
My colleagues recently shared their views on the Internet Society’s (ISOC) 2015 Global Internet Report, which focuses on the Mobile Internet. It is an insightful report and I encourage you to read the executive summary; if you haven’t got the time to read the whole document.
In the report, privacy and security issues are cited as one of the main challenges for Mobile Internet. This is understandable given the increased growth of users. Criminals and other bad “cyber” actors will not let this opportunity simply slip away as mobile platforms become “the place” where people do business transactions, store data and interact with one another.
The Mobile Malware Scene
Malware is a menace and a serious threat to mobile users.
The term ‘malware’ refers to a variety of forms of hostile or intrusive software, including computer viruses, worms, Trojan horses, ransomware, spyware, adware, scareware, and other malicious programs. It can take the form of executable code, scripts, active content, and other software.
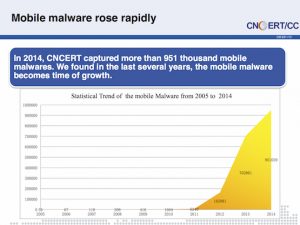
CNCERT collected more than 950,000 mobile malware samples in 2014. Most of the malware have monetary and privacy implications to users (premium number, SMS etc.).
The issue of malware has being highlighted many times, most recently at APRICOT 2015.
During the conference, TWNCERT shared how bad actors are abusing the popular smart phone messaging app Line to either distribute malware or scam users.
KRCERT/CC also discussed at length the response system the implemented as a result of increase in fraud cases committed via the smart phones. They managed to reduce the impact but warned that fraudsters are learning how to evade detection.
Part of the problem is lack of user awareness. Also, more than 300 third-party android app stores are not making things easier.
Collaborative Security
Mitigating the security challenges is critical, but won’t be easy. In the Global Internet Report , ISOC says they are promoting Collaborative Security as the way forward.
“Our approach stresses that everyone has a collective responsibility for the security of the Internet:
People are what ultimately hold the Internet together. The Internet’s development has been based on voluntary cooperation and collaboration. Cooperation and collaboration remain the essential factors for its prosperity and potential”
Last year, I blogged about my experience handling a piece of Android Malware targeting users in Malaysia. The malicious APK hosted on the cloud-hosting provider Dropbox, with the command and control (where information from the infected phones are stored) in Taiwan. This scenario in itself is a good demonstration why the call for Collaborative Security is relevant.
Last month, I was lucky to attend a presentation by Olaf Kolkman Chief Internet Technology Officer of ISOC, who discussed collaborative security in detail when he delivered his keynote address at the FIRST Annual Conference in Berlin, Germany. He said every player in the Internet ecosystem – developers, vendors, service/network providers, national and enterprise CERTs/CSIRTs, RIRs, experts developing standards and so on have a role to play and need to collaborate with one another.
To a certain extent I think a lot of people already get this and there is a lot of activities happening in this space. However, as always, more can be done.
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.
