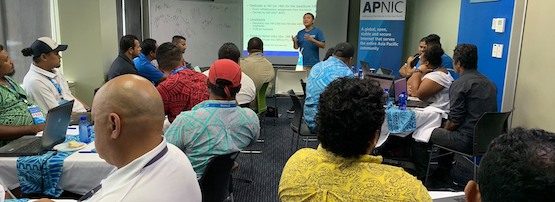
In June, I attended my first Pacific Network Operators Group (PacNOG) meeting, which was held in my home town of Apia, Samoa.
PacNOG is sometimes viewed as a meeting for only ISPs and those who have very big networks to manage. I guess this perception had made me question the usefulness of going in the past (having worked on government networks).
However, after attending and getting to know everyone, its clear that it’s for anyone involved in managing and monitoring networks who wish to not only learn best current practices and contribute their experiences, but also develop and maintain their connectivity (human and network), specifically its security, safety, and making it more streamlined (the “3 Ses”).
At the recent meeting, a lot of focus was on security, not so much the breaches by malicious actors but the misconfiguration of network solutions and server resources. A key takeaway was that we must start to implement documented processes when handling change controls. This will assist with preventing misconfigurations and assuring our clients, customers and peering partners that the configurations of resources we are administering are not only safe but are secure and streamlined.
Read: PacNOG 24: Trust, rumours and routing security
It was good seeing friends from the Pacific community who came and trained and shared their expertise in maintaining Internet resources at an international and regional level as well as a national and office level. With the Internet being faster and more dynamic than ever before, all levels must be considered to actually see how we all contribute to developing a safe, secure, and sustainable network; and in turn how this contributes to economic growth within the region.
This alone is a very good reason why we all should be part of PacNOG, as we all have some influence in the way we do our part, in terms of managing and monitoring our links and nodes.
Another key takeaway for me was that we must all push for clarity of understanding at decision-making levels. We can all talk technical but at the end of the day, someone with non-technical knowledge will need to decide how we can move forward with the technology. We must work with our leaders, both in our economies and in the region, to be united under a common understanding that ensures the safety and well-being of the Internet.
Read: How to talk about cybersecurity in your organization
Let’s tackle security like climate change
The people of the Asia Pacific region are more vulnerable to cyber attacks than any other region of the world. We are made up of many remote islands far from any well-developed economies with greater ability to defend against cyber-incidents. News of cities in more well-developed economies getting hit by ransomware and advanced persistent threats and needing to pay large ransoms may seem foreign to us at the moment but the time will come when it will be a reality in our small cities and towns too.
For the second time in a week, a Florida town has been forced to pay a ransom to hackers in order to regain control of government computer systemshttps://t.co/GFoePekVAB
— IT Pro (@ITPro) June 27, 2019
More so, the hyper-connected nature of the Internet also means we have a responsibility to safeguard our small networks, which can be used to cause damage to other networks far away — think DDoS attacks. In essence, us setting and following the good example of others is no different from our current battle with climate change.
Another great lesson learnt was that we must all audit ourselves — we all might think we know enough but there is always room to improve how we do things; also, we are all human, it’s in our nature to make mistakes and/or overlook things every now or then. We’ve all heard the stories from friends and colleagues about how someone forgot to enable something, or had missed disabling a setting that needed to be disabled, or allowed something, or denied a certain thing that caused something.
Read: Decay modes in cybersecurity capability and why they matter
We really need to have better control of our configuration processes, such as building and documenting configuration management manuals and operational control manuals. In some way, we need to ‘build backups of ourselves’, as one of my fellow PacNOG friends noted during the meeting.
My last takeaway from PacNOG 24 was we must be serious with our security, especially securing our border routers and nodes. If you have a BGP network please talk to APNIC about implementing Route Origin Authorization (ROA). For DNS, make sure you deploy DNSSEC. For data connection, use encryption and secure your traffic. For device authentication, use MTA or 2FA. And remember to be open-minded about all the security paths that could hurt you and your organization.
Learn more Security @ APNIC
From a national perspective, we must educate our citizens to be more security enabled and aware. If the physical layer is the first layers then users/humans must be layer 0.1. If we can make a change on that layer we will most probably see big changes in preventing major cybersecurity incidents. It’s like what I say:
‘Security is not so much a technical problem. It’s a people problem.’
Technology is not bad – it’s the wrongful use of technology that is the threat.
Overall, PacNOG 24 was really beneficial for me. I made a lot of new friends and I hope to continue to strengthen these links by further participating in future events and on the mailing list.
Suetena Faatuuala Loia is the Principal Information Communication Technology Officer for the Ministry of Health, Samoa.
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.
