
Gaining visibility into a target network from the outside is one of the first steps in breaching a network’s defences and has become one of the standard elements of criminal attacks.
The constant scanning of networks has become commonplace, not just by criminals, but also by organizations that sell access to the data that is collected. Gaining insight into the exposed footprint of your network has never been easier. You should assume attackers have an overview of your potentially vulnerable or misconfigured systems and understand what is exposed and exploitable.
What if you, as a defender, could have access to a public benefit, free to use, daily security report that provides an overview of some of your security risks? What if this data allowed you to understand what the criminals might see on your network? What if this data can highlight devices that are infected with malware? In fact, what if this data exposed devices and resources on your network you didn’t even know you had?
Shadowserver daily network report service
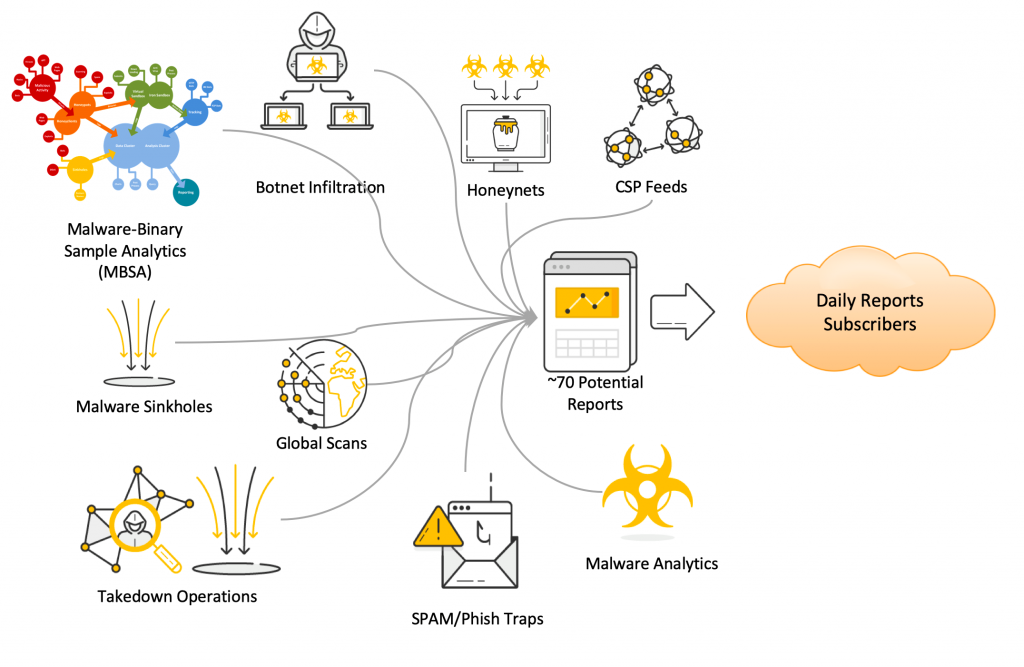
The Shadowserver Daily Network Reports service is a public benefit tool that provides up to 70+ free daily reports on your network organization. This includes data from daily IPv4 Internet scans, malware sinkholes, honeypots and network telescopes, the results of malware executed in sandboxes and many other sources. This data is shared for free with 132 National CSIRTs covering 173 economies and territories, and 6000+ network owners worldwide.
If you are an ISP, hosting provider, enterprise, SME, university, own a network of any size, or are responsible for a network, you can subscribe to these reports at no cost. If you are a National CSIRT you can get the data daily for your entire economy. Shadowserver can also provide reports on domain names as well.
Basically, any time Shadowserver collects something relevant to your network you will be alerted by our daily network reports.
How to leverage Shadowserver reports
Here are some examples of how Shadowserver daily network reports can be used by various organizations such as network owners or National CSIRTs:
Emotet — Emotet data is now part of the ‘victim notification’ process in malware takedown operations conducted by Europol and other law enforcement agencies. The Sinkhole Events infection report contains information on which hosts in the network are infected and have been observed contacting the Emotet command and control (C2) infrastructure. You can then take early action to clean up the hosts and investigate potential consequences of the breach and limiting damage.
HAFNIUM/Exchange — Shadowserver scanning can detect webshells that have been planted by HAFNIUM and other actors, after successfully compromising the organization’s Exchange servers. Action can then be taken to clean up the hosts, avoiding additional damage, and investigations can be started into the possible consequences of the breach.
Kick-starting security teams — Operators who understand security risks but don’t have a big security budget can use more than 70 free Shadowserver daily network reports to understand their visible attack surface, malware infections, botnets, misconfigurations, and vulnerabilities. A small team can translate vast amounts of high-quality security data into actionable insights, helping to clean up the network and prevent major losses.
Read: Skidmap and malicious DNS data mining
Well-resourced security teams — Operations with big security budgets taking good care of networks can also benefit. For example, if upgrading a firewall and access rules fail, an RDP service may become accessible from the outside. Shadowserver’s daily full Internet IPv4 scanning can quickly pick up the exposed service and the security team is notified, avoiding a possible breach.
CSIRTs — For a CSIRT seeking situational awareness of potential threats and vulnerabilities, Shadowserver’s free daily network reports can quickly provide a national overview. Daily actionable information delivered to the CSIRT helps identify the ‘hot spots’ of malicious activity. The CSIRT can quickly share the information with affected parties and help to patch any vulnerabilities.
Subscribing to Shadowserver reports
Subscription to Shadowserver reports is easy. All that is required is to fill out the contact form at The Shadowserver Foundation where you provide the details of your organization or economy (for National CSIRTs) — including the network space which you control — which Shadowserver then verifies. There is no formal agreement in place, submitting the form and completing a verification process is all that is required.
At the point of subscription, the reports can be customized by:
- ASNs for the organization
- CIDR Blocks
- Domains (including entire TLDs)
- Geolocation (for National CSIRTs)
All reports come in the form of CSV files but each report has a distinct format and can be delivered in multiple ways:
- Email (which can include a URL download link with CSV report)
- A webspace (unique per recipient) with multiple files that you can access
- An API (which also returns JSON objects)
Report preferences
You can specify your report delivery preferences at sign up. Most reports are offered by default but do consider signing up to the optional reports as well. Once set up, reports are generated every day.
The Sinkhole HTTP Events Report contains events (connections) to HTTP Sinkholes. Sinkholing is a technique where a resource used by malicious actors to control malware is taken over and redirected to a benign listener that can (to a varying degree) understand connections coming from infected devices. This report identifies the IP addresses from all devices that joined a sinkhole server but did not arrive through an HTTP referrer.
Since a sinkhole server is only accessed through previously malicious domain names, only infected systems or security researchers should be seen in this list. However, the sinkholes may also pick up web crawlers requesting malicious domains.
This report can come in two versions, one for IPv4 only connections, the other for IPv6 only connections.
Why are the reports free?
Shadowserver is an altruistic Nonprofit Organization (NPO) working for the public good. Our funding comes from the sponsorships, grants, and charitable donations of those who share our vision for a more secure Internet. These enable us to deliver daily network reports to anyone at no cost to the end user.
While our services are free at the point of delivery, we welcome any financial support or VPS/hardware donations and are open to collaboration on projects that continue to enable and improve these free public benefit services.
We believe any organization that wants to improve its security posture and better understand its security risk should subscribe to Shadowserver’s free daily network reports, thereby contributing to the improvement of the resilience of computer networks worldwide.
Our mission is to make the Internet more secure by bringing to light vulnerabilities, malicious activity, and emerging threats. Shadowserver is driven by the vision of a secure, threat-free Internet.
Sign up to Shadowserver’s reports here.
Piotr helps make things happen at the Shadowserver Foundation, coordinating large-scale data collection and analysis projects, and managing Shadowserver’s CSIRT relationships.
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.
