Did you know that a BGP prefix hijack can potentially pollute 90% of the Internet within two minutes?
Of course, preventative measures such as Resource Public Key Infrastructure (RPKI) allow network operators to verify advertised routes using a system of digitally signed authorizations to prevent BGP anomalies from occurring in the first place. However, given RPKI adoption is still growing — and BGP anomalies are still common — network operators have a need to detect and respond to unusual routing behaviour in as short a time as possible.
Read: Measuring the adoption of RPKI Route Origin Validation
With this in mind, the creators of the Real Time BGP Anomaly Detection Tool (RTBADT) used a new technique to detect BGP anomalies in a matter of seconds. The team of researchers also created a complementary BGP Replay Tool (BRT) that replays BGP events at the per-speaker level and can compare behaviour across routing platforms.
The development of these tools was assisted in part by an APNIC Internet Operations Research Grant under the ISIF Asia 2016 grant scheme, awarded to the Centre for Advanced Internet Architectures (CAIA) at Swinburne University of Technology in Melbourne, Australia.
RTBADT — Real Time BGP Anomaly Detection Tool
RTBADT is designed to run on a border router, where it can detect BGP anomalies by monitoring a peering session with one of its BGP neighbours.
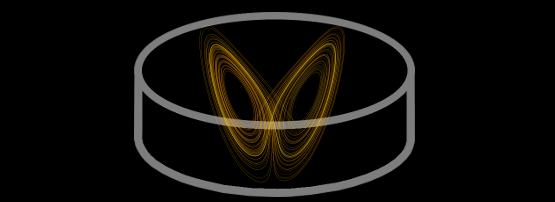
The CAIA team’s approach was “based on the use of Recurrence Quantification Analysis (RQA), a non-linear analysis technique based on phase plane trajectories”. RQA provides measurements such as Recurrence Rate (RR), Determinism (RET), Trapping Time (TT), and recurrence time of second type (T2).
RR is a calculated probability that a system state will recur after a number of time states. DET is the predictability of the system. TT can be used to measure how long the system is in a specific state, and T2 is used to measure the amount of time taken to move between states.
Having established that BGP exhibits recurrence behaviour, the team was able to detect BGP anomalies and other hidden anomalous periods that may have otherwise gone unnoticed. RQA’s ability to rapidly distinguish between normal and anomalous recurrence behaviours allowed them to detect anomalous events in near real-time.
Since RQA needs to be ‘tuned’ for time delay, embedding dimension and recurrence threshold, the tool includes a script to calculate optimal values.
RTBADT comprises four phases of operation: BGP collection (performed using Quagga); RQA calculation (where RR, DET, TT and T2 are determined); application of a moving average method to smooth recorded RQA measurements; and the detection stage, which performs a logical OR operation against measurements.
The tool was tested against a historical BGP misconfiguration event (replayed using the BRT tool), which was detected in 62 seconds.
Since the project was presented at APNIC 44, RTBADT has attracted interest from ISPs and vendors who want the ability to detect and mitigate BGP prefix hijacks as quickly as possible.
Bahaa Al-Musawi presents “Rapid Detection of BGP Anomalies” at APNIC 44.
BRT — BGP Replay Tool
BRT has the ability to replay BGP updates from public repositories such as Route Views, RIPE, or local log files. This allows ISPs and researchers to classify BGP traffic, understand behaviours at BGP speaker level, and investigate variations in behaviour between different router operating systems, such as Cisco, Juniper, and Quagga. It also enables network operators to perform forensic analysis on specific events after they have occurred.
BRT produces an output of human-readable BGP updates with Unix timestamps. The latest version (0.2) supports IPv6 thanks to the team’s patch of the Net::BGP Perl module, as well as dual homing and routing loop detection.
The tool was tested against generated BGP updates and past BGP instability incidents across Cisco, VIRL (Virtual Internet Routing Lab – a network emulation platform developed by Cisco), and Quagga platforms.
The CAIA team that produced these tools was led by Bahaa Al-Musawi, and included Professor Grenville Armitage, Associate Professor Philip Branch, and Rasool Al-Saadi. RTBADT and BRT can be downloaded here.
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.
