
What makes the Internet of Things (IoT) different from the Internet as we know it? Today’s Internet connects people, while the Internet of Things connects… things. What are these things? In the case of IoT, it means embedded computer chips that are attached to some physical device with networking capability.
On the Internet, scaling has always been a challenge. So far, it has actually worked pretty well. For instance, we went from keeping a list of all hosts on the Internet in a single file (HOSTS.TXT) to a hierarchical domain name system (DNS). In order to scale routing, we went from classful IP address distribution to classless interdomain routing (CIDR).
Right now, we have about 7.3 billion people in the world, about 3.2 billion of which are on the Internet. In the future, we expect many times that many IoT devices connected to the Internet. Eventually, the Internet will be expected to handle hundreds of billions or trillions of devices.
We already have thousands of times more computers on the Internet than when it was first deployed, but it still scales. Will it still scale to thousand of times more connected devices? Let’s look at the basic approaches to scaling and how these apply to the fundamental technologies on the Internet.
Horizontal Scaling
A common approach to scaling is to scale horizontally: you add capacity by adding more machines. (The “horizontal” in this case is contrasted with “vertical” scaling where you use more powerful machines. Such vertical scaling quickly reaches a limit because even the most powerful hardware in the world cannot handle the processing demands that we have today.)
Scaling horizontally is not always trivial and depends a lot on the technology involved. For instance with SQL it is difficult to use horizontal scaling, because of the requirements of the ACID (Atomicity, Consistency, Isolation, Durability) model. Financial transactions have similar problems, arising from similar requirements. The rise of NoSQL and blockchains are an attempt to adapt our requirements to allow this type of scaling by making informed trade-offs of reliability for performance.
On the other hand, horizontal scaling works quite well for web services, where each session is basically independent of all others, and users do not expect complete consistency in their browsing experience.
In the end though, horizontal scaling reaches limitations because it provides no way to get access to the data in many different locations.
Hierarchical Scaling
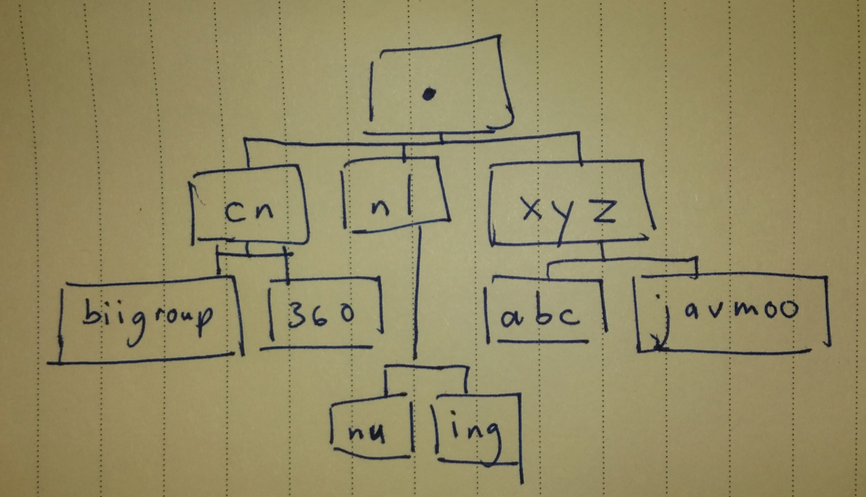
Another way to improve scaling is to introduce hierarchy, like has been done in the DNS.
In hierarchical scaling the data is organized in a tree, which is an old computer science technique that is used in many algorithms and data structures. This effectively allows one to use vast amounts of data without having to search through every item to get what you need. This core concept is the best way that we know to scale, and is at the heart of the fundamental technologies that make the Internet possible.
Three Internet Technologies
The Internet is based on three fundamental technologies: IP addresses, BGP, and DNS. Let’s look at these in more detail.
Addressing: IPv4 and IPv6
Internet addresses are how we assign a unique number to each endpoint on the Internet, used for location and/or identification.
Internet addresses are organized in a hierarchical manner. They are both managed in this way administratively by humans, and configured and processed in this way by computers. It turns the incredible number of unique numeric identifiers needed into a system that humans can easily manage.
It was recognized decades ago that the number of IPv4 addresses (232, or around 4 billion) would not be enough. Fortunately, we have had IPv6 for many years, and the number of available IPv6 addresses is enough for the Internet of Things. And even though the most common address assignment technology – stateless autoconfiguration (SLAAC) – requires a /64 per segment (half of the 128 bits in an IPv6 address), currently only a /8 of the available IPv6 address space has been given to the Regional Internet Registries (RIRs, including APNIC and four others) for use.
With IPv6, addressing all those future IoT devices on the Internet should be no problem.
Routing: BGP
Routing is how computers know where to forward packets to.
When thinking about scaling the Internet itself, we don’t really have to worry about internal routing. Organizations can use whatever routing protocol that meets their requirements, and if they need to they can also use the same routing system that the Internet itself uses: BGP.
BGP is the routing protocol that holds networks together. Unlike the other fundamental Internet technologies, BGP is not hierarchical. It hides information in order to make routing tractable, and therefore there is no ”true” view of the Internet, since every BGP router only has a local view of the routing table.
When we look at the future of the Internet, routing is the biggest unresolved scaling issue. So far Moore’s Law has managed to keep providing faster and bigger routers, so BGP has been able to remain as the only real routing protocol used on the full Internet scale. It is very much an open question whether this will continue to be the case. Software defined networking (SDN) is changing how routing is used, with both internal and external routing, but what the picture will look like in the future is not at all clear.
Naming: DNS
Naming is how both humans and computers talk about services on the Internet.
There are many past and present sources of names such as UUCP, X.500, mDNS, and Tor/i2p/GNUnet p2p. Internet naming is done through the Domain Name System (DNS). DNS itself faces many challenges today, for example securing the DNS system itself from attacks as well as providing reliable names via DNSSEC. Like many old protocols, it is very difficult to change the protocol itself, making evolution difficult.
Throughout the long history of the DNS, alternatives have been proposed and will continue to be proposed, for example DHT-based systems and the Handle System both have proponents. While in some cases such alternatives prove useful in specific applications, in general DNS remains the naming technology of choice on the Internet. DNS is the best. 😉
The Challenges for IoT
So, what are the challenges for the Internet of Things, if not scaling? There are three main areas here:
- Compatibility
- Obsolescence
- Security
Let’s look at these in more detail.
Compatibility
In order to make the most revenue, at the moment, companies strive for “vendor lock-in” which creates isolated systems and “walled gardens”. This is not a new practice – manufacturers have created non-interoperable systems since the dawn of interchangeable parts. Yet in spite of the obvious advantages to society at large, the commercial gain for any particular company of either ignoring interoparation or intentionally avoiding it means that the problem will never really go away.
In the case of IoT, we are seeing mature companies that have no experience with the Internet suddenly trying to produce products for the Internet. Even long-standing Internet companies with a history of cooperation and support for standards-based technologies often sucumb to the temptation to make proprietary technologies. The temptation for old companies that are entering this new market is going to be much stronger, and indeed if we look at the products available today the ability to interoperate is low, and even worse if you consider interoperation based on open standards.
Obsolescence
At the moment, there is no good solution for updating old hardware in the IoT. That is probably caused by the fact that economic models are mismatched: money is earned only at sale time, but devices on the Internet must be updated constantly if they are expected to continue to work.
While today’s consumer society tries to convince people to buy the latest gadget, traditional appliances last for many years. People keep old hardware, even as new products enter the market; they expect that their stove and air conditioner and doorbell will last a long time. While smart phones have trained us that we need to buy a new phone every few years, we are a long way from a world where we need to replace everything every few years – and indeed most of us probably do not want to live in that world.
In the non-connected world, appliance vendors make their money when something is sold, and then typically have low support costs for the products. While one can order a new knob for the stove, the manufacturer does not expect to have to invest serious engineering resources to maintain a product that they sold years ago and do not expect to make any more money on.
The issue here is that on the Internet we actually need constant updates and fixes to the software that systems use if we expect them to continue to work in the future. The cost of constant innovation is a huge amount of effort retro-fitting old systems so they can continue to work in the future.
There are possible solutions for this problem. If manufacturers were to embrace an open model then their products could have a life long beyond when the manufacturer was able to continue to spend money on maintaining it. Even today, open source software and “makers” are able to get old equipment to do incredible things many years after they were introduced.
No matter what the ultimate solutions for the problem are, the trick will be setting the financial motivations up properly to create a sustainable ecosystem.
Security
A closely related problem to obsolescence is security.
Even if we could assume that all IoT systems were sold with solid security systems (they are not), black hats are constantly finding undiscovered flaws and exploiting them to break into computers.
The current best practice for securing systems today is based on patching bugs. That works okay for phones and laptops, because they can automatically get updated, and they have a human user who can take measures to get the system fixed if things do not go well. But can this also work for unattended systems?
There are some prior examples of an unattended system that has been able to update, but they are all pretty extreme: space probes, wilderness sensors. This is not a totally new problem space, but it is certainly not a mature technology. A lot of systems are going to get hacked and used by bad guys before reasonable security measures become common practice.
Conclusion
IoT does not really bring any new scaling problems to the Internet. We can safely rely on the same techniques that have increased the Internet from a tiny handful of connected computers to something that reaches every corner of the planet.
IoT does come with some unique problems. They do not seem unsolvable at first glance, although it is not clear who is going to solve them. With luck, a combination of technology and business experts will cooperate with standards-makers and regulators so that we can use these cool new toys in ways that make the world a better place for the people in it.
Original post appeared on RIPE Labs Blog
Shane Kerr is a DNS researcher at the Beijing Internet Institute
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.

well informative post for its definition, this post tells all about it. Agree on the security, this will be the main issue of all. I remember the IoT events I joined, IoT security is the hot topic and it was really a fruitful event, looking forward to have more.
Internet moves the world !