
Malaysia enjoys a high percentage of women engineers in the ICT sector, making up about 50% of the workforce according to a UNESCO Science Report. However, cybersecurity positions are some of the hardest roles to fill — women in Malaysia account for only 21% of jobs in this industry.
According to a recent study by ISACA, 32% of organizations take over six months to fill a cybersecurity position due to the persistent skills gap and the difficulty of finding qualified candidates to fill these positions.
Raja Azrina has been in the ICT/Network Security industry in Malaysia for over 20 years. She currently works as an Information Security Advisor to two companies. Her current roles involve designing new security solutions and architecture, as well as providing advice to management. She also helps coach young leaders in the industry to sharpen their skills in cybersecurity.
“There are very few people who are willing to specialize in this area since it requires constant learning and keeping up with technology. Having a foundation in computer engineering gave me exposure to both hardware and software, and this became useful, especially with the growing network complexity and virtualization of systems today,” says Azrina.
Azrina began her career working for the organization that helped build the Internet in Malaysia. “My curiosity was to understand the Internet. I started with web programming and later jumped at the opportunity to join the network operations team. I was then tasked to evaluate network technologies, develop configurations, and deploy and commission network expansion involving 50 new points of presence in less than six months across Malaysia,” she says.
“My job at that time also involved system administration, network monitoring systems and authentication systems, which formed a good foundation for my next pursuit — information security.”
Azrina credits these early years of hands-on experience in network and system operations for providing her with a greater understanding to deal with cyber threats. When she was asked to initiate MyCERT (Malaysia Computer Emergency Response Team), she took it as a calling. “I pursued security certifications and conducted the first computer forensics analysis on a compromised host in 1997 under the directive of a local law enforcement agency. After over 10 years of running a cybersecurity organization under the government, I took up a new challenge by joining the industry with a greater focus on security for the critical sectors,” she says.

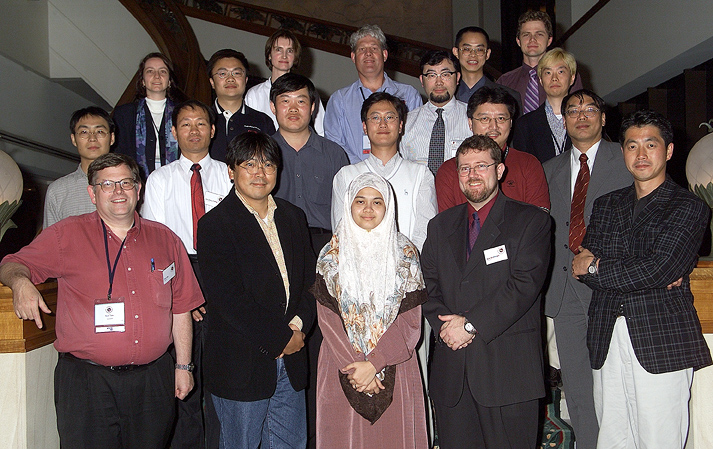
Azrina at the first MyCERT gathering with Computer Emergency Response Teams (CERTs) from the Asia Pacific, during the 9th Annual FIRST Conference in Bristol, England, 1997.
ICT and network security in Malaysia
Azrina says the level of ICT security readiness varies across sectors in Malaysia.
“Regulated sectors are more receptive to security improvements and show higher commitment and compliance. However, my hope is that baseline security requirements of Internet-facing services such as email, web services, and endpoint protection are given greater attention by organizations across sectors,” she says.

She believes organizations should include and demand security specification when acquiring technology and applications. “CIOs, CEOs and the Board of Directors play a key role in ensuring a risk-based approach is embedded within the organization.”
Azrina hopes that ICT solution providers and technology producers will design solutions with security in mind, and not as an afterthought. “We are sorely lacking in security standards and baselines for manufacturers of Internet of Thing [IoT] devices. We have situations where consumers end up installing smart home systems that can be hacked and cars with locking systems that can be compromised. I am hoping security practitioners engage more with multidisciplinary experts in building a future that is more secure and resilient.”
She believes her recent contribution to the field will bring a greater awareness to the effective application whitelisting technology to defend endpoint computers from falling victim to malware attacks.
Choosing cybersecurity as a career
In order to excel in cybersecurity, she believes you not only need formal training and certification, but also hands-on experience, curiosity, passion, and a good attitude.
“These requirements are not challenges for women. However, it is an open secret that the challenge for women is the need to put 110% more effort in their work, compared to men in order to have equivalent compensation. Thus, working in an environment that resonates high integrity and good governance will allow women to excel — choose the company you wish to work with wisely,” Azrina says.
Azrina understands the importance of having guidance in this field and is grateful to have had a towering mentor at an early stage of her career — the father of the Internet in Malaysia, Dr Mohamed Awang Lah. When asked what advice she has for young women trying to get into the ICT/Network Security industry in Malaysia, she says, “Be willing to learn, don’t be afraid to ask. Be good at routine tasks but be curious to investigate and research new issues and technology.”
Curiosity seems to have played a big role in helping Azrina get to where she is today. “What started as curiosity and exploration, later became a passion. I believe I found my ‘why’.”
She wants businesses who rely on technology for their core services to make security and privacy a key part of their decision making. She believes it needs to be made accountable at the Board level and hopes to “see more women in these key positions who have insights on technology and security risks to better steer organizations towards resiliency in the age of IoT and Artificial Intelligence.”
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.


A nice article by Erin Scherer. Really she inspires me and I hope the other women in ICT.