
Everybody reading this article is probably using an array of tools for protecting their smartphone, laptop, or enterprise server. But, very few of us are concerned about the security state of our router.
Even less of us are actively doing something about it. And most likely no one has an automated router protection system in place.
The story begins in early 2014, when a number of now infamous malware — namely, Moose, MrBlack, and TheMoon — started attacking home routers and harvesting information along with carrying out DDoS attacks.
The primary attacks were done taking advantage of default credentials on telnet/ssh, later expanding on exploiting the software vulnerability on such devices. At the same time, the trend of malicious activities became more mature; at first, it was only DDoS attacks but later malware could read and harvest the traffic that went through the router.
In October 2016, Mirai carried out the most intense DDoS attack of the century using vulnerable devices on the Internet, which included routers.
Read: Your questions answered about Mirai Botnet
The lack of mature protection technologies makes this a fertile ground for attacks. We believe that a compromised router provides significant new capabilities to an attacker, beyond those of a compromised end-device. By compromising a router, the attacker can have access to or block network packets going through it, steal cookies and session IDs to impersonate the user, or compromise their privacy.

Who is in charge of protecting us?
A system administrator makes sure all the clients are safe from any malicious activity. This includes making sure all computer systems have the latest version of the most relevant anti-virus software while the firewall protects them from any internal and external malicious activities.
Moreover, mandatory cybersecurity awareness courses helps prevent users from being victims of cyberattacks. While these precautions are important to take, are they thorough enough?
The answer is clearly no. We now see routers being compromised and adversaries have access to all the traffic that goes on in our homes, offices, or enterprises. System administrators, along with normal home users, are now faced with a new challenge to figure out if their router is infected and find a way to make it safe.
How can we secure routers?
From a security expert perspective, attacking and protecting routers is significantly different compared to laptops and desktops, therefore new methods and tools are needed.
The first challenge in this space is the limited CPU and memory resources in such devices, which limits both the malware developers and security solutions.
The second challenge includes routers having variable device configurations, which decrease the applicability of both malware and system analysis tools.
The former is a challenge for malware authors, while the latter is a challenge for any emulation capability, which needs to pretend to be many different configurations in order to get firmware and malware to run. Finally, many, if not most, router firmware is proprietary, and thus difficult to emulate.
RARE to the rescue!
Given the challenges of the diversity of various vendors’ firmware and plethora of different platforms, how can we analyze and profile the behaviour of these router malware?
To answer this, we developed RARE (Riverside’s Augmented Router Emulator), a systematic approach to analyze router malware and understand its behaviour in depth. We identified and collected 221 malware-targeting routers, which is clear evidence of how those of us in security are caught up with end devices, and are neglecting the importance of security in routers and switches.
The key novelty is the augmented operation of our approach, which fools malware binaries to activate irrespective of their preferred target platform. In other words, instead of trying to guess the right router platform for each malware, we start with a generic one and we carefully and repetitively ‘adapt’ it to fool the malware. This is achieved by leveraging two key capabilities:
- A static level analysis that informs the dynamic execution, and
- An iterative feedback loop across a series of dynamic runs, the output of which informs the subsequent run.
We provide an overview of our approach in Figure 2.
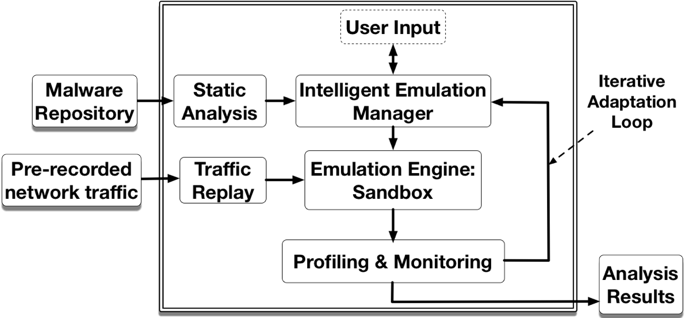
Figure 2 — Overview of RARE: A key novelty is the feedback loop (Iterative Adaptation Loop) that enables previous runs of the malware to inform the subsequent run in order to fool the malware to activate.
Using RARE, we successfully activated 94% of all malware, which included 88.8% of the obfuscated ones, and extracted useful information towards understanding and profiling the infected router’s behaviour. This includes identifying more than 200 unique IP addresses of C&C and reporting servers.
We collect malicious behaviours from the infected router, which includes: killing processes in the router in order to free up resources for themselves, adding firewall rules to make the router unreachable for users, and terminating user interface processes such as HTTP and telnet services. In some cases, the malware installs a new firmware and replaces the original one.
These findings are available upon request — please visit our website for more information.
This work is a first step towards developing a key capability for an under-served segment of devices. We would love to hear from and engage with the community of network administrators and ISP providers — let us know what you think and how you can help our quest.
Ahmad Darki is a PhD candidate in Computer Science at the University of California Riverside. His research is on developing techniques and tools to analyze malware.
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.

Yes, I trust my home router. My router is fully updated to the latest firmware released till now, and it is even protected with a WPA2 security key.
Yes, My router is up to date. and i am happy with my home router 🙂
Hi ,friends
This blog gives full Knowledege about Router. R810 is the lastest 4G Cat6 / Cat12 LTE CPE Router indoor base on Qualcomm chipset.
The R810 delivers maximum speeds of 4G LTE CAT6 / 12 300/400Mbps through its Gigabit Ethernet.It can also support RJ11 port with CSFB or VoLTE voice.
Its 2.4Ghz/5GHz Dual band 11ac WiFi capability allows this device to share internet access for up to 32 clients operations simultaneously.
Thanks
thanks for sharing…
Yeah, of course, I do trust on my router because I have a brand new router and it works really well.
Indeed, I confide in my home switch. My switch is completely refreshed to the most recent firmware discharged till now, and it is even ensured with a WPA2 security key.
Nice Post… Thanks For shearing us this informative post with us..
Nowadays security is the most important thing. Hackers always try to steal our information. we should always update our router firmware to the latest version. And always use WPA2 security protocol.