
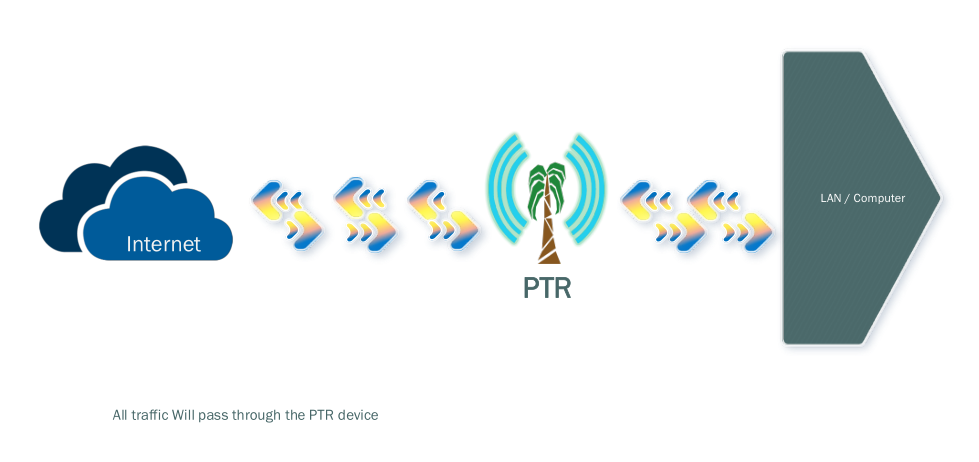
The Palmtree Router (PTR) project was born out of a few conditions that I had faced when I moved to a new location on the Samoan main island of Upolu, in a village called Laulii. Faced with a problem of getting Internet access on my small network, I needed a way to build a network gateway that could support Internet access where a fixed-line connection could not be reached. So the only way to get Internet access was through the mobile network.
Two problems were faced with this mobile network — most of the uplink devices were either a MiFi or a 4G router. Both devices were provided for a purpose and served those purposes only. The MiFi was only good for devices that had support for wireless and could only support up to five devices, but I had more than five devices needing an Internet connection and most of them only supported wired ethernet. In terms of the 4G router, the only problem was that it was very bulky and always needed to be plugged into a power socket.
Getting the idea
I had the idea of bringing the two technologies together by building a device that had the power and portability of a MiFi while at the same time had the capability of a 4G router, and so the Palm Tree Router (PTR) project was born. During these initial developments, another thought had come to mind, about making it safer and secure in terms of how it facilitated connections to the Internet.
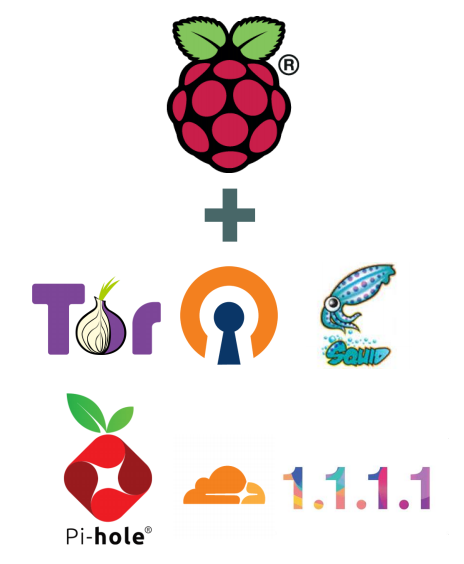
Fortunately, at the same time I was given the opportunity to attend many of the security workshops that the APNIC Foundation had coordinated in the region related to CERT development. Through this training I learned a lot about the importance of privacy and Internet security. It was this training that provided the motivation for the integration of some open source projects for Internet security and privacy into the PTR. These projects include Tor, OpenVPN, Squid, Pi-hole, CF_DoH, plus a few tweaks here and there related to networking and DNS.
Putting it all together
With this motivation, the PTR project started to come together in my bedroom. It was built in my free time, testing small tweaks here and there on the backend before the actual web interface was created. Looking for a device to build it on, I needed to find something portable that had mobility and the power to do more than just a router. I decided on using the Raspberry Pi board for this project, due to the fact that the it had I/O pins, allowing the project to be extended using modules that can be pinned in, to introduce additional capabilities.
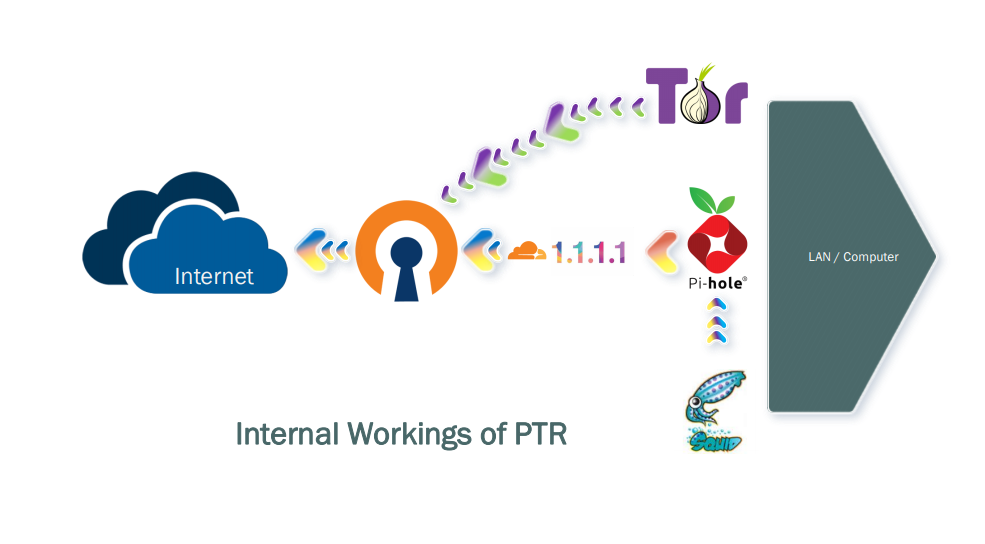
The project uses OpenVPN for VPN connections. All that is required is a profile configuration to be loaded onto the OpenVPN client, which can be done via the web interface. In this initial build, we have tried to keep it simple and easy, since most VPN providers provide a .ovpn file. This allows a user to connect to a number of different locations just by using the PTR device. One of the ways that I use my PTR is to connect my home network to my VPN infrastructure that has all my resources and tools.
Squid is another tool included in the PTR device, which allows it to monitor how Android and iPhone ads come through. By viewing the Squid logs we can identify ad links, and from here a user can choose to block those ads. If the PTR is sitting between your Internet provider and your network, this will allow you to block all the ad domains that you have added to the block tool. This domain blocking is the job of the Pi-hole, which also provides DHCP functionality to the PTR.
One of the great services that Cloudflare provides is DNS over HTTPS (DoH), which is made available through the PTR. All you have to do is configure your DNS settings to point the PTR device’s IP address on port 5053 (or set the PTR to use 127.0.0.1:5053) and your DNS requests will be made via HTTPS.
For those who want to get even more private, the PTR device also supports Tor. Tor is configured as a proxy, so all you need to do from the client side is set your browser or client system’s proxy setting to the PTR Tor proxy, then start to browse the Internet through Tor.
How can it be used?
The PTR project is more of a gateway to secure networks. It is is built to provide enough resources to get to your own secure network, and from there, you have to setup your firewalls and other lines of defence.
The PTR could be useful for communities — allowing them to share secure applications and resources by providing a secure connection to the Internet using only a PTR device. Many security companies are going down this ‘Security-as-a-Service’ route, but bringing our community to the same movement using open source software will help those who want to customize their security while providing access to a simple but effective tool.
What’s next for PTR?
At the moment, most of the financial support for PTR is from our own pockets, which has covered the costs associated with web portals and the devices themselves.
The project is pushing to build monitoring dashboards that can reflect the health of connections and traffic through the PTR device. The aim is to develop a cloud-based management tool that can be used to manage multiple PTR devices, which will assist in automating VPN device connection and connecting multiple locations to a central security hub through a customized VPN infrastructure.
A long-term hope is that the PTR can be used to build private security networks over the Internet. We are looking into using blockchain to manage PTR device identity for these types of custom networks.
The applications of this project are many, as it is more of an access gateway device that can connect you to anything you configure it for. With this in mind, one of our fears is that bad actors will use it for malicious purposes, which we are always thinking about ways to prevent.
The project is always happy to accept any type of support, including financial support and network training with regard to security and secure network protocols (particularly those related to remote connections). Join the project and let’s build a safer information sharing society.
Finally, I would like to thank the APNIC Foundation for all their great work in the Pacific in building security capacity and community, as the project was created as a result of their contribution and support.
Suetena Faatuuala Loia is the Principal Information Communication Technology Officer for the Ministry of Health, Samoa. Suetena holds a B.Eng in Computer Science and Technology from Northwestern Polytechnical University (NWPU), Xian, China.
The views expressed by the authors of this blog are their own and do not necessarily reflect the views of APNIC. Please note a Code of Conduct applies to this blog.

A fantastic way of private internet gateway. Thanks for sharing.
Niccccce.
Proud of you uso. Youve come a long way.
Great stuff Tena 🙂 Palmtree for the coconutwireless