
Last week I travelled to Mumbai, India, to participate in SANOG 28 (South Asian Network Operators Group).
This was an unusual conference for me. My husband is the networking guru and he routinely attends NANOG meetings, for the North American group. I even had dinner here at SANOG with a woman who knows him. The closest I’ve gotten to NANOG is tagging along when the conference brings him to interesting or useful places (San Juan, Philadelphia) and doing some dinners with attendees who I know when I happen to be around. Plus, I usually go to open source or systems operations conferences. This was the first time I’d been to a conference focused on networking operations.
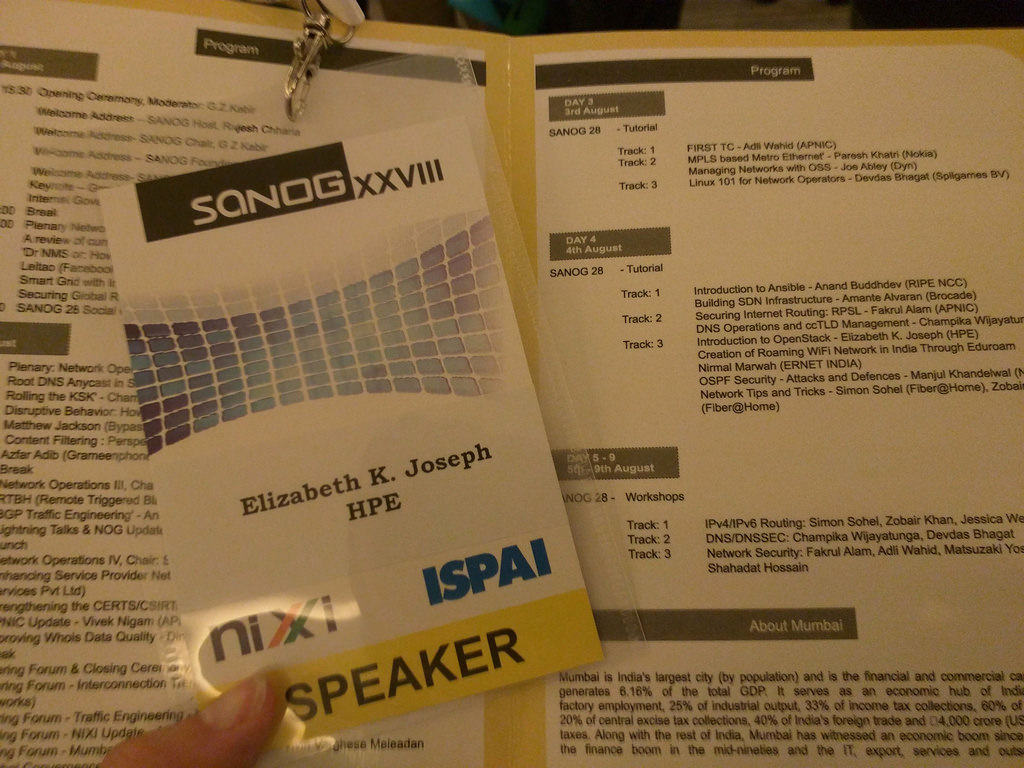
So what brought me to the other side of the world to this uncharacteristic-for-me conference? I was encouraged to submit a proposal to do an OpenStack tutorial, and it was accepted! I’m really grateful to my friend Devdas Bhagat who encouraged me to submit. He kept me in the loop all week with social activities and generally being around for me as I started interacting with a community that’s so new to me.
As the conference began, I learned that there have been nine SANOGs in India, and that this was the third time they’ve come to Mumbai. SANOG itself covers Afghanistan, Bangladesh, Bhutan, India, Maldives, Nepal, Pakistan and Sri Lanka, but given the venue, the first speaker spoke on some of the challenges confronting India specifically.
I enjoyed a keynote by Joe Abley of Dyn, who spoke on treating your technical teams well and making sure you’re doing everything you can to support them in their work and goals. He also mentioned the splitting of technical from managerial tracks. This is becoming increasingly common in the San Francisco bay area – they learned some time ago that engineering and managerial skills are very different and people should be levelling up on their own tracks. It’s a message that I’m glad is being spread more widely because as an engineer myself I can confidently say that I’ll be a happy person if I can continue moving up in my career to conquer more interesting technical problems without ever having to manage other people.

Speaking directly to the technical talks, we had Paul Wilson, the Director General of APNIC, who gave a keynote on the transition of IANA stewardship from the US government to ICANN. Speaking as an operations person who is aware of the broader Internet governance work because that’s where my servers live, I knew this transition had been in the works for several years but I didn’t know much about the actual plans or status. This presentation was the clearest, most concise summary of the plans, progress and status of the work they had been doing, and how close they are to finishing!
The most surprising part of this conference for me was the status of IPv6 in APAC, a view into which was presented by Byron Ellacott of APNIC. I had been under the naive assumption that given the explosive growth of network infrastructure in the region over the past several years, it would go without saying that these green fields be IPv6 capable. I was wrong. While IPv6 adoption in the US and a few countries in Europe has continued to grow, it remains low to non-existent in most APAC regions.
At a speaker dinner later in the week, I asked about this, and the consensus was a chicken and egg problem. A considerable amount of content is still IPv4, so until that moves to IPv6, providing capability for it doesn’t make sense. As long as adoption remains low (estimated 6.5% worldwide) and IPv4 is still supported, organizations don’t have an incentive to offer their content over IPv6. Instead, they’re taking extensive advantage of NAT and keep trying to find ways to get more IPv4 addresses (even if the maths is against them).
The whole discussion gave me some pause about the push for IPv6. Having a husband in the industry and working on a team that is eager to see strong IPv6 support in our infrastructure, I was an early adopter (I’ve had a AAAA record for my blog for years!). I thought we were all moving in the direction of adoption but are we really?
The second day began with a talk by Anurag Bhatia of Hurricane Electric about the status of the root DNS anycast in South Asia and how that impacts users. It continued with an update from Champika Wijayatunga of ICANN on the rotation of and changes to ICANN’s Root Zone Key Signing Key (KSK) and related Verisign Zone Signing Key (ZKZ), which I didn’t know a lot about but you can by checking out ICANN’s site on the topic. It definitely was surprising to learn that a rotation plan for the KSK wasn’t previously in place and that it’s remained the same since 2010.
These first morning talks concluded with a pair of talks that were amusingly juxtaposed: The first was by Matthew Jackson on how geo-restrictions in New Zealand lead to the development of technologies to get around the limitations and subsequent policy changes. As a native of the US, I’ve only rarely been impacted by region-blocking, but it has always been troublesome to me. As he said in his talk: “The Internet we built wasn’t meant to be geo-restricted.” Indeed. The talk that came after it was about ISP/network-level content filtering technologies. Hah!
“The internet we built wasn’t mean to be geo-resticted” via @mattnzl #SANOG28
— Elizabeth K. Joseph (@pleia2) August 2, 2016
As the day wound down, so did the conference. The closing event was held at the nearby Mumbai Cricket Association Indoor Cricket Academy and Recreation Centre. It’s the off-season, so no cricket was happening and the field was dark, but the inside of the building was beautiful. Though I’m not much of a party type, it was nice to meet a few folk and have some snacks before concluding my evening.
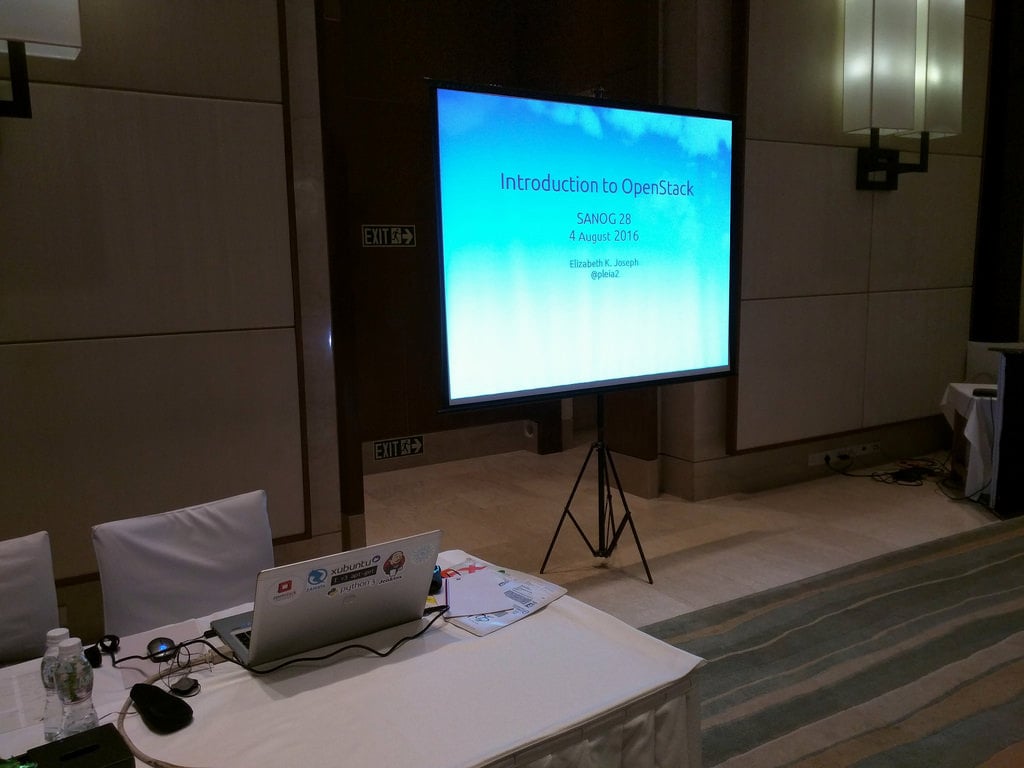
The week continued with tutorials. On Thursday, I presented mine: An Introduction to OpenStack. When my presentation was being evaluated by the committee in early July, I worked with them to tune the description to make an allowance for familiarity with Linux. Following acceptance, they strategically scheduled my tutorial the day after an Introduction to Linux hosted by Devdas.
As I wrote about in this interview, the tutorial was divided into three parts:
- Introduction to some OpenStack deployments
- Demonstration
- Building your own cloud
Since the audience was very networking focused (less open source, systems), what I sought to communicate was the basic concepts around OpenStack and some of the services it could provide. Then, by giving a demonstration of using different components through a DevStack install, I sought to give people a practical view into launching instances, adding block storage, metering and object storage. The talk concluded by doing a section very similar to my CodeConf talk back in June, where I explored the next steps as they begin their journey into OpenStack territory.
The tutorial was 90 minutes long, and I had a few very engaged members of the audience. Afterwards, I was able to talk to a couple of folk who previously had trouble separating all the Open* named projects, and were glad to learn more about OpenStack; so at least that one stood out. My publisher also gave me some coupons for the digital version of Common OpenStack Deployments so I was able to give those out to three participants, and pre-order discounts for the rest of the audience.
You can view slides from my tutorial, which include a link out to the DevStack demonstration instructions.
I think what I enjoyed most about this conference was simply being exposed to a new community. It was a real pleasure to be able to sit down at dinner with some of the brilliant people solving problems with these expanding networks. Beyond our discussions about the expansion of (or lack of) IPv6, I was able to chat with a DNS engineer at RIPE about infrastructure they use for the root server they run. I was specifically interested in how much organizational sharing happens between operators of the root DNS servers. His answer? Very little, intentionally. As a champion of open source infrastructures, it took some time for me to come around, but I conceded that in this instance it does make sense. By using different tooling and methodologies, the heart of the Internet is kept safe against inevitable vulnerabilities that arise in one tool or another.
Huge thanks go to the organizers of this conference and everyone who made me feel so welcome during my first visit to India. These past few nights I’ve had some great food and very friendly company of some great people from organizations whose work I admire.
Original post appeared on Elizabeth’s Blog PrincessLeia.com
Elizabeth Krumbach Joseph is a Linux Systems Administrator and gives talks about Open Source and Systems Administration at conferences around the world.
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.



Nice to read such an extensive review of the entire event. Thanks Elizabeth. And ofcourse, nice to know get your comments on my presentation – (ISP level content filtering technologies)