
Representatives from public safety agencies recently spoke at each of the Regional Internet Registries’ (RIRs) latest Policy meetings in a coordinated effort to share their views on the accuracy of whois databases. Grégory Mounier, from the European Cybercrime Centre, presented on behalf of the group of public saftey agencies on this topic at RIPE 73, both in the Plenary and AAWG.
September 2016 – Headquarters of the European Police Office (EUROPOL), The Netherlands.
Investigators of the European Cybercrime Centre (EC3), the cyber division of Europol, receive a notification from national cyber investigators that one major European chain of supermarkets has just reported to the police that their IT system has been compromised resulting in a serious data breach. Several million sensitive customer details have been leaked.
Internal investigations into the incident link the network intrusion to a SQL injection attack. After examining the log files, EC3 investigators identify one specific IP address as the indicator of the compromise.
As soon as the suspected IP address is identified, investigators scramble to find the ISP in allocation of this IP address in order to serve legal process to attribute the attack to a named subscriber. To do this they need to find the physical address of the ISP. It should only take a couple of minutes since that information is supposed to be available in the IP whois databases maintained by the RIRs.
However, the whois search shows that this IP address belongs to a /24 prefix, which was an assignment registered in the RIPE Database by ISP A to ISP B. After several hours of relentless research through the IP and DNS whois databases, but also in open source official ledgers of corporations, investigators end up with a rather confusing picture: ISP B to which the IP space has been reallocated to by ISP A, is potentially linked to three different individuals and five different physical addresses (three in the UK, one in Serbia and one in Belize). They also find one phone number in the US, one in Sweden and one in the UK. At this stage they have no certainty as to which address and which individuals they should send their legal order to.
This is why whois accuracy needs to be fixed
Accurate whois information is essential to attribute malicious online activities to and identify bad actors. But this case above illustrates the challenges encountered by individuals or institutions seeking information on providers holding resources that are used for abusive practices in the whois.
The accuracy of IP whois databases has long been a hot topic for discussion in the RIR communities. What’s the point of maintaining registry directory services if some of the information is outdated and unusable?
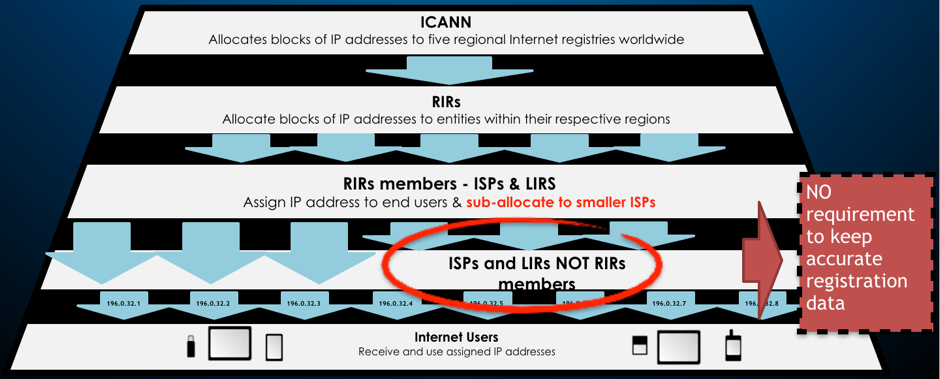
To address this issue every RIR community has adopted data accuracy requirements in their policies and contracts to ensure that RIR members maintain correct registration data (range, contact information, status and so on) at all times. Audit processes have also been implemented to check the correct execution of those data accuracy requirements.
Despite these efforts, it appears that whois accuracy is still a challenge that negatively impacts not only network operators who are the primary users of the whois, but also every other actor who has come to use the IP whois database over the years, to the extent that this has become a public policy problem in dire need of being addressed.
Whois accuracy will become an even more salient issue with the upcoming expansion of IPv6 since resource holders will likely have no need to come back to the RIRs to get new resources and RIRs will, therefore, lose their only available ‘stick’ to enforce accuracy policies with downstream providers.
Issue of current reassignment and sub-allocation policies
The main problem currently lies with reassignment and sub-allocation policies and the lack of appropriate enforcement mechanisms, which leads to misleading, outdated or false information regarding the last downstream provider, the ISP closest to the customer.
The contractual requirements for RIR members to maintain correct registration data are clear. However, if LIRs make sub-allocations to multiple downstream network operators, they remain contractually responsible for ensuring that the address space allocated to it is used in accordance with the RIR policies – including data accuracy requirements. But the policies remain vague on how these accuracy requirements should be implemented by the LIRs onto their customers.
How can the RIR community ensure that all IP sub-allocations to downstream ISPs are registered so that the entire chain of sub-allocations is accurately reflected in the whois? Should there be standard service agreements signed between the LIRs and their downstream customers to ensure compliance with accuracy requirement policies adopted by the RIRs? Should we look at possibly using the routing tables to determine endpoints instead of relying on contractual relationships?
These are the questions that a group of public safety agencies – comprising not only criminal investigators but also consumer protection agencies and civil law enforcement agencies – are looking into. They have started to work with the five RIR communities to develop a mutually beneficial policy on whois and they hope to address the problem of inaccuracy stemming from reallocations to downstream providers.
While the amount of abuse on the Internet continues to grow (spamming, IP address spoofing, DDoS attacks), users and network providers need to be able to obtain justice. The whois is an essential tool to identify harmful activities that undermine the stability and security of our Internet. The benefits of accurate and up-to-date registration data are straightforward: it would provide both public and private sector communities with an effective incident response and would significantly contribute to improving the trust and credibility of the IP space industry.
Public safety agencies cannot do it alone though. They need the RIR communities’ technical expertise and specialist knowledge to jointly devise policies customized to fit each RIR’s regional policy framework and which can realistically be implemented at minimal cost and for maximum efficiency.
Grégory Mounier is Head of Outreach for the European Cybercrime Centre (EC3), EUROPOL.
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.

interesting topic. But I am not sure about that IP address can connect to the Internet without correct information. For example, User B needs to advertise itself on any Router first (at the very beginning) and there would be physical connectivity from that router to User B-s own router. I think, having the investigation on physical connection could find the attackers position clearly. (whether it has different contacts points on registry)