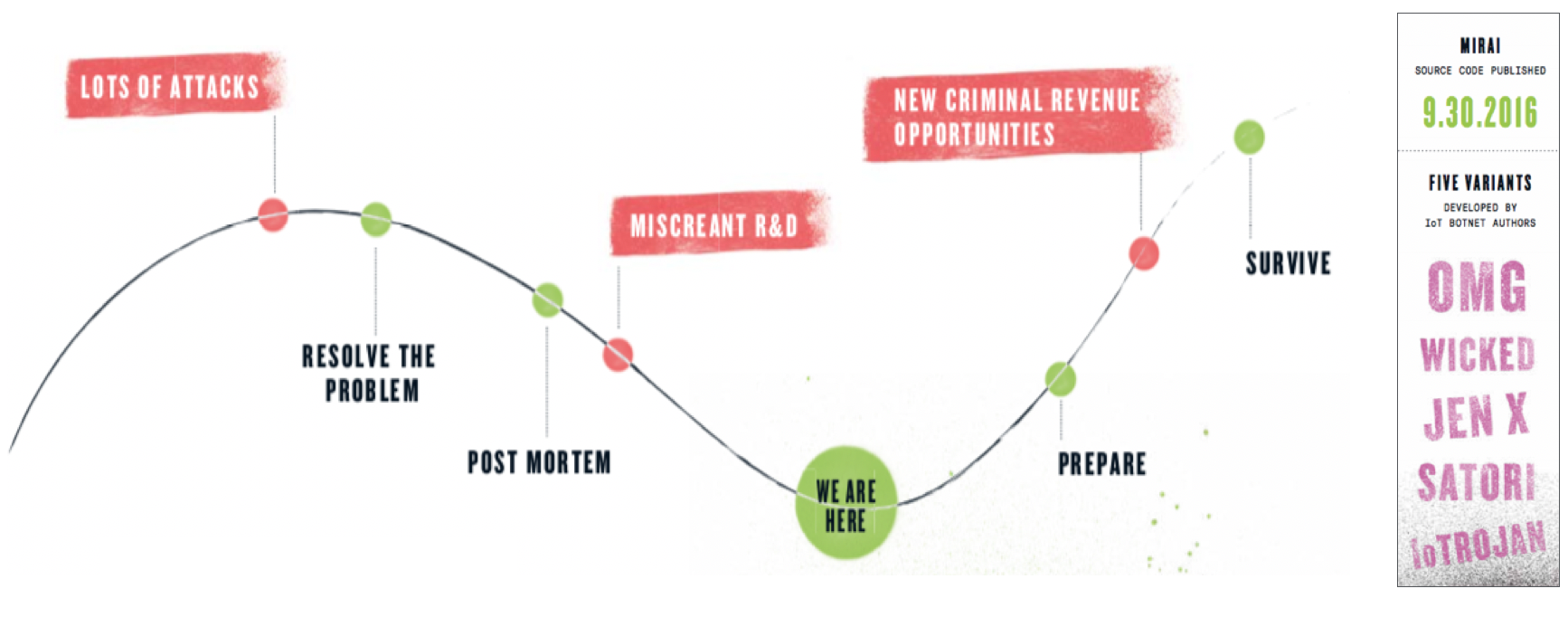 Figure 1: Since the release of the Mirai source code back in 2016, five new major variants have been released, each with new infection vectors and attack capabilities.
Figure 1: Since the release of the Mirai source code back in 2016, five new major variants have been released, each with new infection vectors and attack capabilities.
In 2018, there was a large increase in attack vectors that had previously only been in the hands of sophisticated attackers. Again, this was primarily due to these attacks being implemented in the booter/stresser services. However, a brand new attack type, the abuse of vulnerable memcached servers, was used in March 2018 to launch the largest DDoS attack seen in the history of the Internet: a 1.7 Tbps attack.
Carpet bombing
Carpet bombing attacks are a new variant of the more common reflection or flooding attacks, where instead of focusing the attack on a single destination, the attacker attacks every destination within a specific subnet or CIDR block (for example, a /20). This will both make it more difficult to detect the attack and also to mitigate it, potentially resulting in outages due to the flood of attack traffic across network devices and internal links.
In addition, these attacks are often fragmented, resulting in a flood of non-initial IP fragments, which can be tricky to mitigate. The attacker will often shift their attacks from one subnet (or CIDR block) to another, complicating the detection and mitigation even further.
The observed attack scale has been from 10 Gbps to 600 Gbps using DNS, SSDP (Simple Service Discovery Protocol), C-LDAP (Connectionless Lightweight Directory Access Protocol) and TCP SYN-ACK type reflection.
Detecting carpet bombing attacks
Detecting attack traffic using traditional flow-based detection that focuses on specific destination IP addresses will usually not work as the attack traffic will be spread across all IP addresses in the networks under attack. It will, therefore, be necessary to analyse traffic volumes crossing network boundaries or traversing specific network devices as this will show the broader attack volume. It will, however, be necessary to understand what normal traffic volumes look like, including regular spikes within them, in order to detect attacks.
Network traffic should, therefore, be profiled and average volumes measured on a regular basis (hourly, weekly).
Mitigating carpet bombing attacks
As carpet bombing attacks use traditional DDoS reflection type attacks or flooding attacks, they can be mitigated using the same approaches:
- Traffic from unwanted source ports can be dropped or rate-limited using infrastructure access lists (iACLs) or Flowspec.
- The source IP addresses producing the attacks can be blocked using iACL’s, Flowspec or source-based remote triggered blackholing (S/RTBH).
- Non-initial fragments can usually be safely rate-limited down to low values (1%). For DNS replies, an exemption should be made for your own DNS recursive infrastructure to avoid blocking large EDNS (Extension Mechanisms for DNS) replies. This can successfully remove up to 50% of the attack volume when dealing with fragmented attack traffic.
- Attack traffic can be diverted to Intelligent DDoS Mitigation Systems (IDMSes) but care must be taken to not divert too large a chunk of the attack traffic as it can be quite large when spread across entire network blocks.
Steinthor Bjarnason is Principal Engineer in Arbor’s Security Engineering & Response Team (ASERT) at Netscout.
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.
