
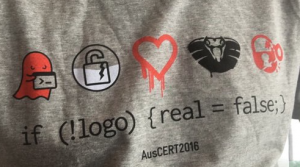
The AusCERT 2016 annual conference was (as expected) awesome! There was good content, interesting speakers, lots of opportunity to network with fellow information security professionals, a LEGO pit, and that special AusCERT2016 t-shirt not everybody will understand at first glance!
I was fortunate to be part of the presentation selection committee this year and the good news is that all of the talks are available online.
In the opening remarks, Thomas King from AusCERT gave a quick overview of their membership, types of incidents and some updates on their services.
It is good to see there is more awareness of the need to have incident response capabilities in various types of organizations.
Keynotes highlights
The keynotes on all three days were great. Christopher Soghoian spoke about the crypto wars between governments and tech companies. He highlighted that technology for enabling security and privacy can be turned on easily.
Securing communications helps to protect everyone across the board – law abiding citizens and governments. Efforts to undermine security by introducing backdoors and weakening the crypto used will likely backfire.
On the second day, Darren Kitchen gave an entertaining presentation on the conflict between security and convenience. Darren shared some examples of how, for the sake of convenience, operating systems trust external devices. This same trust relationship can be used to compromise computer systems.
I enjoyed listening to a few presentations in the Ubiquitous track. The first one was on securing health information by Farah Magrabi. Farah gave numerous examples of security incidents, as well as good insights into the challenges of securing health records and keeping up to speed with current best practices in risk management.
Have you been pwned?
Troy Hunt gave a good “behind the scenes” look at the service he runs – haveibeenpwned.com, in particular, on how he handles the reports, verifies the reported breach and the consequences these data breaches have on average users. He highlighted the need to have something similar to a mandatory data breach report to minimize these type of incidents and manage them better.
I think everyone enjoyed listening to the keynote by RSA’s Bill Duane on their experience handling the infamous 2011 RSA breach. Bill shared quite a bit about the attacks and methodologies. For me the main takeaway was how these breaches were impacting the life of security responders in organizations. I’m not going to give away spoilers, but I strongly encourage you to check out his presentation online.
Regarding security response teams, there were two presentations that caught my attention. The first one was by Hemamali Tennakoon from Sri Lanka CERT. She spoke at length about the challenges facing her organization in helping victims of cyber harassment and bullying incidents.
The other was by Chris Horsley from Cosive (and an ex-AusCERT, ex-JPCERT friend) who gave a very good overview on CSIRT maturity and the features they ought to have at each level. He also shared some thoughts about how teams with different levels of maturity deal with ever emerging jargon, such as ‘big data’ and ‘hunting’.
There are many other interesting talks and activities (like the Speed Debate) that I didn’t cover. But as mentioned earlier, you can find them online.
And last but not least, kudos to the AusCERT conference team for putting together another great event. I look forward to seeing you next year!
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.
